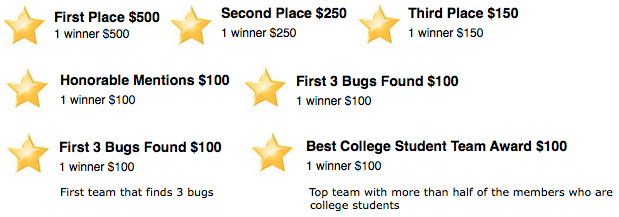
$1000+ in prizes, 6 hours, free food and drink. August 2, 2014 at MIT.
Register on Eventbrite(new window). View the hackathon webpage(new window).
We feel that privacy is a fundamental human right. The goal of the Proton Mail project is to build an encrypted email service that is easy enough for the general public to adopt, but at the same time secure enough to deter large scale surveillance. The project is quite young (and still in Beta), but we hope to take some meaningful steps towards helping common people secure their online communications.
To accomplish this, we need the help of the security community. We have two goals in mind for this competition. One is to invite members of security community to work with us to make the next versions of Proton Mail more secure by finding and patching vulnerabilities. Secondly, we want this to be an opportunity for web security practictioners to learn from each other. At the end of the competition, there will be a discussion where participants can detail the attack methods used, and defense mechanisms to thwart such attacks.
We welcome everybody from novices to experts, and we will have free food, drinks, and prizes for the top teams. The competition will take place at MIT on Saturday, August 2 from 1:30 pm until approximately 8:00 pm (room TBA). Participants will be given access to the next version of Proton Mail to perform penetration testing. The competition rules, schedule, and other important details are provided below.
Schedule
1:00 Registration + Find Teammates
1:30 Competition Begins!
6:00 Dinner Arrives, Judging Begins
6:30 Discussion/Presentation (offsite participants can paricipate via video conference)
7:30 Winners Announced!
You can work either independently or in a team. The maximum is 5 members per team. Same rules apply to offsite participants.
Eligibility/Rules
- Scope: Attacks will be limited to the development machine provided expressedly for the competition. Both server and web application vulnerabilities are fair game with the exception of DDOS attacks.
- Judging: The judging panel will consist of Proton Mail developers assisted by one more more outside experts who are not participating in the competition. Participate agree to respect the final decision made by the judges.
- Responsible disclosure: We request that all vulnerabilities be reported to us at competition@proton.me. We believe it is against the spirit of this competition to disclose the flaw to third parties for purposes other than actually fixing the bug. Partcipants agree to not disclose bugs found during the competition and discussed in the discussion until after our security team has confirmed they have been fixed.
- Prize announcements: If you are part of a winning team, you need to provide us some identifying information (such as a Twitter account, Linkedin profile, website or email information), winners cannot be completely anonymous.
- By participating in this competition, you agree to adhere to the above rules and conditions. All rules must be followed to be eligible for prizes.
Judging Criteria
Judging will be based on impact criterion as below:
Impact
- privacy violation, user data disclosure = 5
- corrupt data = 3
- minor server and web application vulnerability = 1
Submission Instruction
To maximize the points earned and to meet our judging deadline, each team should write a short report when a vulnerability is found and email the report to competition@proton.me. The report should include the following:
- team name
- operating system and web browser in which the vulnerability is found
- step-by-step procedure of how to produce the security vulnerability
A clear step-by-step procedure will help the judges to confirm the security vulnerability and award points in real time. Screenshots and video are very helpful but not required.