Practical lessons from a hacker’s playbook
Most founders think their businesses are too small to be targeted. That’s exactly why hackers love them.
Attackers look for the entry point with the least friction. In a fast-moving startup, there’s no shortage of easy ways in: a busy founder, a reused password, or an unsecured home network.
Learn how to defend your tech SMB.
Why startups are the perfect prey for hackers
Small mistakes travel fast in a startup because they are:
Built for speed
Things move quickly. Errors can propagate before anyone pauses to contain them.
Generous with trust
Requests from familiar names are acted on without friction. Attackers will step into that trust.
Grant broad access
Small teams share permissions across tools. One identity can unlock many systems
Original research from the Proton Data Breach Observatory shows the real-world impact of these conditions:
71% of breaches affect small and medium-sized businesses
A single breach can cost a startup over $1 million
The cost of inaction
Most startups don't realize they are the path of least resistance until the investigation begins. Secure your build by learning the offensive tactics used to compromise your peers.

How a breach unfolds in 2026
Secrets of a Hacker’s Playbook walks through a realistic attack from the attacker’s point of view.
Based on decades of real-world breach analysis, it strips away jargon and Hollywood myths to show how a ghost in the machine dismantles an organization from the inside.
Phishing for a key
An hour on LinkedIn is enough to identify who approves payments, who manages infrastructure, and who’s overloaded.
Weaponizing the inbox
Once inside, the hacker reads contracts, tracks travel schedules, monitors invoices, and sees how decisions get made.
Exploiting the supply chain
Instead of a loud, dramatic theft, they perform a malicious commit to hide a data harvester inside a routine update.
The damage report
The startup realises too late: their IP is gone, funds are diverted, and customer data has been compromised.
What you’ll learn in this ebook
Secrets of a Hacker’s Playbook translates an attack into clear, actionable insight for startups.
Where modern attacks start: Hackers target people and third-party vendors instead of head on assaults on your servers.
The danger of a breached inbox: Internal systems become vulnerable once an attacker has access to a single employee's email.
The cost of haste: Developer trust and rapid shipping cycles create hidden risks in your codebase.
Proven hack prevention: Identify security controls that actually stop an attack versus those that only look good on paper.

Secrets of a Hacker’s Playbook is a threat model you can apply immediately.
Who needs to read the Hacker’s Playbook?
This guide is written for startup founders, CTOs, and technical leads who:
Ship software
Handle customer data
Work with small teams
Make security decisions
Want to sleep at night

Download the free guide: Secrets of a Hacker’s Playbook
See your business through an attacker’s eyes — and learn how real breaches actually unfold.

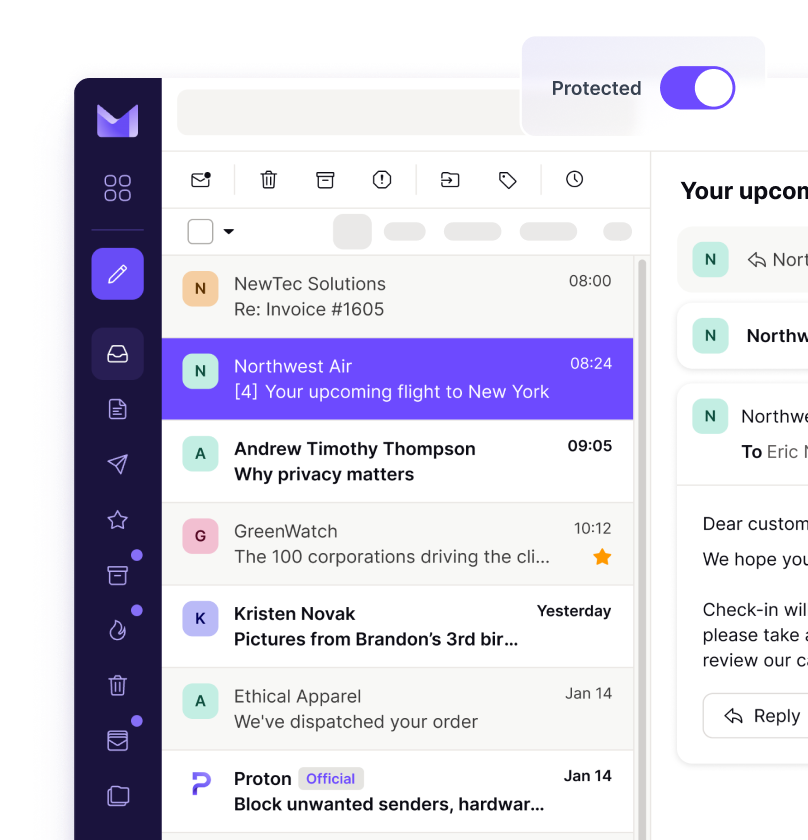
Stop hacks in their tracks with Proton for Business
Proton’s ecosystem acts as an attack circuit breaker. If one layer fails, the next one stops the attacker cold.
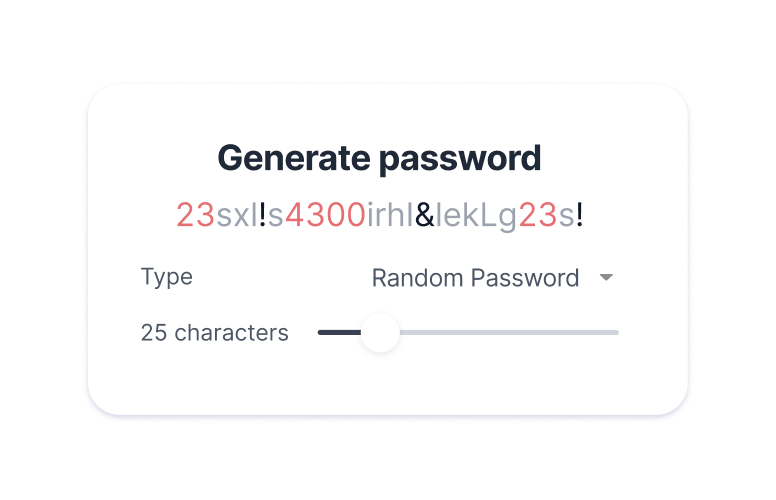
Eliminate password reuse with Proton Pass
Unique, strong credentials for every service. Automatic phishing protection that refuses to autofill on spoofed domains.
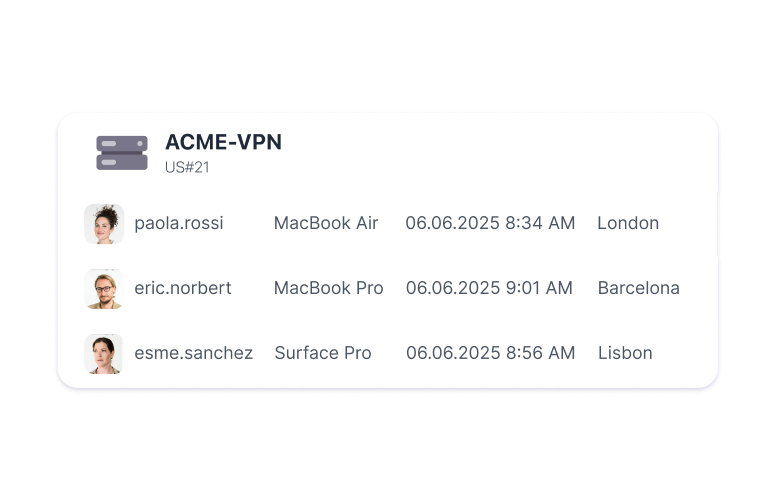
Constrain access with Proton VPN
Dedicated gateways let you restrict logins to approved company IPs. Stolen credentials fail outside your network.
Detect ghosts early with Proton Sentinel
High-risk accounts are monitored for suspicious behavior. Unusual devices or locations are flagged before reconnaissance begins.
Secure communications with Proton Mail
Zero-access encryption keeps internal strategy, financial discussions, and board communications unreadable — even during provider-level breaches.
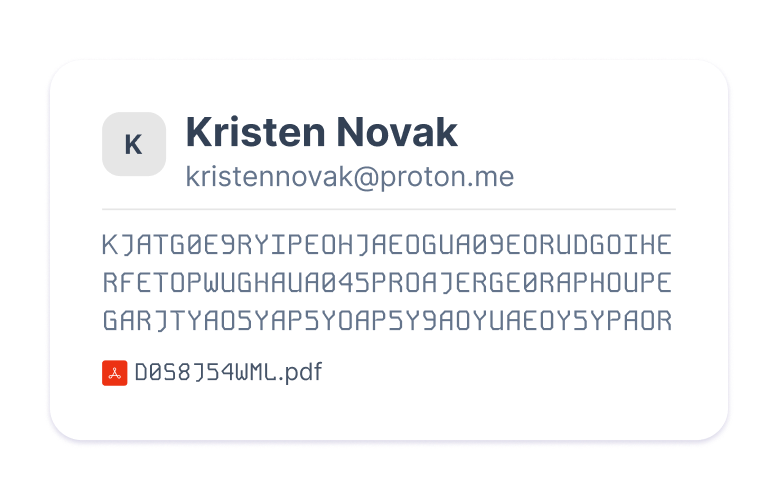
Secure communications with Proton Mail
Zero-access encryption keeps internal strategy, financial discussions, and board communications unreadable — even during provider-level breaches.
Frequently asked questions
- Is this guide technical or non-technical?
- Is this a real attack or a hypothetical scenario?
- Does the ebook focus on prevention or damage control?
- How long does it take to read?