O que é criptografia de ponta a ponta (E2EE) e como funciona?
A criptografia de ponta a ponta mantém suas informações privadas para que apenas você e a pessoa com quem está se comunicando possam vê-las. Saiba como funciona e por que é importante para sua privacidade.
O que é criptografia de ponta a ponta?
A criptografia de ponta a ponta (E2EE) criptografa seus dados em seu dispositivo e só os descriptografa no dispositivo do destinatário. Em "de ponta a ponta", uma ponta é a origem (seu dispositivo) e a outra é o destino (o dispositivo do destinatário) da jornada dos seus dados.
Sem E2EE, seus dados podem ser descriptografados ao longo do caminho — por exemplo, nos servidores de uma empresa — tornando-os vulneráveis a hackers, vigilância e uso indevido. Com E2EE, ninguém no meio do caminho pode ler, escanear ou compartilhar suas informações confidenciais, nem mesmo o provedor de serviços.
Como funciona a criptografia de ponta a ponta?
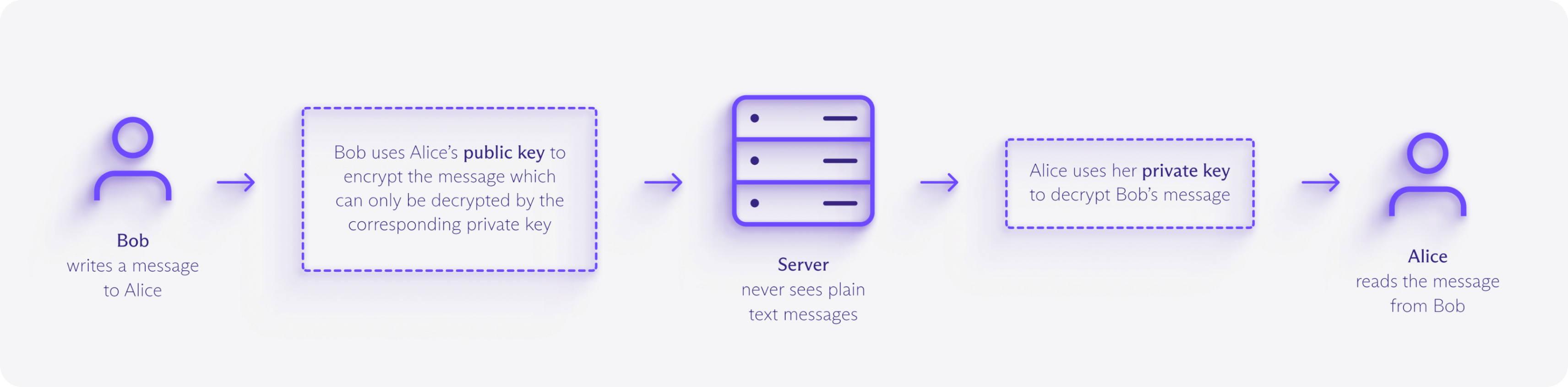
A criptografia de ponta a ponta usa criptografia assimétrica para garantir que apenas o destinatário pretendido possa descriptografar seus dados. Cada usuário possui uma chave pública (segura para compartilhar) e uma chave privada (mantida em segredo em seu dispositivo).
Quando você envia dados, seu dispositivo os criptografa com a chave pública do destinatário, produzindo dados criptografados ilegíveis chamados texto cifrado. Esse texto cifrado pode passar por vários servidores e redes sem riscos, pois apenas a chave privada correspondente pode descriptografá-lo.
Um exemplo de criptografia de ponta a ponta
Imagine que você está enviando a um amigo uma caixa trancada que só a chave dele pode abrir.
Você tranca seu conteúdo dentro da caixa antes de enviá-la pelo correio, e ela permanece trancada enquanto viaja por cada ponto de verificação postal — os "servidores".
Qualquer pessoa que manuseie a caixa pode vê-la, mas não pode olhar para dentro nem trocar o conteúdo. Apenas a chave do seu amigo pode destrancá-la.
Qual a diferença entre a criptografia de ponta a ponta e a criptografia padrão?
Os serviços on-line tradicionalmente usam criptografia em trânsito, como TLS (a tecnologia por trás do HTTPS), para criptografar seus dados enquanto eles trafegam entre seu dispositivo e os servidores deles.
Isso funciona bem para navegar em sites ou enviar formulários, já que hackers ou provedores de internet não podem ver as informações confidenciais que você insere ou recebe.
Mas, assim que seus dados chegam aos servidores da empresa, eles são descriptografados e armazenados usando chaves que ela controla. Isso significa que eles podem ler, compartilhar ou entregar a governos ou autoridades policiais, se solicitado.
Com E2EE, a empresa nunca detém as chaves privadas, portanto, não pode ler, escanear ou compartilhar seu conteúdo, mesmo que quisesse.
Quais são os benefícios da criptografia de ponta a ponta?
Privacidade
A criptografia de ponta a ponta protege seu e-mail, fotos, documentos e outros arquivos contra escaneamento, criação de perfil ou acesso não autorizado. Provedores de internet, anunciantes, corretores de dados e sistemas de vigilância não podem monitorar seu conteúdo, dando a você controle sobre suas informações pessoais.
Segurança
Como o serviço que manipula os dados não possui a chave de descriptografia, você não precisa confiar que ele não lerá, venderá ou analisará seu conteúdo. Mesmo se seus servidores forem violados, os dados roubados permanecem ilegíveis. A criptografia de ponta a ponta também preserva a integridade dos dados — seu conteúdo chega exatamente como foi enviado — e está em conformidade com regulamentos de privacidade rigorosos, como GDPR e HIPAA.
Liberdade
A comunicação privada apoia a liberdade de expressão. A criptografia de ponta a ponta defende contra censura, vigilância e perseguição política, para que você possa compartilhar ideias e informações sem medo. Todos precisam dessa proteção, mas especialmente jornalistas, ativistas e cidadãos sob regimes restritivos.
Assuma o controle dos seus dados
A Proton foi criada para proteger seus dados desde o início. Com criptografia de ponta a ponta, aplicativos de código aberto e auditorias independentes, suas informações permanecem suas.
Os e-mails que você envia para outros usuários da Proton ou para endereços que oferecem suporte a PGP (um padrão aberto para E2EE) são criptografados de ponta a ponta, incluindo o corpo da mensagem e os anexos.
Para outros casos, você pode adicionar proteção por senha. Dessa forma, apenas você e a pessoa para quem você está escrevendo podem ler seus e-mails.
Os eventos do calendário que você cria são criptografados de ponta a ponta, incluindo títulos, descrições, localizações e listas de convidados.
Mesmo quando você compartilha sua agenda ou envia um convite, ninguém mais — nem mesmo a Proton — pode ver para quem é.
Senhas, nomes de usuário, endereços da web, notas, cartões de crédito, detalhes de identidade e outros dados que você salva são protegidos com criptografia de ponta a ponta.
Quando você compartilha cofres, tanto o conteúdo quanto os links compartilhados são criptografados de ponta a ponta, para que apenas as pessoas que você convidar possam ver o que há dentro.
Tudo o que você armazena e compartilha no armazenamento na nuvem é criptografado de ponta a ponta, incluindo conteúdo de arquivos, nomes de arquivos, nomes de pastas, pré-visualizações de miniaturas e links compartilhados.
Apenas você e as pessoas com quem você escolhe compartilhar podem acessar seus arquivos — nem mesmo a Proton pode vê-los.
Saiba mais sobre criptografia