Update: As of December 2016, Proton Mail has switched to a single password system as the default. The two-password mode described in this article is still available and supported, but is no longer the default.
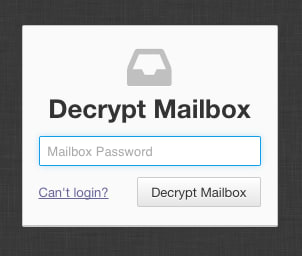
Proton Mail uses two passwords to secure your account: login and mailbox.
Login password
 (new window)
(new window)MailBox password
 (new window)
(new window)













