How to create new encryption keys in Proton Mail
- Leitura
- 3 min
- Categoria
- Encryption and keys
By default, Proton Mail uses Elliptic Curve Cryptography (ECC) keys defined on Curve25519 to secure your emails. ECC is highly secure, fast, and compatible with almost all OpenPGP implementations.
If your account was created before 2021, you may still have RSA keys instead. To get the full benefits of ECC keys (for future sent and received emails), you can generate new keys.
Additionally, you may want to generate new keys if you believe that your existing keys have been compromised.
When interacting with certain legacy versions of OpenPGP implementations, you may need to create an RSA key (if you don’t already have one), which can be done locally, for example by running gpg --full-generate-key, and then importing the key into your Proton Mail account.
In all cases, it is extremely important that you do not delete your old keys used for encryption and signing. If you do, you will lose the ability to decrypt all your existing emails. Please follow the instructions below closely.
Generate new encryption keys
It is only possible to add new keys after you have created a Proton Mail account.
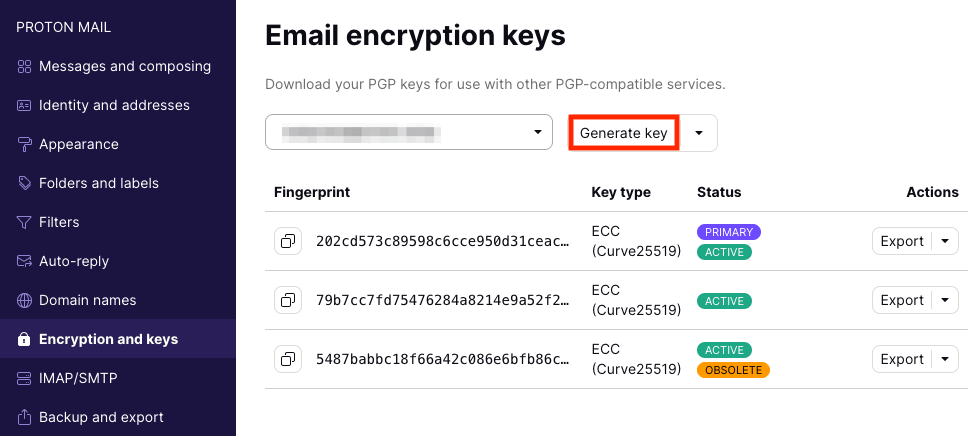
Log in to the web app at mail.proton.me(nova janela), go to Settings → All settings → Encryption and keys → Email encryption keys and click Generate key.
If you are generating a new key using the same encryption algorithm as an existing key, you will see the following warning.
You can generate up to 20 keys, but additional keys will slow down Proton Mail slightly.
Note: The newly generated key will be set as your primary (default) key automatically.
Change your primary key
Click the downloads arrow ↓ next to a key and select Use for encryption and signing.
 (nova janela)
(nova janela)Mark keys as obsolete or compromised
If you are creating a new key because you believe your old key might be compromised, or it is obsolete, click the downloads arrow ↓ next to a key and select one of the two:
- Mark obsolete: This disables encryption.
- Mark compromised: This disables signature verification on top of encryption.
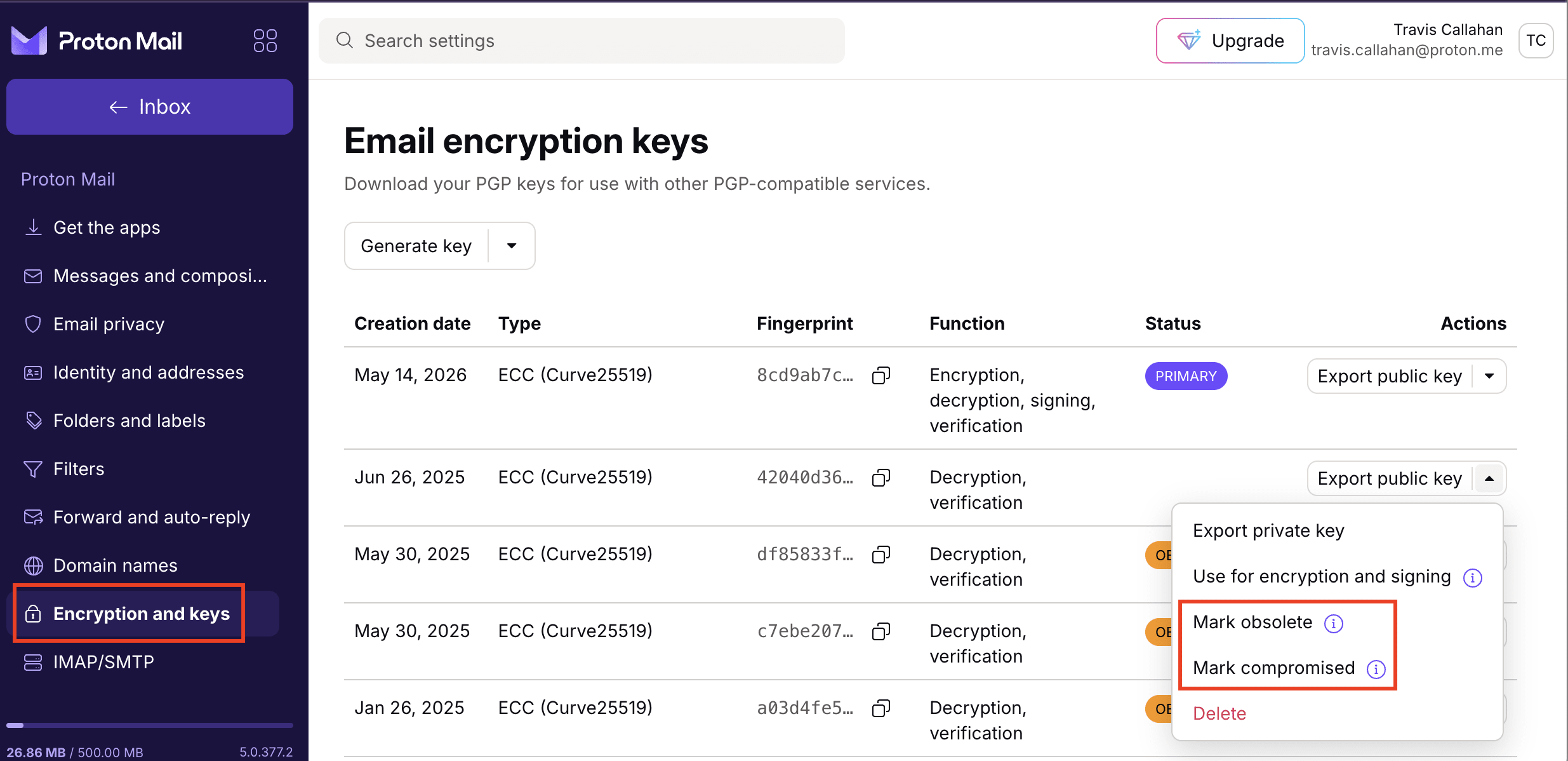
Note: Even if your encryption keys are compromised, do not delete your old keys. These are still needed to open emails that were encrypted using them.