Proton Sentinel
- Reading
- 3 mins
- Categories
- Mobile security
- Proton for business
- Security and privacy
Proton Sentinel is an advanced account protection program that provides maximum security for those who need it. It mitigates security threats by combining AI with human analysis.
Plans
Pass Plus, Proton Unlimited, Proton Duo, Proton Family, Proton Visionary, Proton Workspace Standard, Proton Workspace Premium.
In this article
How it works
Proton Sentinel uses AI and human analysis to make it much harder for an attacker to take over your account. When you enable Sentinel, you’ll get:
- Advanced security protection, including stricter challenges for suspicious sign-in attempts.
- Greater visibility on sign-in attempts and account activity.
- 24/7 escalation of suspicious sign-in attempts to security analysts who will review assessments made by our systems.
- Automatic escalation of security-related support requests to our security analysts.
Anyone on a supported plan can enable Sentinel. If you’re a journalist, activist, executive, or someone who deals with sensitive data and communications, we strongly encourage you to use it.
Note: If you share your Proton Account with someone else, we recommend enabling two-factor authentication (2FA) alongside Sentinel. Without 2FA, you’ll have a higher chance of being challenged when you try to sign in.
Learn more about how Proton Sentinel protects you
How to use Proton Sentinel
Enable Proton Sentinel
- Sign in to account.proton.me and open your Security and privacy settings.
- Turn on the Enable Proton Sentinel toggle.
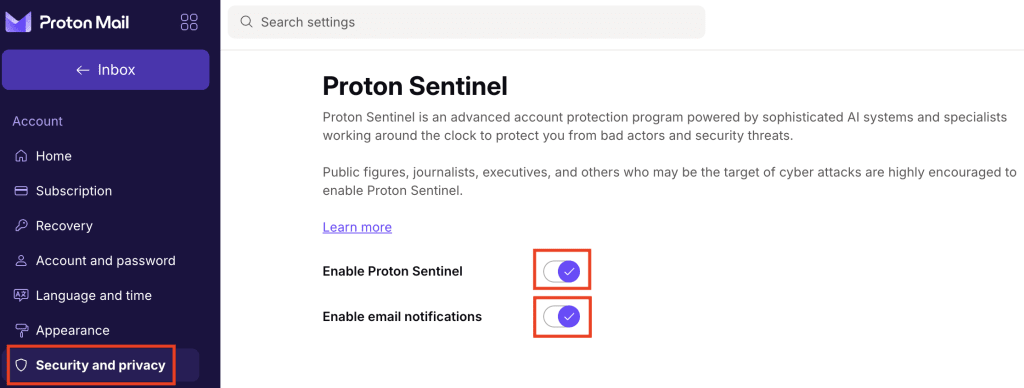
Proton Sentinel is enabled.
By default, we’ll notify you about suspicious activity by email. If you don’t want to be notified, toggle email notifications Off.
View security events
You can monitor Proton Sentinel security events from your activity monitor dashboard. Here’s how to enable account monitor:
- Sign in to account.proton.me and open your Security and privacy settings. Need help finding your account settings?
- Scroll to Activity monitor. Turn on the Activity monitor toggle.

Activity monitor is enabled.
- Records of future sign-in attempts and other account management events will appear here.
- In the Protection column, you’ll see which events Proton Sentinel has taken protective action on (if any).
- If you see any suspicious events, please contact us.
Show detailed security events
With activity monitor, you can allow Proton to record and show you additional event details. Enabling this feature while Proton Sentinel is on gives you access to some extra details that are only available to Sentinel users:
- In your Security and privacy settings, scroll to Activity monitor.
- Toggle Enable detailed events to On.

All future account monitor events will now show:
- Location: The approximate location (city and country) associated with the IP address.
- ISP: The Internet Service Provider associated with the IP address.
- Device: The device used for the sign-in attempt.
Proton Sentinel for organizations
Proton Workspace and Professional administrators can use Proton Sentinel to monitor authentication and security events for everyone in their organization.
Only admins can enable or disable the feature. When enabled, it applies to the whole organization and can’t be turned off for individual users.
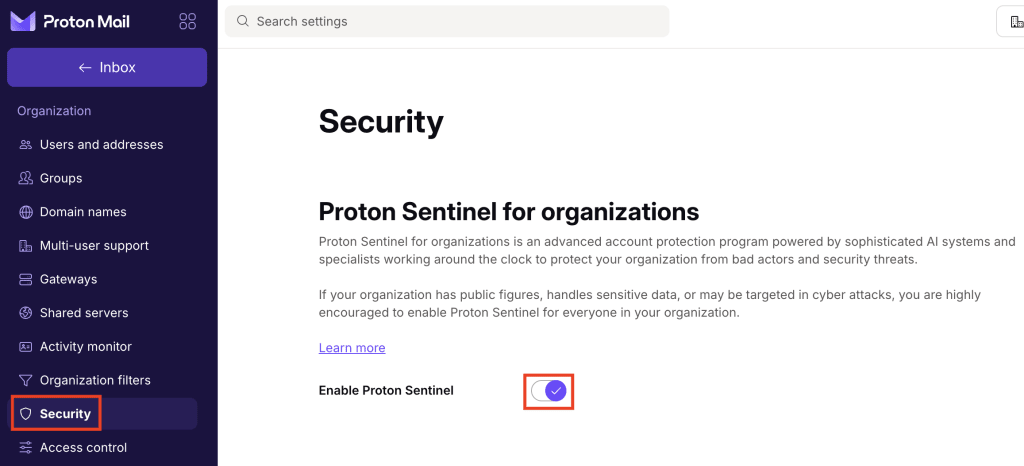
Enable Proton Sentinel for your organization
- Sign in to account.proton.me and open your account settings. Need help finding settings?
- Select Security from the sidebar (under Organization).
- Find the Proton Sentinel section and toggle Enable Proton Sentinel to On.
View and manage security events
Users: When Sentinel is enabled, everyone in your organization can:
- View sign-in and account events for their own account
- Enable and review enhanced security events for their own account
Administrators: With our business account monitor tool, admins can also enable, view, and manage security events for everyone in the organization. How to use business account monitor