Cos'è la crittografia end-to-end (E2EE) e come funziona?
La crittografia end-to-end mantiene private le tue informazioni in modo che solo tu e la persona con cui comunichi possiate vederle. Scopri come funziona e perché è importante per la tua privacy.
Cos'è la crittografia end-to-end?
La crittografia end-to-end (E2EE) crittografa i tuoi dati sul tuo dispositivo e li decripta solo sul dispositivo del destinatario. In “end-to-end”, da un lato c'è l'origine (il tuo dispositivo) e dall'altro la destinazione (il dispositivo del destinatario) del percorso dei tuoi dati.
Senza E2EE, i tuoi dati possono essere decriptati lungo il percorso, ad esempio sui server di un'azienda, rendendoli vulnerabili ad hacker, sorveglianza e uso improprio. Con la E2EE, nessuno può leggere, scansionare o condividere le tue informazioni sensibili, nemmeno il fornitore del servizio.
Come funziona la crittografia end-to-end?
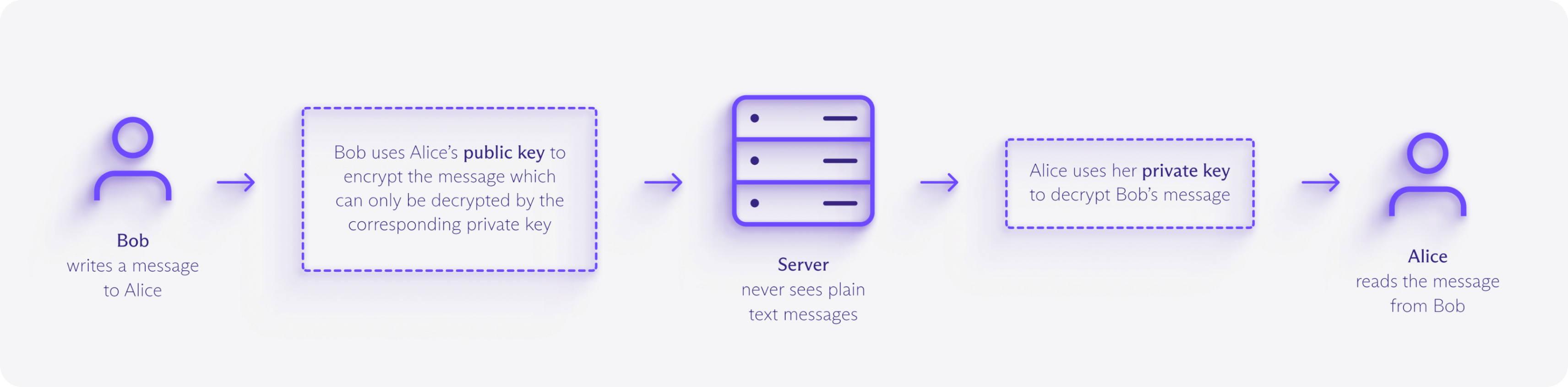
La crittografia end-to-end utilizza la crittografia asimmetrica per garantire che solo il destinatario previsto possa decriptare i tuoi dati. Ogni utente possiede una chiave pubblica (sicura da condividere) e una chiave privata (mantenuta segreta sul proprio dispositivo).
Quando invii dati, il tuo dispositivo li crittografa con la chiave pubblica del destinatario, producendo dati crittografati illeggibili chiamati testo cifrato. Questo testo cifrato può passare attraverso più server e reti senza rischi, perché solo la chiave privata corrispondente può decriptarlo.
Un esempio di crittografia end-to-end
Immagina di inviare a un tuo amico una scatola chiusa a chiave che solo la sua chiave può aprire.
Chiudi i contenuti all'interno della scatola prima di inviarla per posta, e questa rimane chiusa mentre viaggia attraverso ogni punto di controllo postale: i "server".
Chiunque maneggi la scatola può vederla, ma non può guardare al suo interno né scambiare i contenuti. Solo la chiave del tuo amico può aprirla.
In che modo la crittografia end-to-end è diversa dalla crittografia standard?
I servizi online utilizzano tradizionalmente la crittografia in transito come TLS (la tecnologia alla base di HTTPS) per crittografare i tuoi dati mentre viaggiano tra il tuo dispositivo e i loro server.
Questo sistema funziona bene per navigare sui siti web o inviare moduli, poiché gli hacker o i provider Internet non possono vedere le informazioni sensibili che inserisci o ricevi.
Ma una volta che i tuoi dati raggiungono i server dell'azienda, vengono decriptati e archiviati utilizzando chiavi che controllano. Ciò significa che possono leggerli, condividerli o consegnarli a governi o forze dell'ordine se richiesto.
Con la E2EE, l'azienda non conserva mai le chiavi private, quindi non può leggere, scansionare o condividere i tuoi contenuti, nemmeno se lo volesse.
Quali sono i vantaggi della crittografia end-to-end?
Privacy
La crittografia end-to-end protegge le tue email, le foto, i documenti e gli altri file da scansioni, profilazione o accessi non autorizzati. Fornitori di servizi Internet, inserzionisti, data broker e sistemi di sorveglianza non possono monitorare i tuoi contenuti, lasciandoti il controllo sulle tue informazioni personali.
Sicurezza
Poiché il servizio che gestisce i dati non possiede la chiave di decriptazione, non devi fidarti del fatto che non legga, venda o analizzi i tuoi contenuti. Anche se i suoi server venissero violati, i dati rubati rimarrebbero illeggibili. La crittografia end-to-end preserva anche l'integrità dei dati: i tuoi contenuto arrivano esattamente come sono stati inviati e rispettano rigide normative sulla privacy come il GDPR e l'HIPAA.
Libertà
La comunicazione privata supporta la libera espressione. La crittografia end-to-end difende da censura, sorveglianza e persecuzione politica, così puoi condividere idee e informazioni senza paura. Tutti hanno bisogno di questa protezione, ma in particolare i giornalisti, gli attivisti e i cittadini che vivono sottoposti a regimi restrittivi.
Prendi il controllo dei tuoi dati
Proton è stato creato per proteggere i tuoi dati fin dall'inizio. Con la crittografia end-to-end, le app open source e gli audit indipendenti, le tue informazioni rimangono tue.
Le email che invii ad altri utenti Proton o a indirizzi che supportano PGP (uno standard aperto per la E2EE) sono crittografate end-to-end, inclusi il corpo del messaggio e gli allegati.
Per altri casi, puoi aggiungere la protezione tramite password. In questo modo, solo tu e la persona a cui scrivi potete leggere le tue email.
Gli eventi del calendario che crei sono crittografati end-to-end, inclusi titoli, descrizioni, posizioni ed elenchi degli invitati.
Anche quando condividi i tuoi impegni o invii un invito, nessun altro, nemmeno Proton, può vedere a chi è rivolto.
Password, nomi utente, indirizzi web, note, carte di credito, dettagli dell'identità e altri dati che salvi sono protetti con crittografia end-to-end.
Quando condividi le casseforti, sia i contenuti che i link condivisi sono crittografati end-to-end, in modo che solo le persone che inviti possano vedere cosa c'è dentro.
Tutto ciò che archivi e condividi nell'archiviazione cloud è crittografato end-to-end, inclusi contenuti dei file, nomi dei file, nomi delle cartelle, anteprime delle miniature e link condivisi.
Solo tu e le persone con cui scegli di condividere potete accedere ai tuoi file. Nemmeno Proton può vederli.
Scopri di più sulla crittografia