More of our most critical communications now happen through online video calls. Yet recent advances in AI and data mining technology have placed these calls at high risk of exploitation and abuse.
Many video conferencing services are driven by advertising models or the AI race to record, transcribe, and store as much meeting data as possible. These Big Tech companies can now cheaply deploy generative AI to analyze and learn from everything said and presented in our meetings.
In the AI era, unencrypted video conferencing threatens individual freedom and organizational security. That’s why we built Proton Meet: to deliver an enterprise-grade experience comparable to Zoom, Google Meet, and Microsoft Teams, while protecting every call with always-on end-to-end encryption. With Proton Meet, no one — not even us — can eavesdrop on your calls.
Like all Proton services, Proton Meet offers a powerful free tier because we believe everyone deserves freedom and privacy, regardless of their ability to pay for it.
The security problem with existing meeting solutions
On the consumer side, many rely on services like WhatsApp, Facebook Messenger, or Apple FaceTime to connect with friends and family. While these apps use end-to-end encryption to prevent the provider from listening in, they come with significant downsides:
- High friction & metadata collection: Every participant must install the app, create an account (often requiring a phone number or email), and be added to a group. This process creates high friction and allows providers to harvest valuable social graph metadata.
- IP address exposure: These services often default to peer-to-peer connections(nova finestra). This means participants can see each other’s IP addresses, potentially revealing their physical locations unless they are using a reputable VPN(nova finestra).
- Scalability limits: Consumer chat apps struggle with large groups because peer-to-peer connections grow exponentially with each added participant. Consequently, call limits are strict — WhatsApp caps at 32 participants, and many others cap at 50.
For professional meetings, services like Zoom, Google Meet, and Microsoft Teams are widely used. These services use massive servers in data centers to relay audio and video, so they can scale to larger meetings with up to 1,000 participants while hiding participant IPs from each other. They also offer high accessibility, allowing users to join via any web browser without creating an account.
However, end-to-end encryption (E2EE) is either absent or poorly implemented. Fundamentally, these platforms were not designed with privacy as a priority.
Proton Meet solves this dilemma by leveraging the cutting-edge Messaging Layer Security (MLS) encryption protocol, while retaining the accessibility and administrative controls expected from enterprise solutions.
Technical design
WebRTC for high performance and easy access
Similar to other professional meeting services, Proton Meet’s foundation is WebRTC technology with Selective Forwarding Units (SFU), which are the big servers that relay audio, video, chat, and other data to all participants.
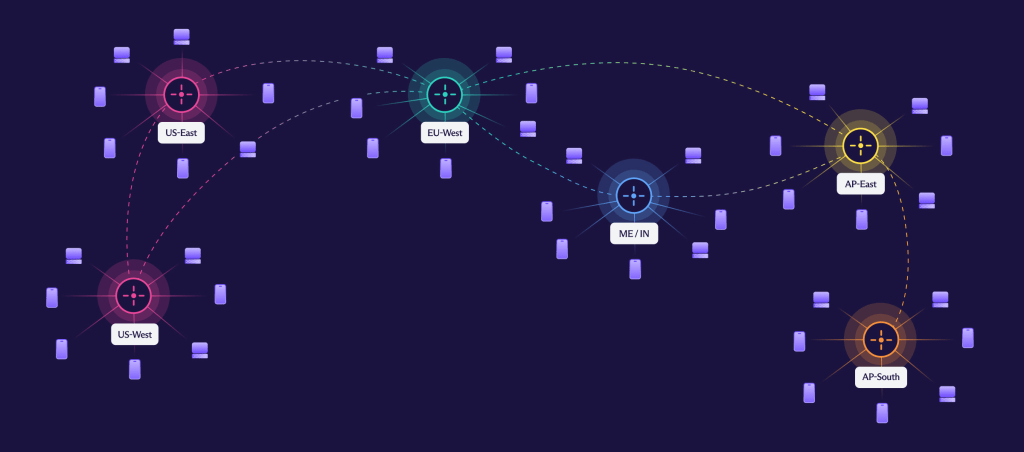
We utilize a distributed network of data centers around the world like we do for Proton VPN to provide the highest reliability and lowest latency for each call. Because there are no peer-to-peer connections, we can scale to massive group calls while obfuscating the IPs of participants from each other.
Since WebRTC is a mature technology adopted by all the major browsers, Proton Meet can be accessed from any computer or mobile device with a web browser. You can send a meeting link to anyone in the world and they can join the meeting instantly in any web browser, even if they don’t have a Proton Account or Proton Meet app. In addition to the web browser app, Proton Meet also has desktop and mobile apps for those who prefer to use apps instead of a browser.
Meeting authentication with SRP so Proton can never access your calls
Similar to other professional meeting services, we provide admin controls for hosts to manage their meetings. The host is the user who created the meeting link and sent it to other participants. It is critical that hosts only share the meeting links with trusted people, because anyone with the full meeting link can join the meeting if the meeting is not locked. We designed Proton Meet to automatically generate a unique password for each meeting, but this password is never known to Proton servers, preventing us from accessing a meeting.
A meeting link looks like:

It includes a meeting ID (S0NDHQ48NR) and a password (LaggoOcjlq6L). The hash symbol (#) in the link means the part after it (the password, in our case) is not sent to the server by the browser. This prevents the password from getting logged or accessed on the server side. The password is generated on the host’s device and then shared with the host’s other devices with end-to-end encryption so that the host can securely access their meeting links from all their logged-in apps and devices.
When a meeting link is created, the host’s client stores a password verifier with the server so Proton Meet can use the Secure Remote Password (SRP) protocol(nova finestra) to ensure all meeting participants have the right passwords, without the server ever knowing the password. SRP has been securing Proton logins for the past 10 years and ensures Proton servers can serve the right user without Proton having access to the password that can unlock the private keys.
End-to-end encryption with Messaging Layer Security (MLS)
The goal of end-to-end encryption (E2EE) is to ensure only the participants can decrypt the communication. Other third parties, including the service provider, should not be able to eavesdrop.
Most E2EE protocols are built for 1-to-1 communication. For example, in Proton Mail, which uses OpenPGP for E2EE, if you send an email to multiple Proton Mail users, OpenPGP has to asymmetrically encrypt for each recipient using each recipient’s public key. The computation and bandwidth scale linearly with the number of participants and it becomes very expensive for large group chats and calls.
In 2023, a protocol called Messaging Layer Security (MLS), which some members of the Proton team have been working on, became an IETF standard. It provides a much more performant way to use E2EE for large groups. The idea is that as members are added or removed, they contribute keying material for that cycle of the protocol, called an epoch. The members are organized in a binary tree that allows them to efficiently update members with new secrets when entering a new epoch. Every member cryptographically agrees on who is in the group at all times.
In Proton Meet, the epoch key is used to derive the keys used for encrypting the audio, video, and messages sent to the group. When a new participant joins or when a participant leaves, this triggers a key rotation and everyone starts to use new keys. This means that a participant only has the cryptographic keys to decrypt communication sent after they joined and before they left the group, ensuring forward secrecy and post-compromise security.
In Proton Meet, all audio, video, screen share, and chat data are always encrypted on the client-side using a key provided by MLS before sending to the SFU servers, which simply forward the encrypted data to the other participants.
Proton Meet uses the meeting password as a pre-shared key (PSK) in MLS to ensure only participants with the right meeting password can derive the right MLS keys. Since the Proton Meet servers do not have the meeting password and thus cannot derive the MLS keys, Proton cannot decrypt and record any of the audio, video, screen share, or chat messages. Note that participants can still record meetings locally on their devices.
Threat model
No logs
While E2EE can secure meeting audio and video streams, it does not protect metadata such as social graphs that can linger online and harm our privacy. Many of Proton’s users are high-profile journalists, activists, and executives who need to ensure their identities and relationships stay confidential. Proton Meet aims for data minimization and does not store metadata logs such as who met with whom after the call ended. Participants can also join meetings anonymously without logging into a Proton account.
Anonymous identity
Proton Meet does not reveal the identity of meeting participants to each other. Every time you join a meeting, you can choose any name to use for that meeting. If you are logged in, the name field will auto-fill with the primary name of the account for convenience. This participant name is end-to-end encrypted with a key derived from the meeting password and then shared with other participants. No Personally Identifiable Information (PII) such as email address or IP is visible to other participants. Note that if you send calendar invites, the email will reveal the email address linked to that calendar.
Server compromise
We designed Proton Meet to minimize both the amount of trust needed in Proton servers and the level of risk if our servers are compromised. Below, we will go over various scenarios and how users can stay vigilant and detect meeting intrusions.
- First, if just the WebRTC SFU servers get compromised, the attacker can censor and block the forwarding of audio, video or chat data, but cannot read or alter the data due to the keys only being shared via MLS end-to-end encryption. The SFU servers also cannot identify which SFU room corresponds to which meeting ID, as that mapping is only visible on our database and backend API servers.
- Second, if Proton Meet’s database servers are compromised, there is very little data leak risk as the databases only have the meeting IDs and never have the passwords nor any audio, video, or chat data. So the attacker would not be able to join any meetings, nor learn past meeting participants, nor access any sensitive data.
- Finally, if Proton Meet’s backend API servers, including the MLS servers, are compromised, an attacker can try to join the MLS group, posing as a new participant. However without the meeting password for the pre-shared key, the attacker will not be able to derive the right MLS keys and thus will not be able to hear or see the other participants. For users with extremely high security requirements, the meeting info tab shows the MLS state such as the epoch, the group size, and the security code that is derived from the epoch secret. Therefore it is possible to verify that the MLS group size matches the number of trusted participants in the meeting and the security code is the same across all participants.

Since the MLS data is stored on every client device, any change to the MLS group will be visible to all participants. So even if all servers are compromised and an attacker joins the meeting, every participant will be able to see the MLS state change and that there are more participants than expected. Since all Proton Meet clients are open sourced(nova finestra), anyone can review the security of the client-side code that implements MLS.
Compromised meeting link
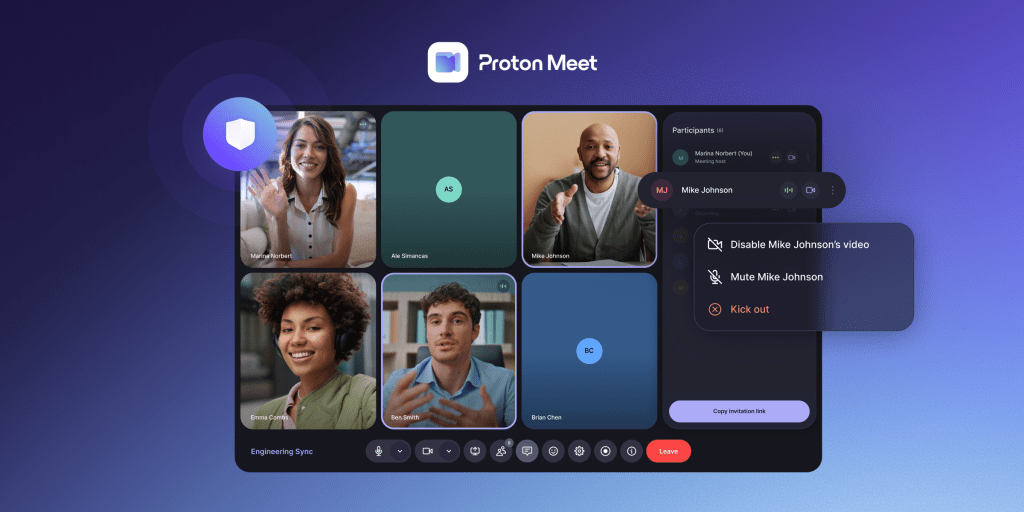
The primary risk to a Proton Meet call is an unauthorized participant gaining access via a shared link. To mitigate this, hosts can lock meetings once expected attendees have arrived. They can also mute audio, stop video, or remove unwanted participants instantly.
We also recommend generating a unique meeting link for every session to prevent link reuse across different groups. This is handled automatically when using the Schedule Meeting feature, and permanent meeting room links can also be manually rotated as needed. Future updates will include even more enhanced security controls.
Conclusion
The launch of Proton Meet is a significant milestone in our mission to build a more private internet. While Big Tech video call solutions take advantage of our need to connect by eavesdropping on our calls and monetizing our data, Proton Meet’s security model ensures that your private conversations stay private.
End-to-end encrypted and based in Europe, Proton Meet offers a truly sovereign Big Tech alternative for both personal and professional communication — protecting you from breaches, surveillance, and exploitation. Shielded by zero-access encryption, multi-layered security, and some of the world’s strongest privacy laws, Proton Meet helps business simplify compliance and shields all users from US data requests and extraterritorial jurisdiction.
Our principles are safeguarded by Proton’s primary shareholder, the nonprofit Proton Foundation, and our business exists to serve the interest of our community. So, like all our services, Proton Meet’s development will be guided by your feedback and feature requests. Thank you for all your support.






