Learn about unsolicited messages sent in bulk by email, how to identify and prevent them, and how spam email filters work.
What is spam email?
What is the purpose of spam emails?
Are spam emails dangerous?
How do spammers get your email address?
Common types of spam
Spam email examples
How to stop spam emails
How to beat spam with additional email addresses (aliases)
How email spam filters work
How to ensure emails don’t end up in spam
Final thoughts
What is spam email?
Spam email (or just “spam”) is any unsolicited and unwanted messages sent out in bulk by email, usually for commercial purposes. The term “spam” originated from a Monty Python sketch(nova janela) about the canned pork product of the same name.
Spam is also known as “junk email”. While both spam and junk email may be unwanted and clutter up your inbox, junk email is usually something you’ve opted in to receive, for example, when buying something online.
All commercial email services, including Proton Mail, use automatic spam filters to shield you from the torrent of junk emails that would otherwise arrive in your inbox. Most spam should be sent automatically to a spam or junk folder.
What is the purpose of spam emails?
Spam emails are usually commercial with the aim of making money. While some are just annoying ads for genuine products, others are from spammers selling fake or dubious goods or services.
Others are downright malicious and aim to steal your personal information or infect your computer with malware(nova janela).
Are spam emails dangerous?
Spam emails are typically just ads that clutter up your inbox, so they’re nothing more than a nuisance. But malicious spam, such as phishing emails, can be dangerous.
Phishing is when fraudsters send you spam that looks legitimate but contains malicious links or attachments. The links may send you to websites that harvest your usernames, passwords, or banking details. Download the attachment, and you could infect your device with a virus or other malware.
It’s also worth noting the considerable environmental impact of both legitimate and malicious spam. In 2021, the total annual worldwide carbon footprint of spam(nova janela) was estimated to top 29 million metric tons of CO2e.
How do spammers get your email address?
Spammers can obtain your email address from various sources, but the most common ones are:
Data breaches
Databases containing email addresses are leaked or stolen with alarming regularity. They’re often sold to spammers or simply published on the internet.
Many databases also contain details such as passwords, so it’s always worth checking on websites such as haveibeenpwned.com(nova janela) to ensure your email address has not been included in such a data breach(nova janela).
Purchased lists
Unscrupulous websites and internet businesses sometimes sell lists of their customers’ email addresses to spammers, who then sell them on or swap them with other spammers.
Web scraping
Scammers often simply scrape the web for anything that looks like an email address (such as a text string with an @ symbol) and add it to a database.
Guesswork
Sending emails is basically free, so scammers sometimes send thousands of emails to semi-randomly generated email addresses (randomtextstring@ gmail.com or hotmail.com). It’s also easy to guess email addresses based on common names (such as john.smith123@yahoo.com).
From you
You often inadvertently get ads for genuine products after you’ve bought a product registered with a company online. This feels unsolicited, but you may have given your consent, tacitly or otherwise.
Under the CAN-SPAM act(nova janela) in the United States, companies can send you commercial emails unless you opt out.
In Canada (under CASL(nova janela)), the UK (UK GDPR(nova janela)), and the European Union (GDPR(nova janela)), you have to opt in to receive marketing emails.
Either way, be careful when you buy things online. You may have to check a box at the checkout to opt in or out to avoid being spammed.
Common types of spam
As spam emails are any unsolicited emails sent in bulk, they come in many forms — from legitimate ads to “urgent”, fake messages apparently from your bank.
Here are some typical spam messages that are fraudulent:
- Fake dating: You receive a message describing the man or woman of your dreams. But clicking on the link takes you to a phishing site or downloads malware.
- Money scams: You’re randomly asked to help transfer a massive sum of money from abroad in return for a cut of the cash (for example, the so-called Nigerian prince scam(nova janela)). But you must hand over your bank account details or pay a “processing fee” to get it.
- Prize winnings: You have won a sweepstake or lottery and need to collect your “prize”. But the link is malicious: It’s just a way to steal your personal or bank details.
- IT warnings: Your device has been “infected by a virus”, or your “account has been locked”. You’re then urged to pay for a (fake) antivirus solution or click on a malicious link “to verify your account”.
- Health care scams: You’re offered a miracle cure for a chronic disease like cancer with a 30-day money-back guarantee. But the drug is fake, and you never get your money back.
In general, if an email offers you something that seems too good to be true, it probably is.
Spam email examples
A lot of spam emails are just ordinary ads. While annoying, they’re not malicious and don’t pose any threat.
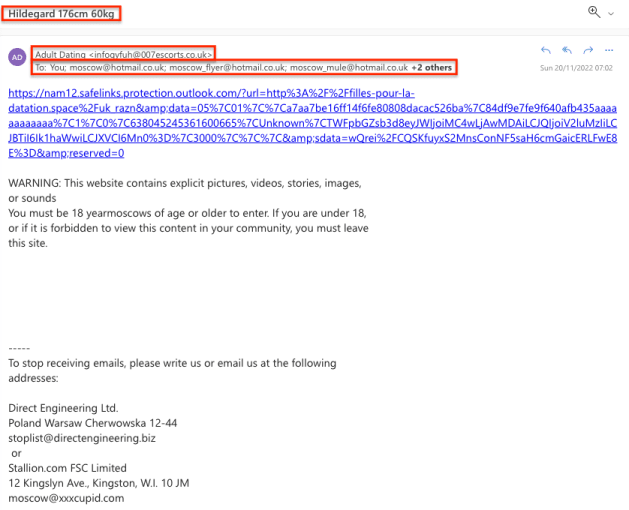
Below is one that is clearly not genuine and likely to be malicious. Apart from the dubious subject and sender (Adult Dating), the message has been sent to a random list of Hotmail addresses beginning with the word “moscow”:
Below is another spam message that looks much more convincing — apparently an important email from PayPal. But there are at least five signs that it’s fake:
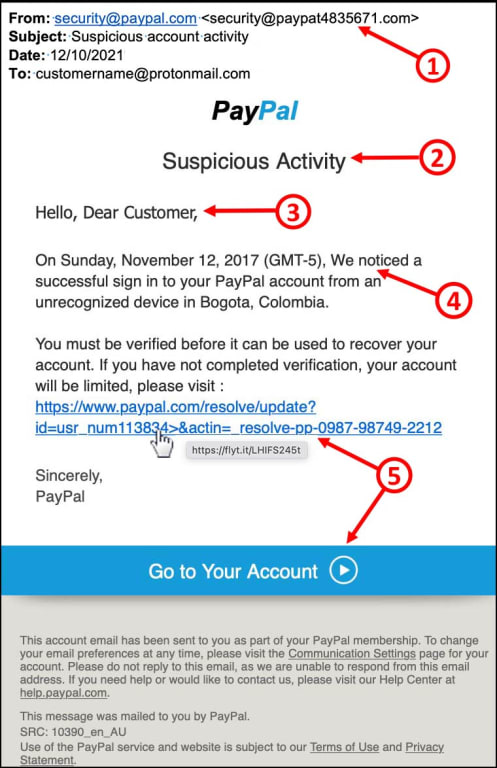
- Unofficial sender’s address: The sender in the From: field is “security@paypal.com”, but the following email address is actually <security@paypat483576.com>. The unofficial address “@paypat483576.com” instead of “@paypal.com” is a good sign the message is fake.
- Urgent requests, threats, or prizes: Phishing emails often pretend your account has been compromised. They ask you to take urgent action to “verify” or “confirm” your personal details or your account will be suspended or closed. Or they report a pleasant “surprise”: you’re due a tax refund, a lottery win, or a “special offer” that’s only available for a limited time.
- Generic greeting: While legitimate emails usually greet you by name, like “Hi Alice” or “Hello Bob Jones”, fraudsters often start with a general greeting like “Dear Customer” or “Hi” followed by your email address. Or they may use no greeting at all.
- Grammar or spelling mistakes: Scammers are not always the best writers, so look out for errors. Here it’s a simple capital letter “We” in the middle of a sentence, or it may be a company name misspelled: “Pay-pal” instead of “PayPal”.
- Links, buttons, or unsolicited attachments: Phishing messages often invite you to click on a button or link to enter personal information or make a payment. If you’re using a computer, hover your mouse over the link (don’t click!), and you’ll see the URL address (https://www.flyt.it) is different from the link (“https://www.paypal.com”). Or messages may contain an attachment, like a fake invoice, containing malware, which infects your computer when you download it.
With Proton Mail, you can use link confirmation to check external links before you open them.
All the above are clear indications of phishing, but not all malicious emails look so fake. Nowadays, some look genuine, so don’t click on links in unsolicited emails.
How to stop spam emails
While you can’t stop spam emails from being sent, there are ways to minimize the amount you receive and prevent them from clogging up your inbox:
Report spam
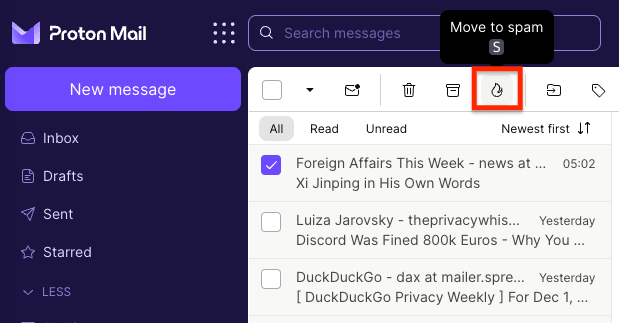
Most email providers have a “Mark as spam” or “Move to junk mail” option. With Proton Mail, if you select “Move to spam”, the message will immediately be sent to the spam folder and the address added to your Blocked list.
Never interact with spam
If you receive spam, you should never click links, download attachments, or reply. Responding to spam will alert the spammer that your email address is active, and you’ll likely be targeted with more spam!
Don’t try to “unsubscribe” from spam
Most legitimate emails come with an “unsubscribe” link to stop future messages. With Proton Mail, you can use the Unsubscribe from mailing list button. But with spam that’s not from a legitimate source, clicking on “unsubscribe” will likely just confirm your address is valid and result in more spam.
Keep your personal email private
Don’t publish your personal email address (or other personal information) online. Spammers often scrape the web and collect anything that looks like an email address to target with spam.
Use spam filters
All commercial email providers use automatic spam filters to reduce the amount of spam that reaches your inbox. With the best email providers, like Proton Mail, you can also use custom filters to manage spam. This is particularly effective when used with additional email addresses (see below for more).
How to beat spam with additional email addresses (aliases)
You can reduce the amount of spam that arrives in your inbox using additional, disposable email addresses, also known as aliases.
+Aliases
With Proton Mail, you can create an unlimited number of +aliases using the “+” symbol after the username in your email address.
There are two ways you can use this to defeat spam:
- Use a +alias whenever a suspicious website (or just one you have no wish to hear from again) asks for your email address. For example, alice.user+spam@proton.me. You can then create a custom filter to automatically send all emails sent to that address to your spam folder.
- Use custom +aliases for each website you give your email addresses to. For example, you could use something like alice.user+washingtonpost@proton.me for your Washington Post subscription. If you receive an email to this address from anyone other than the Washington Post, you will know they either sold your data or experienced a data breach.
Additional addresses (aliases)
As with +aliases, you can also create completely new additional addresses (aliases) and use these addresses for websites you don’t want to hear from again. You can then use filters to send anything from that address to your spam folder.
With a Proton Mail paid plan, you can have up to 15 additional addresses with any Proton Mail domain (@protonmail.com, @pm.me, @protonmail.ch, or @proton.me). And if you have your own domain name, you can also create additional addresses using your domain (for example, spam@yourdomain.com).
Learn more about types of email addresses and aliases
SimpleLogin
A great open-source, third-party solution to create email aliases to beat spam and phishing emails is SimpleLogin(nova janela). With SimpleLogin, you can create up to 10 aliases for free or an unlimited number with a paid plan(nova janela).
How email spam filters work
All commercial email services use automatic spam filters to protect you from spam.
Proton Mail’s smart spam filters use several techniques to detect spam and will learn from emails when you click Move to spam or mark them as not spam (click Move to inbox from the spam folder).
Block list filters
Proton Mail maintains a block list of IP addresses and email addresses known to belong to spammers.
Subject-line filters
Unlike most email services, Proton Mail cannot read the contents of emails to detect spam. But we can examine subject lines for trigger words or phrases, such as “discount,” “limited time”, or “offer”.
Subject lines in a language different from the one you have selected in settings may also be regarded as suspicious. So it’s a good idea to check your spam folder if you’re expecting to receive this kind of mail.
Header filters
Email headers can contain valuable clues that can be used to detect spam emails, such as whether the email is a copy of a group of emails sent at the same time to a particular group of recipients.
Bayesian filter
A Bayesian filter is a smart filter that learns from the emails you send to spam or mark as not spam, automatically creating custom spam rules for your inbox.
For example, if you mark a message from a certain sender as spam, a new rule-based filter is created for your account, and all future messages from that sender will be sent to your spam folder.
Content filters (not used by Proton Mail)
Other email services commonly use content filters, but not Proton Mail. This is because they rely on reading the content of your emails, which Proton Mail cannot access.
These filters scan the content of emails for trigger words. With more text to scan than just the subject line, these typically look for multiple uses of the trigger word. They may also look for emails that contain language of an inappropriate or sexual nature.
How to ensure emails don’t end up in spam
An automated filter system will inevitably make mistakes and send legitimate emails to your spam folder (or miss spam in your inbox). You can help ensure this doesn’t happen in two ways:
Use smart filters
Proton Mail uses a smart (Bayesian) filter to intelligently create rules for your account. If you find an email in your spam folder that shouldn’t be there, simply select it and click the Move to inbox (not spam) button to move the email back into your inbox and mark it as not spam.

Similarly, you can mark emails in your inbox as spam using the Move to spam button. This will send it straight to your spam folder and add the address to your Blocked list.
Our smart filters will learn from these actions and create new filter rules based on them. To view or modify these rules, sign in to your account and go to Settings → All settings → Proton Mail → Filters → Spam and block list.
Here, you can also manually add or remove email addresses from your Not spam list or Blocked list.

Learn more about spam filtering, Not spam list, and Blocked list
Use custom filters
For even greater control over your emails, you can create both simple custom filters and more advanced sieve filters.

These custom filters allow you to filter emails using various criteria and specify what will happen to them. You can move filtered emails to your spam folder or ensure they always arrive in your inbox.
Learn more about how to use filters
Learn how to create an advanced sieve filter
Final thoughts
Most spam emails are just annoying ads. But beware of malicious spam, like phishing emails, which can be dangerous.
Proton Mail’s filters will shield you from most spam. With custom filters, disposable email addresses, and a little common sense, you have the tools needed to defeat spam and take control of your inbox.
Frequently asked questions
Can I get a virus from spam?
Most spam is harmless, but some spam emails contain malicious links to phishing websites or attachments that can infect your device when downloaded.
What is phishing?
Phishing is a technique used by criminals to obtain victims’ usernames, passwords, and financial details. Much like regular spam, it usually involves sending out unsolicited emails. But these appear as if they come from a legitimate website, like a government agency, a bank, or a popular service like Netflix or PayPal.
Click on the link provided, and you’ll be taken to a forged website and invited to enter your login credentials, bank details, or other sensitive personal data. Other phishing emails contain attachments that can infect your device with malware when downloaded.
Learn more about how to prevent phishing attacks
How do I block an email address?
Most commercial email providers allow you to block unwanted emails. In Proton Mail, when you mark an email as spam, it’s automatically added to your spam filter’s Blocked list.To manage your spam filters in Proton Mail, sign in to your account and go to Settings → All settings → Proton Mail → Filters → Spam and block list.






