Proton Pass is an end-to-end encrypted password manager based on the same well-tested encryption that secures the rest of the Proton ecosystem. Proton Pass is unique in that it was designed from the ground up to have a strong focus on privacy and security. It therefore has a more complete encryption model than most other password managers.
Read more about the launch of Proton Pass beta
Proton Pass doesn’t just encrypt the password field but applies end-to-end encryption to all fields, including usernames, web addresses, and all data contained in the encrypted notes section.
This means Proton Pass prevents anyone, including Proton itself, from knowing which online services you subscribe to or have accounts with. This information, much like your emails or your browsing history, can reveal a lot about you and must be protected if you want to maintain your privacy.
The design of Proton Pass uses end-to-end encryption, guaranteeing that all cryptographic operations, including key generation and data encryption, are performed locally on your device. This means that your unencrypted data cannot be accessed by Proton or shared with any third parties. Proton servers never have access to your unencrypted keys, data, or credentials, including your Proton Account password.
Data model
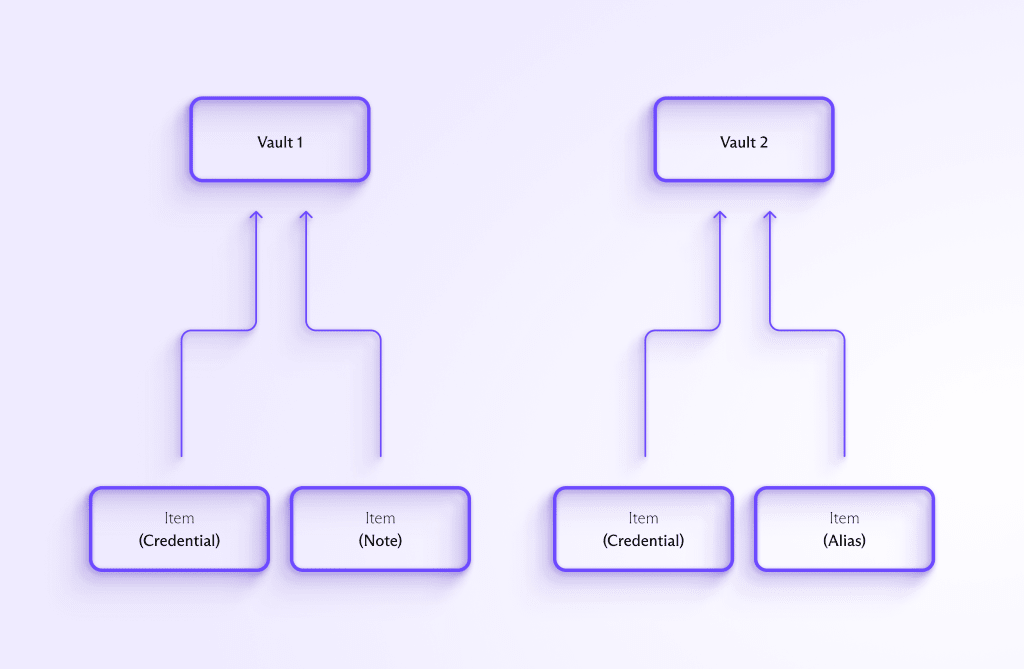
Proton Pass enables you to store various types of information securely, including:
- Credentials: You can store access credentials to websites or apps, which may include a username or email, a password, and a second-factor authentication code (TOTP).
- Notes: You can securely store any information that doesn’t fit in a credential field in this free-form text field, including license numbers, codes, or simple text notes.
- Aliases: You can also create email aliases with Proton Pass. This feature enables you to create randomly generated email addresses that you can use in place of your real email addresses for online accounts. This makes it easy to shut down an alias that’s linked to a service that’s breached or begins sending you spam without affecting your other accounts.
Proton Pass stores all these items within a secure vault. Vaults provide a convenient way for you to organize and (in the future) securely share your data.
Encryption model
Proton Pass takes a comprehensive approach to ensuring maximum security and privacy for all user data. All cryptographic operations occur locally on your device, and any data transmitted to the server is always encrypted. Proton never has access to the plaintext keys required to decrypt user data, making it impossible for Proton to decrypt stored data, even if requested by third parties.
Proton Pass also benefits from the same advanced encryption we utilize for authentication in Proton Mail. This includes using a hardened version of the Secure Remote Password (SRP) protocol that offers stronger security guarantees against man-in-the-middle (MITM) attacks. Our implementation means that even an attacker who can arbitrarily read, modify, delay, destroy, repeat, or fabricate messages between Proton and a user in an undetectable fashion is limited to checking only a single password guess per login attempt, which is equivalent to just trying to log in directly. This way, even if Proton is compromised and acts maliciously, password-equivalent information is never revealed.
Read more about Proton’s authentication encryption
Vault encryption
Each Proton Pass user has an asymmetric user key. Proton Pass encrypts this user key as follows:
- Accounts that use a single account password: Proton Pass encrypts the user key with a bcrypt hash of the account password and the account salt.
- Accounts that use our multiple account passwords feature: Proton Pass encrypts the user key with a bcrypt hash of the key password and the account salt.
The user key is used to open all shares you can access, meaning it must be secured. The bcrypt password hashing implementation used by Proton Pass is more robust and secure than PBKDF2, which has led to breaches in other password managers.
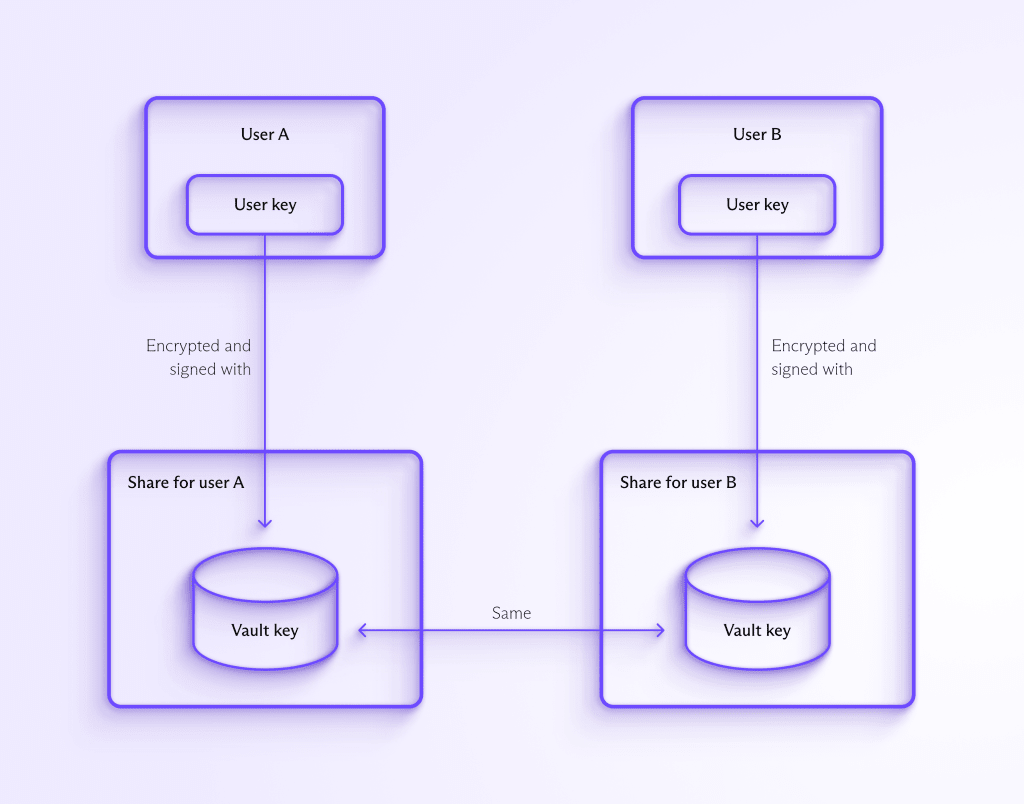
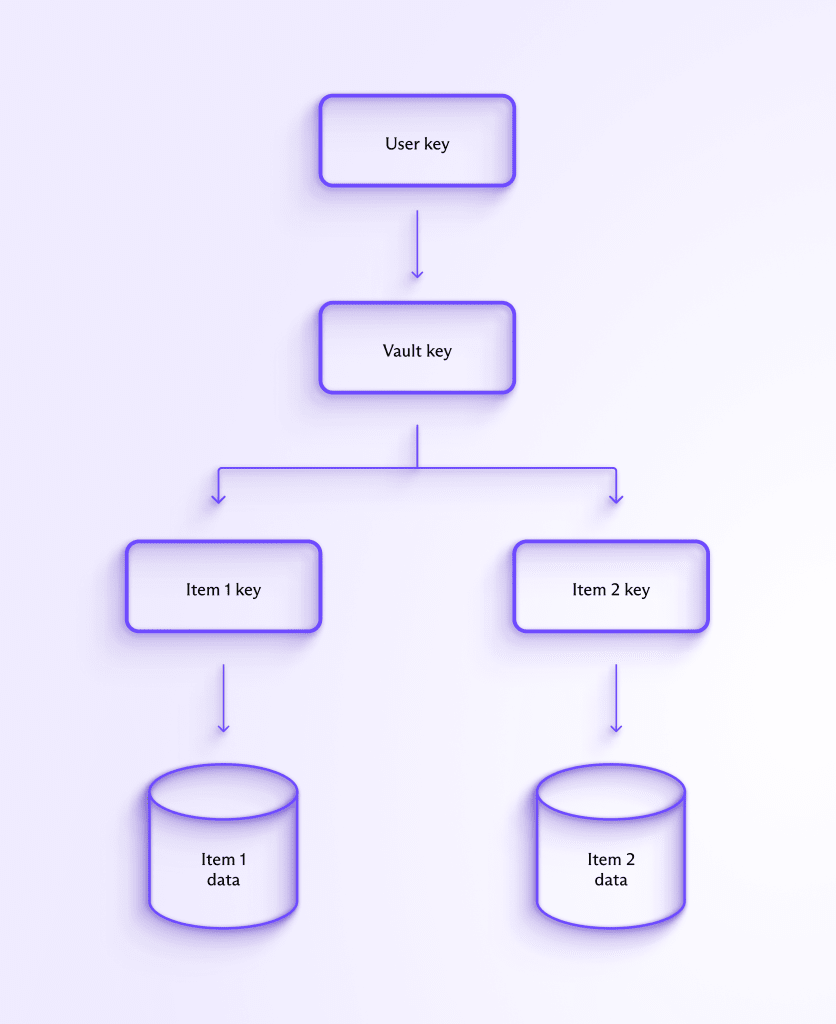
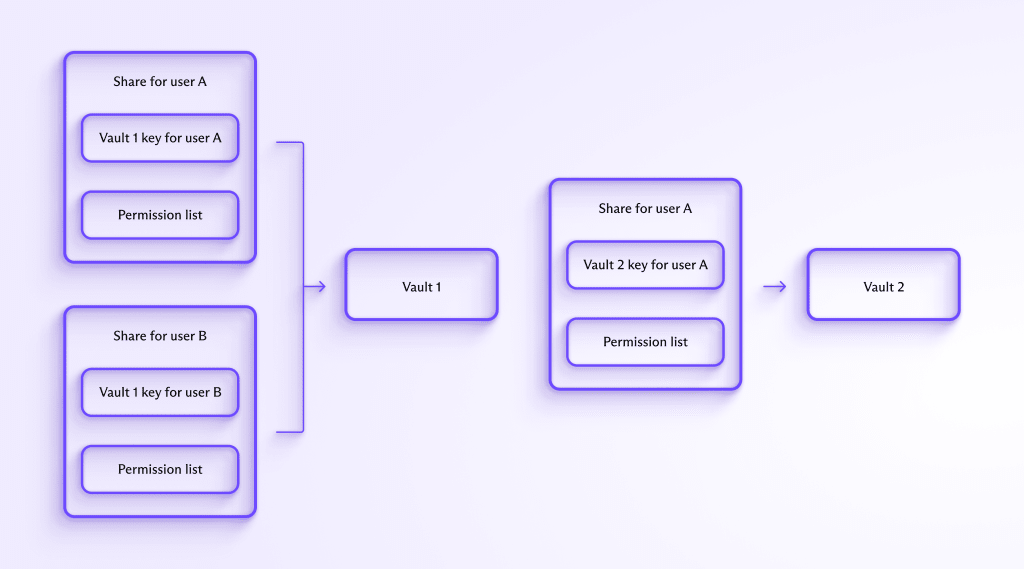
When you create a vault, Proton Pass generates a 32-byte random vault key. This key is encrypted and signed with your user key, ensuring only you can decrypt the vault key and nobody (not even Proton) can read or create new vault keys. If several users have access to the same vault, Proton Pass will encrypt the vault key with each user’s public user key. This makes it easy to securely share access to vaults.
Once you have access to the vault key, all items in Proton Pass are encrypted using 256-bit AES-GCM.
Item encryption
Each vault can contain multiple items, such as logins, notes, and aliases. When you create a new item, Proton Pass generates a 32-byte random item key. Proton Pass encrypts that item using the newly generated item key, which itself is then encrypted with your vault key. Both the item key and the item data are encrypted using 256-bit AES-GCM.
Whenever you update an item, Proton Pass encrypts the new data using the previously generated corresponding item key. By using individual item keys for each item, Proton Pass lets you share specific items with other users without sharing the vault key, allowing for more fine-tuned access control.
This approach enables Proton Pass to respect the security principle of least privilege by providing the minimum number of cryptographic keys necessary to access only the data shared.
Sharing
The Proton ecosystem already has open-source, publicly audited, and battle-tested secure sharing encryption models for Proton Drive and Proton Calendar, and we’ve leveraged this experience to design Proton Pass. The Proton Pass encryption model enables you to share your vaults with others, and we plan on adding more sophisticated sharing functionalities as Proton Pass evolves. Currently, you must be a vault administrator to share your vault keys.
Sharing encrypted information requires sharing and distributing public keys, which creates the potential for man-in-the-middle (MITM) attacks, specifically the distribution of fake public keys. In addition to user keys, each Proton user has one or more address keys for each email address associated with their account.
If you’re the vault administrator, you can share your vault key and Proton Pass will encrypt it with your recipient’s address key, ensuring only they can access it.
After your intended recipient receives your encrypted vault key, they will validate its signature using your address key. This step verifies that the invitation legitimately came from you. Once the signature has been validated, Proton Pass will encrypt the vault key using your recipient’s user key and store it securely.
Conclusion
Like all Proton services, Proton Pass will be open source upon release. Anyone will be able to consult the source code to verify our security model. As with our other services, Proton Pass will also undergo regular independent security audits and these audit reports will be shared publicly as soon as they are available.
Finally, for interested security researchers, Proton Pass is eligible for Proton’s Bug Bounty program that offers awards of up to $10,000 for the discovery of bugs in Proton’s software.
This work was conducted by Adrià Casajús, Son Nguyen Kim, Carlos Quintana, Daniel Huigens, and Lara Bruseghini from the Proton identity and cryptography teams.






