Some files have more sensitive content than others — like copies of your ID, tax returns, medical records, legal documents, and family photos. In the wrong hands, your personal data can be misused, stolen, or exploited, leading to identity theft, fraud, or serious privacy violations.
One of the most effective ways to protect these confidential files is through encryption. In this guide, we’ll show you which types of files you should encrypt, why it matters, and how to do it step by step.
- Why should you encrypt your files?
- The right encryption makes all the difference
- Which files do you need to encrypt?
- How to encrypt files and keep them safe
Why should you encrypt your files?
Encryption means turning readable data (like a document or photo) into unreadable code — unless you have the right key to unlock it. Even if hackers get their hands on these files, encryption makes sure they can’t actually use them.
Some files contain personal, financial, or professional data that could be damaging if exposed, such as through a lost laptop, hacked cloud account, or stolen USB stick.
Encrypting sensitive files helps protect:
- Your identity, so it can’t be stolen
- Your money, so it can’t be drained
- Your privacy, so it can’t be violated
- Your work, so it can’t be leaked or copied
The right encryption makes all the difference
When choosing how to protect your files, it’s important to understand where and how encryption is applied, because not all methods offer the same level of security:
- Encryption at rest protects your files when they’re stored on your device, in a cloud account, or on a backup drive. If someone steals the storage device, they still can’t access the data without your key.
- Encryption in transit secures your data as it moves, like when you’re uploading to the cloud or sending an email. It prevents attackers from intercepting files over the internet.
- End-to-end encryption (E2EE) protects your files in both scenarios. It ensures your files stay encrypted from the moment you create or send them, all the way to the person or service receiving them, and that no one in between (not even the provider) can decrypt them.
Weak, outdated, or improperly implemented encryption can be exploited(новое окно) and often leads to data breaches. That’s why it’s important to use tools that rely on strong encryption standards like AES-256. The services you choose should also be transparent about how their encryption works and independently audited to prove they’re doing it right.
Which files do you need to encrypt?
Not all files need encryption, but certain categories — and the file formats that store them — should always be protected. This includes:
- Documents (PDFs, DOCX)
- Spreadsheets (XLSX, CSV)
- Images (JPG, PNG)
- Archive formats (ZIP, RAR) that may contain sensitive data
You should also always encrypt files containing:
Personally identifiable information
Personally Identifiable Information (PII), including Social Security numbers, passport scans, and driver’s licenses, is often stored in PDFs, scanned images, or spreadsheets. For individuals, a leak can result in identity theft or financial fraud. If you’re a business, exposing this kind of data can lead to legal action, regulatory fines(новое окно), and loss of customer trust — especially under laws like GDPR or HIPAA.
Medical records
Your medical records can include diagnosis reports, prescriptions, lab results, and insurance claims — often saved as PDFs, Word documents, or files exported from health apps or clinic portals. These files reveal deeply personal information that most people wouldn’t want shared without consent, such as chronic conditions or medication history.
2024 saw 725 healthcare data breaches(новое окно) affecting 500 or more people — the third year in a row with over 700 major incidents. For example, at a Finnish clinic called Vastaamo(новое окно), thousands of patients had their therapy notes and financial details exposed after the clinic failed to encrypt sensitive medical files in storage.
Financial records
Bank statements, tax returns, credit card details, and investment reports often live in files like PDFs, spreadsheets, or scanned documents. These contain valuable information that should be encrypted, like account numbers and income details.
Between 2008 and 2024, one of the biggest financial data breaches(новое окно) happened in 2019, when First American Financial Corporation leaked 885 million records, including sensitive financial and personal documents.
Legal documents
Wills, non-disclosure agreements (NDAs), real estate deeds, and legal correspondence — usually stored as PDFs or Word files — often contain highly sensitive personal and financial information that should be encrypted, such as names of beneficiaries and settlement terms.
For example, a cyberattack on the UK’s Legal Aid Agency(новое окно) exposed 15 years’ worth of personal data, including criminal records, national insurance numbers, birthdates, addresses, employment details, and financial information of people who had applied for legal help.
Business documents and intellectual property
Your work files can hold more than just to-do lists. Strategy decks, client databases, contracts, internal emails, source code, product designs, research data, and unpublished creative work can all contain sensitive or valuable information. These often come in formats like PPTX, DOCX, CSV, SQL, or design files like AI and CAD.
If leaked, they could expose trade secrets, damage your business, or allow someone else to steal your ideas. For example, in 2017, someone found an unencrypted USB stick(новое окно) on the street with sensitive files like airport security plans and VIP access routes. It led to a major investigation and showed how failing to encrypt a flash drive can create serious security risks.
Personal journals, photos, and private media
Your private files, including journals, family photos, videos, and voice notes, often capture the most intimate parts of your life. You probably wouldn’t want anyone else to access, let alone leak or misuse them — including for AI training. But if they’re stored unencrypted, especially in the cloud, they can be surprisingly easy to expose.
For example, in 2020, the photo printing app PhotoSquared(новое окно) left thousands of personal images and customer shipping labels completely exposed on the internet due to an unsecured storage server. Anyone with the link could browse, download, and view people’s private photos without a password.
Login credentials and passwords
Passwords are the keys to your digital life — from email and banking to cloud storage and social media. For example, in the 2015 VTech breach(новое окно), hackers accessed the personal data of millions of families, including passwords that were transmitted without encryption. This made it easy for attackers to obtain the passwords and access private messages, photos, and account details — even those belonging to children.
How to encrypt files and keep them safe
Here are some of the easiest and most secure ways to encrypt your files and other sensitive data:
Use encrypted cloud storage to store, back up, and share files
Start where most of your files already live — in the cloud. Unlike services like Google Drive or Dropbox, Proton Drive gives you end-to-end encryption by default, so no one but you can access your documents, photos, or backups. You can securely share files with others, let them upload their own files to your Drive, and manage or revoke access anytime.
How to encrypt and share files with Proton Drive:
- Sign up for a Proton Account if you haven’t already.
- Open the Drive web app(новое окно) and log in with your credentials. You can also set up apps for Windows, macOS, Android, and iOS.
- Drag and drop files into Proton Drive. Files are automatically end-to-end encrypted.
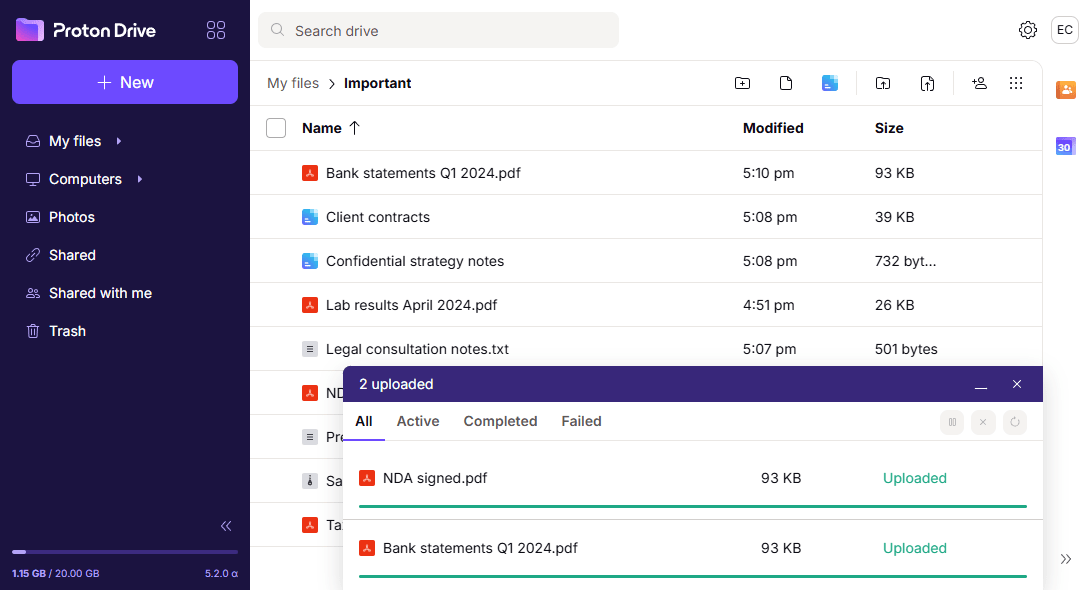
- Click the share button on any file or folder to share via email or public, secure link, then set view or edit permissions. In the case of public links, you can also add a password and expiration date.
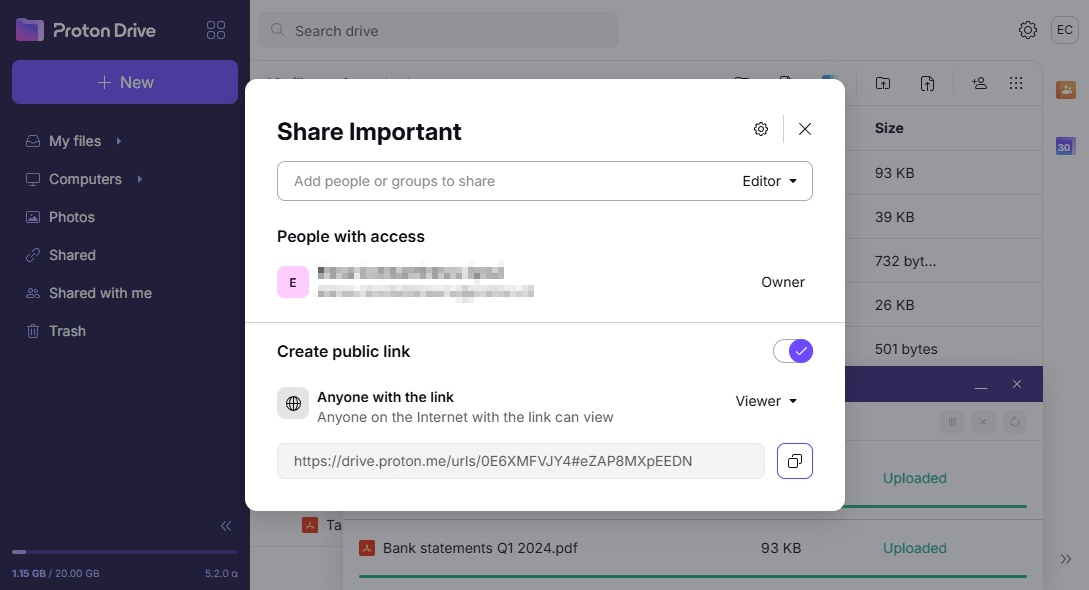
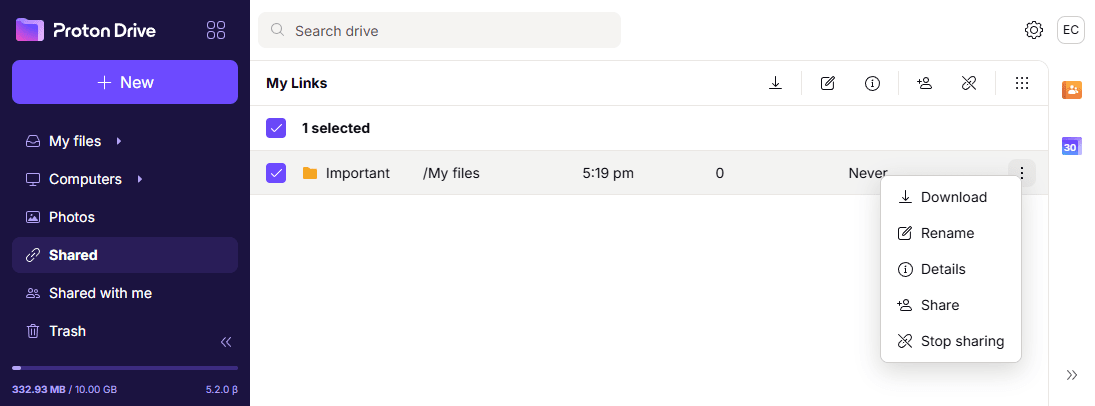
- Go to your Shared tab(новое окно) to revoke access anytime.
Use file-level encryption to lock specific files or folders
When you need to store files locally — like archives or backups of tax documents, legal papers, or medical scans — you can encrypt individual files or folders with a password.
For example, you can use 7-Zip to create a password-protected ZIP archive, or set up a hidden, password-protected container using VeraCrypt(новое окно).
Use full-disk encryption to secure everything on your device
If your laptop or external drive is lost or stolen, full-disk encryption ensures no one can access your files without your password. It protects everything at once, from documents and downloads to cached emails and saved logins.
On macOS, you can enable FileVault(новое окно), and on Windows, use BitLocker. Once turned on, encryption runs in the background and doesn’t change how you use your device — it just keeps your data safe by default.
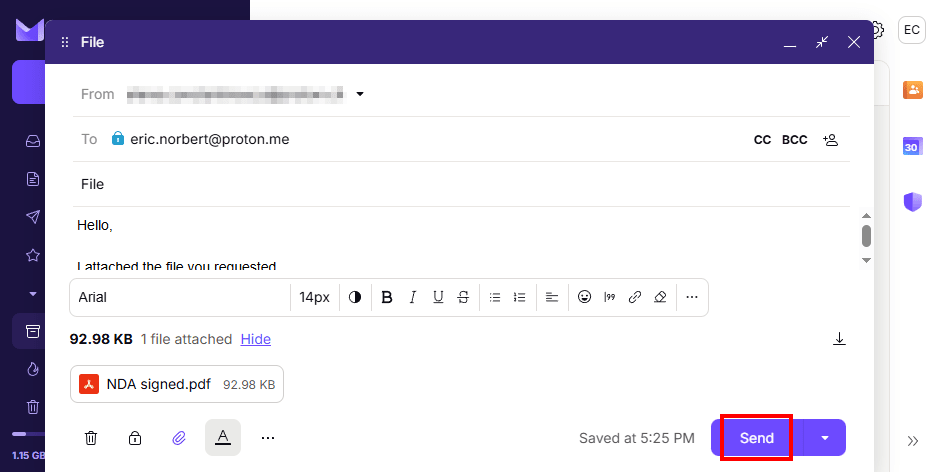
Use encrypted email for private conversations and file attachments
Email is often the go-to for quickly sending important documents, like medical records to a clinic or signed forms to an employer. Email providers like Gmail, Apple Mail, and Outlook don’t offer end-to-end encryption and may collect your data for targeted advertising. On the other hand, Proton Mail uses end-to-end encryption to ensure only you and your recipients can read your emails and attachments. You can also set passwords and expiring dates.
How to send encrypted emails and attachments with Proton Mail:
- Sign up for a Proton Account if you haven’t already.
- Open the Proton Mail web app and sign in with your Proton credentials. You can also set up apps for Windows, macOS, Linux, iOS, and Android.
- Select New message, then add a sender, subject, and message.
- Click the paperclip icon to attach documents, images, or other files.
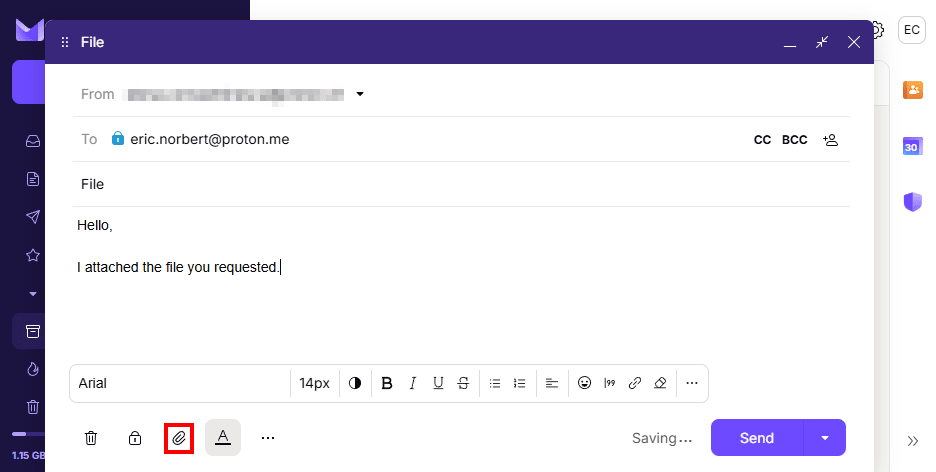
- Proton Mail automatically encrypts emails sent between Proton Mail users, so you can simply hit Send. If you’re sending an email outside of Proton, click the lock button to set a password.
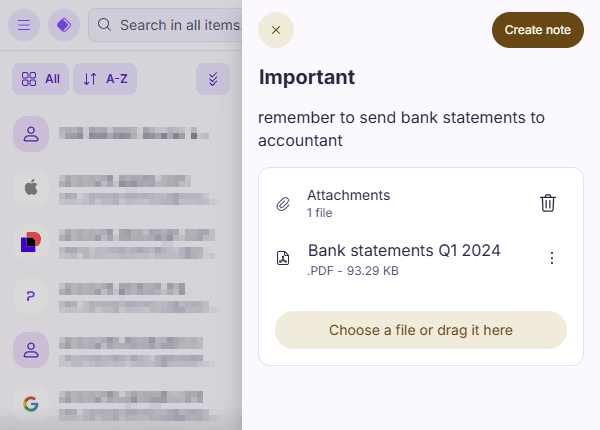
Use a secure password manager for logins and sensitive notes
Your passwords unlock everything — from your email and cloud storage to banking and social media accounts. But storing them in a browser or text file leaves them vulnerable. A secure password manager like Proton Pass keeps your credentials and sensitive notes safe in encrypted vaults, protected by a single strong master password.
You don’t have to remember every login, and you’ll never be tempted to reuse weak passwords thanks to a built-in password generator. Plus, you can enable two-factor authentication (2FA) for your Proton Account and saved credentials, store credit cards, identity details, encrypted notes, and file attachments, and share data with anyone.
How to protect your passwords and sensitive data with Proton Pass:
- Sign up for a Proton Account if you haven’t already.
- Open the Proton Pass web app(новое окно) and sign in with your credentials. You can also set it up on iOS, Android, Windows, macOS, and Linux, with extensions available for all major browsers.
- As you browse, Proton Pass generates and offers to save strong passwords, then autofills them when you return. You can also manually add information, such as payment info and notes.
Use a VPN to encrypt uploads and downloads on public networks
When you’re working on the go — sending files from a café, hotel, or airport — your internet connection might not be secure. A VPN (virtual private network)(новое окно) service like Proton VPN encrypts your online traffic, including file uploads and downloads, so no one can intercept your data in transit. Your online activity remains protected from hackers, snoopers, advertisers, and surveillance.
Proton VPN includes DNS leak protection(новое окно) to hide the websites you visit, a kill switch(новое окно) that stops all traffic if the VPN drops so your files stay safe, and Secure Core(новое окно) to send your connection through extra secure servers, protecting you from advanced network attacks.
How to encrypt file transfers with Proton VPN:
- Sign up for a free or paid Proton Account(новое окно). Paid plans give you access to advanced features like Secure Core.
- Set up Proton VPN on your device. It works with Windows, macOS, Linux, iOS, and Android.
- Launch the app and log in with your Proton credentials.
- Choose Connect to quickly connect to the nearest location, or select a country from the map. Now you can safely access the internet, browse the web, and transfer files.

Encryption isn’t just for tech experts or companies, but an easy and effective way for anyone to protect sensitive files from prying eyes, no matter the content.
Start with the files you use most often — the ones you regularly upload, send, or store. That might be a scan of your passport for travel bookings, an ID for public institutions, or a utility bill for verifying your address. These everyday documents are often the most exposed — and the most important to protect.






