Defend press freedom with Proton
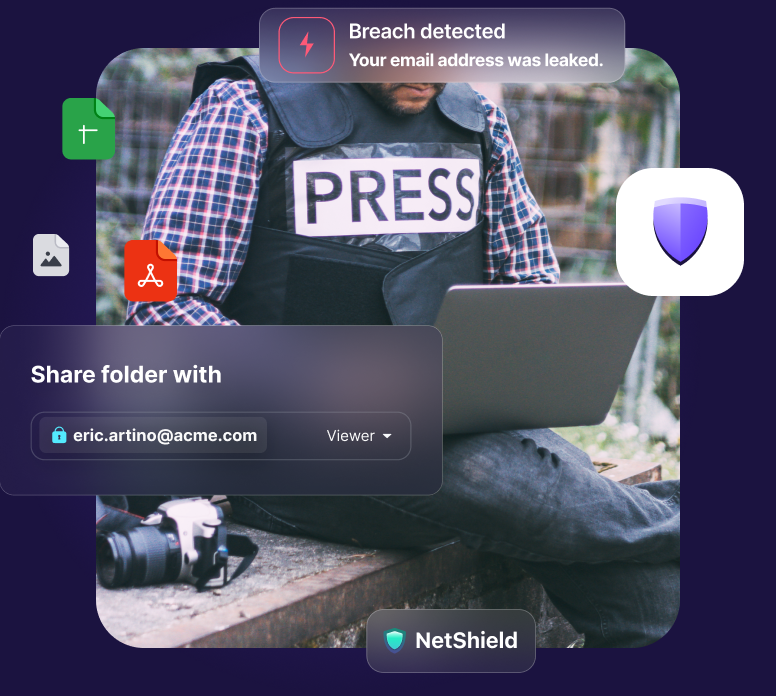
Journalists are under attack. Proton protects your emails, contacts, documents, and other data with end-to-end encryption to keep you and your sources safe.
Update: To counter unprecedented threats, we're now offering discounts on Proton for Business to news media.
Featured in
Proton helps journalists work safely and communicate securely
Our strong encryption and Swiss jurisdiction empower you to stay in control of your data at all times. Because we apply end-to-end and zero-access encryption automatically, your emails, calendar events, files, docs, and passwords are safe from data breaches and surveillance. And as a Swiss company, we cannot legally comply with any foreign subpoenas.
Every year, hundreds of journalists are killed or imprisoned for their reporting. Thousands more face surveillance, censorship, and fear of reprisals from government authorities or extremist groups. Our mission is to protect you with powerful and easy-to-use digital security tools.
How Proton protects journalists
Proton security starts with end-to-end encryption. Nobody — not even Proton — can see your emails, calendar events, files, and other data stored on our servers.
Communicate safely with your team and your sources
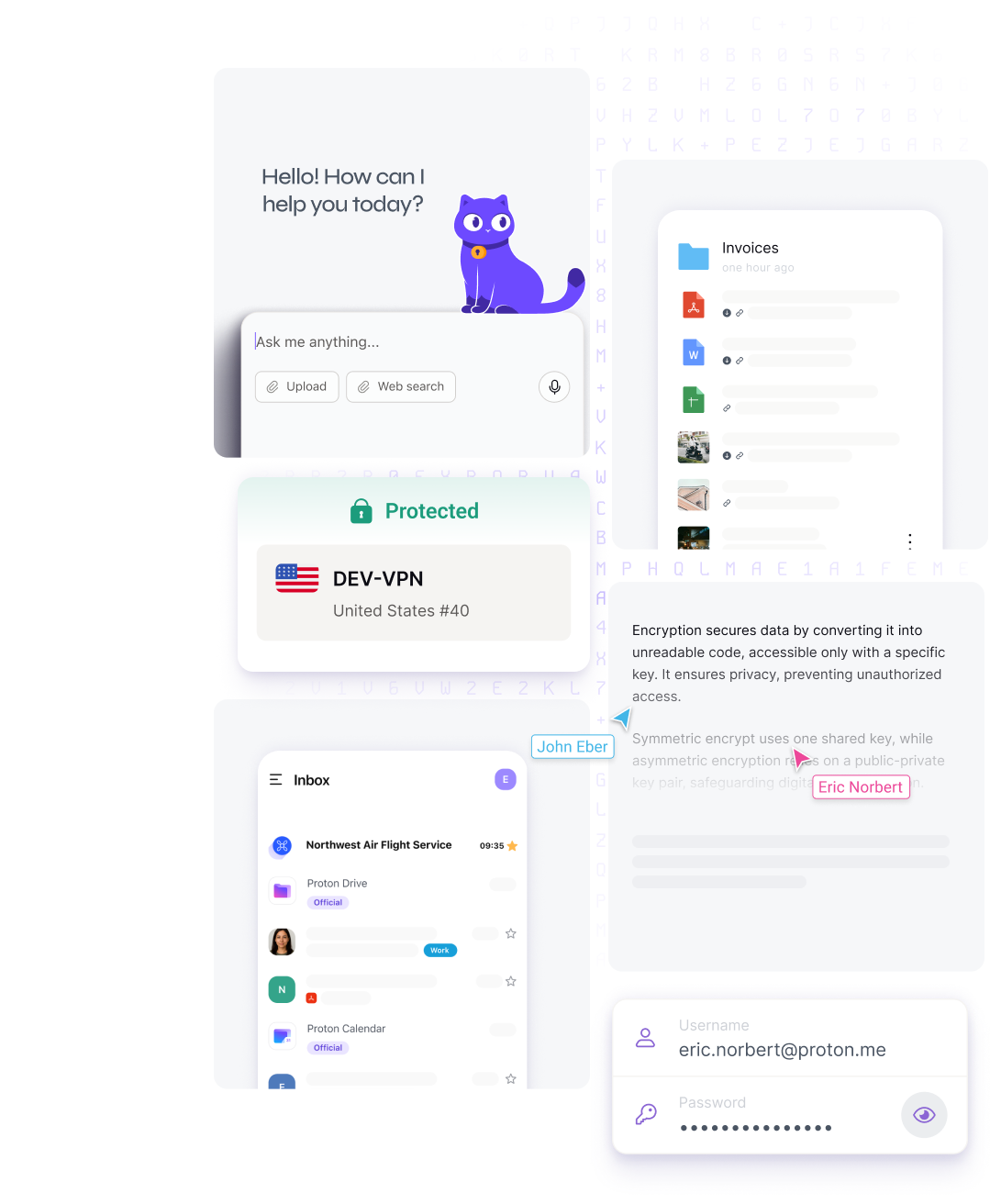
Proton Mail doesn’t (and can’t) scan your emails or share them with third parties. Whether you’re communicating with anonymous sources or handling confidential information, only the intended recipients will ever see your messages.
Securely store and share sensitive files
From whistleblower tips to research documents, Proton Drive’s encrypted cloud storage keeps your files safe. Access and share critical data across devices, knowing your files are fully protected against unauthorized access.
Collaborate on stories with encrypted docs
Whether you’re taking notes or drafting an article, Docs in Proton Drive is the only online document editor that lets you gather inputs and edits from others, in real-time, while maintaining total end-to-end encryption.
Unblock content and browse the web privately
We're the trusted VPN for journalists. Proton VPN hides your IP address and encrypts your web traffic to prevent surveillance, block trackers, and evade censorship so you can freely access the internet anywhere.
Safely manage passwords and credentials
Proton Pass protects your team’s sensitive credentials with end-to-end encryption, reducing the risk of unauthorized access or data breaches. Easily store and share passwords for accounts or databases.
Keep your team organized and on schedule
Our encrypted calendar gives your team a private way to schedule meetings, share video links, or coordinate interviews with sources. No one can see where you are or what you're doing, boosting your team's safety.
We've been committed to press freedom for over a decade
Since our founding in 2014, Proton has consistently promoted independent journalism around the world. Through our nonprofit Proton Foundation, we have directly supported media organizations including Charter’97, The Markup, Freedom of the Press Foundation, and the International Federation of Journalists’ Safety Fund.

Based in Switzerland
As a Swiss company, we can't share your data with anyone without a valid Swiss court order. Your data is protected by strong privacy laws and outside US or EU jurisdiction.
Open and transparent
Our apps are open source and independently audited, so anyone to verify and trust our code is secure. Transparency is one of our core values.
Community supported
Founded in 2014 through a crowdfunding campaign, Proton remains 100% funded by our community, not venture capital or advertising.

Protect your newsroom with Proton
Get our special deal for media organizations. Customize your plan for the needs and size of your team.
Frequently asked questions
- What qualifies an organization for Proton's special pricing for media outlets?
- Can media organizations access the full suite of Proton services at a discounted rate?
- How do I start using Proton at my media organization?
- Can Proton help keep anonymous sources and whistleblowers safe?
- What are the benefits of using Proton VPN for journalists?
- Where can I learn more about Proton's security safeguards?