Encryption > Glossary > ChaCha20
What is ChaCha20?
ChaCha20 helps protect your data when you send messages, store files, or browse privately using an app or service.
It is a modern encryption algorithm designed to keep information confidential while remaining fast and efficient across a wide range of devices.
Learn how ChaCha20 works, why it matters in modern cryptography, and how it compares to AES.

What is ChaCha20?
ChaCha20 is a high-speed, lightweight, and highly secure 256-bit symmetric-key cipher used to encrypt and decrypt data. It was designed by Daniel J. Bernstein as an improvement on an earlier cipher called Salsa20. The goal was to create something that is both efficient and secure, especially in software.
How ChaCha20 works
ChaCha20 encrypts data by generating a stream of secure pseudorandom bytes and combining that stream with the original message. The result is encrypted output that looks random to anyone without the secret key.
Because it uses the same key to encrypt and decrypt data, ChaCha20 is much faster than RSA, an asymmetric algorithm that uses a public key and a private key. RSA is useful for key exchange and signatures, but ChaCha20 is better for encrypting large volumes of internet traffic.
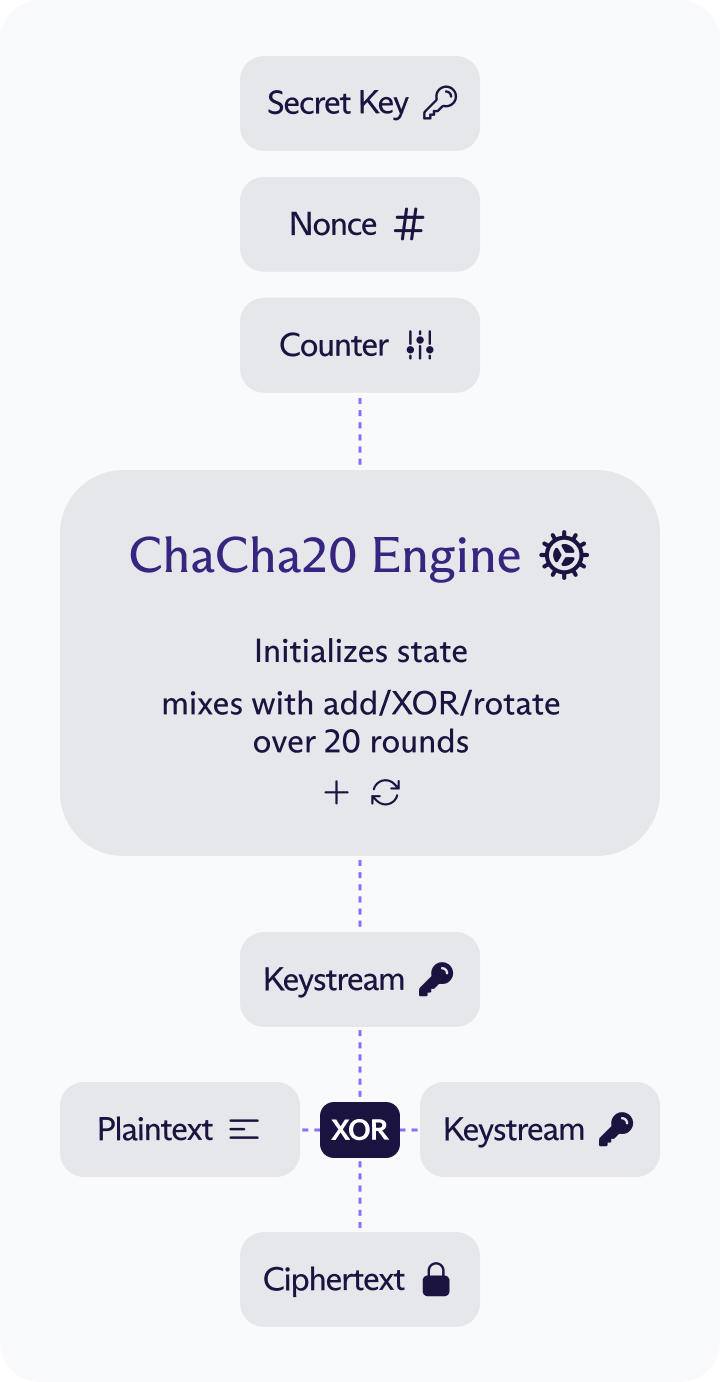
At a high level, ChaCha20 takes three inputs: a secret key, a nonce (a number used once — a unique value used for each encryption), and a counter (to help generate different output blocks). It uses these values to initialize an internal state, which is then repeatedly mixed to generate a stream of secure pseudorandom bytes known as the keystream.
That mixing process relies on three simple operations — addition, XOR, and bit rotation — applied over 20 rounds to thoroughly scramble the data. The resulting keystream is then combined with the plaintext to produce the ciphertext — the encrypted data.
Why ChaCha20 matters
ChaCha20 solves a practical problem in modern security: how to get strong encryption that is both efficient and reliable across many devices. It is very fast in software, good on phones, small devices and older CPUs, and based on simple operations computers do well (add, XOR, rotate).
These features make it attractive in systems like TLS, VPNs(nytt vindu), SSH, and messaging apps. For example, ChaCha20 is used by the WireGuard®(nytt vindu) VPN protocol(nytt vindu) to provide fast, secure encryption with strong performance even on devices that lack specialized AES hardware.
ChaCha20 vs AES
Here's how ChaCha20 compares to AES:
Aspect | ChaCha20 | AES |
|---|---|---|
| Cipher type | Stream cipher | Block cipher |
| Basic operation | Adds/XORs/rotates on 32-bit words | Substitution-permutation on 128-bit blocks |
| Standard key sizes | 256-bit | 128, 192, 256-bit |
| Performance on CPUs without special hardware | Usually very fast | Often slower than ChaCha20 |
| Performance on CPUs with hardware acceleration | Usually loses to AES with AES-NI / ARM crypto extensions | Often extremely fast |
| Typical authenticated mode | ChaCha20-Poly1305 | AES-GCM |
| Common use cases | TLS on mobile/embedded, software-only crypto, WireGuard® | TLS, disk encryption, enterprise systems, hardware-backed encryption |
| Best fit | Portability, consistent software speed, safer software implementation | Maximum speed on modern hardware, broad compliance/support |
AES encryption is the long-established standard and is extremely fast on processors with built-in AES hardware support. Because of that, it performs especially well on many desktops, servers, and newer mobile chips. However, without AES hardware support, software-only AES can be slower and sometimes harder to implement safely. In contrast, ChaCha20 is designed to be very fast in ordinary software because it uses simple operations like addition, XOR, and rotation, which work efficiently on almost any processor.
If an application offers both AES and ChaCha20, you don’t usually need to choose one manually, since most modern apps select the better option automatically based on your device and processor. In general, AES performs best on newer devices with built-in AES support, while ChaCha20 is a stronger choice on devices where encryption is handled mainly in software, such as some phones, low-power hardware, or older CPUs.
Is ChaCha20 safe?
ChaCha20 is considered secure by modern standards when implemented correctly and used with a unique nonce for each encryption.
Strong encryption
ChaCha20 uses 20 rounds of add-rotate-XOR operations and is considered resistant to known practical attacks.
Good software security
Its simple design makes it efficient in software and can reduce some side-channel risks seen in certain AES implementations.
Widely deployed
ChaCha20 is supported by major browsers and used in modern HTTPS/TLS connections, SSH, and WireGuard®.
Usually paired with Poly1305
It is often used as ChaCha20-Poly1305, which protects both confidentiality and message integrity. ChaCha20-Poly1305 is one of the main symmetric encryption options used in TLS 1.3.
Proton VPN and ChaCha20
With Proton VPN’s WireGuard® protocol(nytt vindu), ChaCha20-Poly1305 helps secure the VPN tunnel so your internet traffic stays private without sacrificing speed, whether you’re browsing privately, streaming content, or using public WiFi on the go.