en Learn how to plan an MFA rollout, choose the right authentication methods,
reduce employee resistance, and enforce MFA across your business.
en Covering the 2026 FIFA World Cup? Here's how journalists can stay safe from
physical threats, border scrutiny, and digital surveillance.
en Learn how your small businesses can build a compliance foundation that wins
deals, protects data, and proves your security posture.
en Learn how to use Google Photos' Locked Folder, how it exposes your photos to
Google, and a safer way to store sensitive images privately.
en Compare internal communication software to find tools that keep every message,
file, and meeting your team exchanges private.
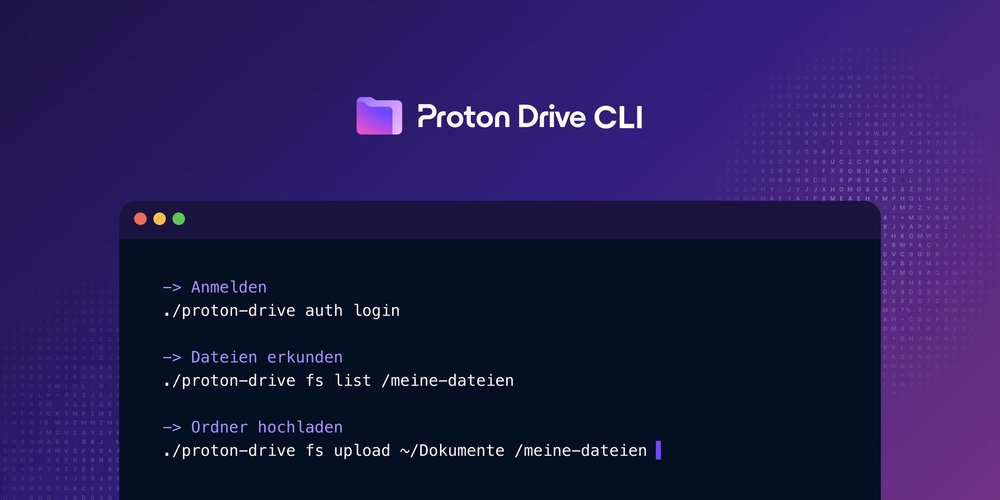
9. Juni 2026 Produkt-Updates Proton Drive Die Proton Drive CLI ist ab sofort für Windows, macOS und Linux verfügbar. Lade
Dateien hoch und herunter, teile sie und automatisiere deine Drive-Workflows
direkt über das Terminal.