¿Qué es el cifrado de extremo a extremo (E2EE) y cómo funciona?
El cifrado de extremo a extremo mantiene tu información privada para que solo tú y la persona con la que te comunicas podáis verla. Descubre cómo funciona y por qué es importante para tu privacidad.
¿Qué es el cifrado de extremo a extremo?
El cifrado de extremo a extremo (E2EE) cifra tus datos en tu dispositivo y solo los descifra en el dispositivo del destinatario. En «de extremo a extremo», un extremo es el origen (tu dispositivo) y el otro es el destino (el dispositivo del destinatario) del viaje de tus datos.
Sin E2EE, tus datos pueden ser descifrados en el camino; por ejemplo, en los servidores de una empresa, haciéndolos vulnerables a hackers, vigilancia y uso indebido. Con E2EE, nadie en el camino puede leer, escanear o compartir tu información confidencial, ni siquiera el proveedor del servicio.
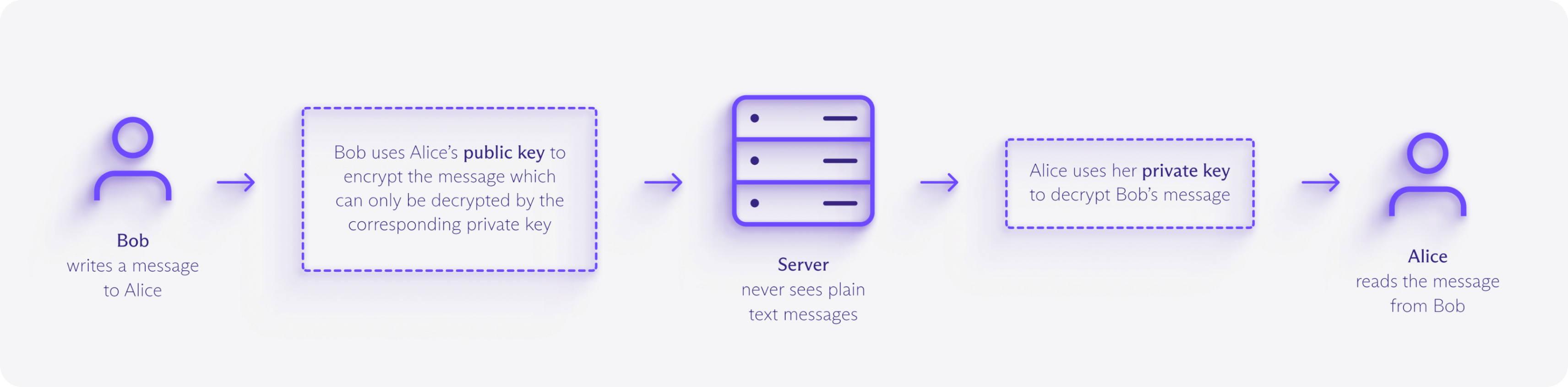
¿Cómo funciona el cifrado de extremo a extremo?
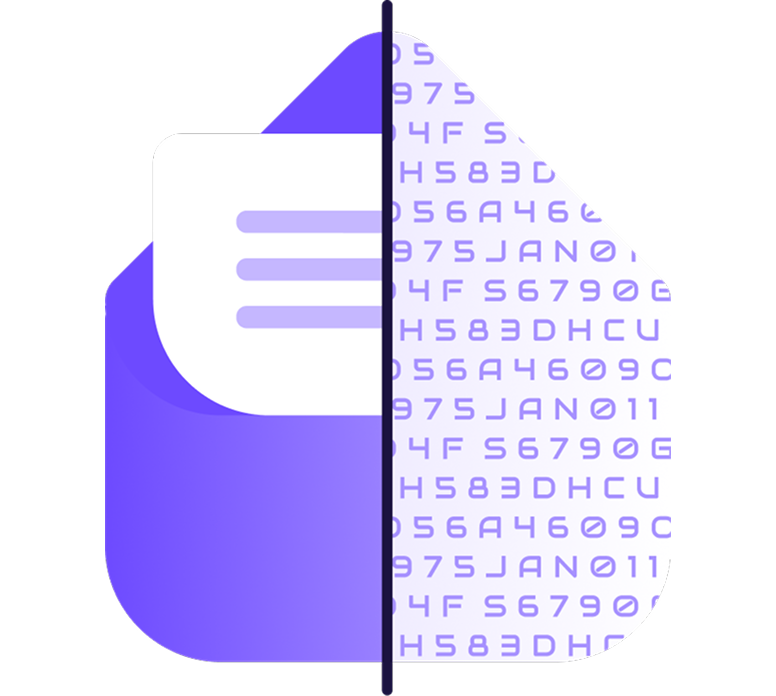
El cifrado de extremo a extremo utiliza criptografía asimétrica para garantizar que solo el destinatario previsto pueda descifrar tus datos. Cada usuario tiene una clave pública (segura para compartir) y una clave privada (mantenida en secreto en su dispositivo).
Cuando envías datos, tu dispositivo los cifra con la clave pública del destinatario, produciendo datos cifrados ilegibles llamados texto cifrado. Este texto cifrado puede pasar a través de múltiples servidores y redes sin riesgo, porque solo la clave privada correspondiente puede descifrarlo.
Un ejemplo de cifrado de extremo a extremo
Imagina que envías a un amigo una caja cerrada que solo su llave puede abrir.
Cierras el contenido dentro de la caja antes de enviarla por correo, y permanece cerrada mientras viaja a través de cada punto de control postal: los «servidores».
Cualquiera que manipule la caja puede verla, pero no puede mirar dentro ni cambiar el contenido. Solo la llave de tu amigo puede abrirla.
¿En qué se diferencia el cifrado de extremo a extremo del cifrado estándar?
Los servicios online utilizan tradicionalmente cifrado en tránsito como TLS (la tecnología detrás de HTTPS) para cifrar tus datos mientras viajan entre tu dispositivo y sus servidores.
Esto funciona bien para navegar por sitios web o enviar formularios, ya que los hackers o los proveedores de Internet no pueden ver la información sensible que introduces o recibes.
Pero una vez que tus datos llegan a los servidores de la empresa, son descifrados y almacenados usando claves que ellos controlan. Eso significa que pueden leerlos, compartirlos o entregarlos a gobiernos o fuerzas del orden si se les solicita.
Con el E2EE, la empresa nunca tiene las claves privadas, por lo que no puede leer, escanear o compartir tu contenido, incluso si quisiera.
¿Cuáles son los beneficios del cifrado de extremo a extremo?
Privacidad
El cifrado de extremo a extremo protege tu correo electrónico, fotos, documentos y otros archivos del escaneo, la elaboración de perfiles o el acceso no autorizado. Los proveedores de internet, anunciantes, intermediarios de datos y sistemas de vigilancia no pueden monitorear tu contenido, dándote control sobre tu información personal.
Seguridad
Como el servicio que maneja los datos no tiene la clave de descifrado, no tienes que confiar en que no lea, venda o analice tu contenido. Incluso si sus servidores son vulnerados, los datos robados permanecen ilegibles. El cifrado de extremo a extremo también preserva la integridad de los datos, tu contenido llega exactamente tal y como se envió, y cumple con estrictas normativas de privacidad como el GDPR y la HIPAA.
Libertad
La comunicación privada apoya la libertad de expresión. El cifrado de extremo a extremo defiende contra la censura, la vigilancia y la persecución política, para que puedas compartir ideas e información sin miedo. Todo el mundo necesita esta protección, pero especialmente los periodistas, activistas y ciudadanos bajo regímenes restrictivos.
Toma el control de tus datos
Proton se creó para proteger tus datos desde el principio. Con el cifrado de extremo a extremo, las aplicaciones de código abierto y las auditorías independientes, tu información sigue siendo tuya.
Los correos electrónicos que envías a otros usuarios de Proton o a direcciones que admiten PGP (un estándar abierto para E2EE) están cifrados de extremo a extremo, incluido el cuerpo del mensaje y los archivos adjuntos.
Para otros casos, puedes añadir protección por contraseña. De esa manera, solo tú y la persona a la que escribes podéis leer tus correos electrónicos.
Los eventos del calendario que creas están cifrados de extremo a extremo, incluidos los títulos, descripciones, ubicaciones y listas de invitados.
Incluso cuando compartes tu horario o envías una invitación, nadie más (ni siquiera Proton) puede ver para quién es.
Las contraseñas, nombres de usuario, direcciones web, notas, tarjetas de débito o crédito, detalles de identidad y otros datos que guardas están protegidos con cifrado de extremo a extremo.
Cuando compartes cajas fuertes, tanto el contenido como los enlaces compartidos están cifrados de extremo a extremo, para que solo las personas que invitas puedan ver qué hay dentro.
Todo lo que almacenas y compartes en el almacenamiento en la nube está cifrado de extremo a extremo, incluido el contenido de los archivos, los nombres de archivo, los nombres de carpetas, las vistas previas en miniatura y los enlaces compartidos.
Solo tú y las personas con las que elijas compartir pueden acceder a tus archivos; ni siquiera Proton puede verlos.
Más información sobre el cifrado