Secure, seamless communication is the foundation of every business. As more organizations secure their data with Proton, we’ve dramatically expanded our ecosystem with new products and services, from our password manager(new window) to Dark Web Monitoring for credential leaks.
Today we’re introducing several new and easy-to-use features for Proton Mail and Proton Calendar to help teams collaborate more efficiently.
From painless meeting scheduling to faster email management, we developed all these features in response to specific feedback from the community. (So if you have any feature suggestions, please reach out to us.) As always, these are designed to be simple so your team can use them without any training or interruption to your workflow.
You can already start using all these features right now with any Proton for Business plan(new window).
Proton Calendar
See the availability of colleagues and avoid meeting conflicts
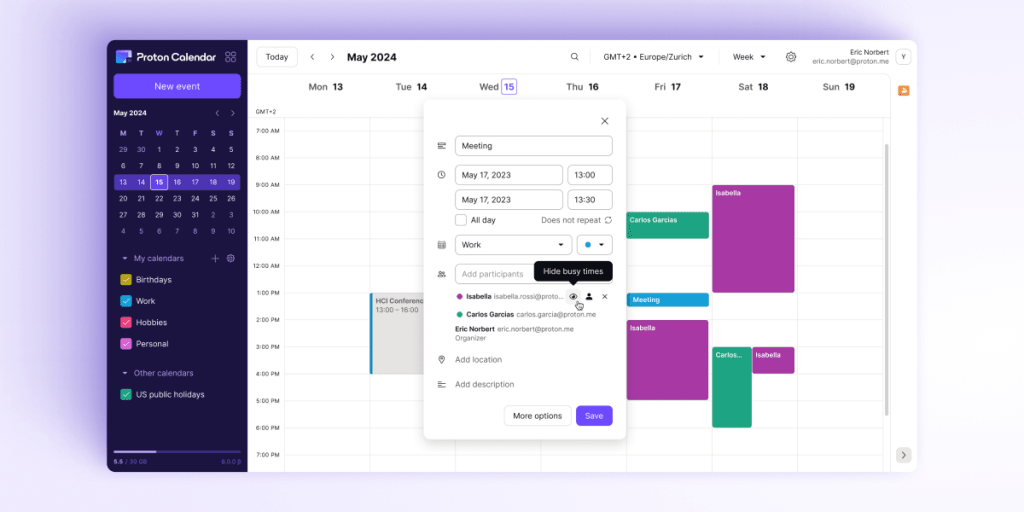
You and your colleagues can now see the availability of meeting participants so you no longer need to ask them for the best time to meet. You’ll see everyone’s availability in your organization’s shared calendar. This allows you to save the time you would have spent coordinating, send an invite in seconds, and avoid meeting conflicts.
You also have the flexibility to choose whether you want to share your availability with others.
Streamlined calendar views to improve efficiency
Proton Calendar on iOS now includes a “week view” to give you better visibility of your meetings and weekly availability.
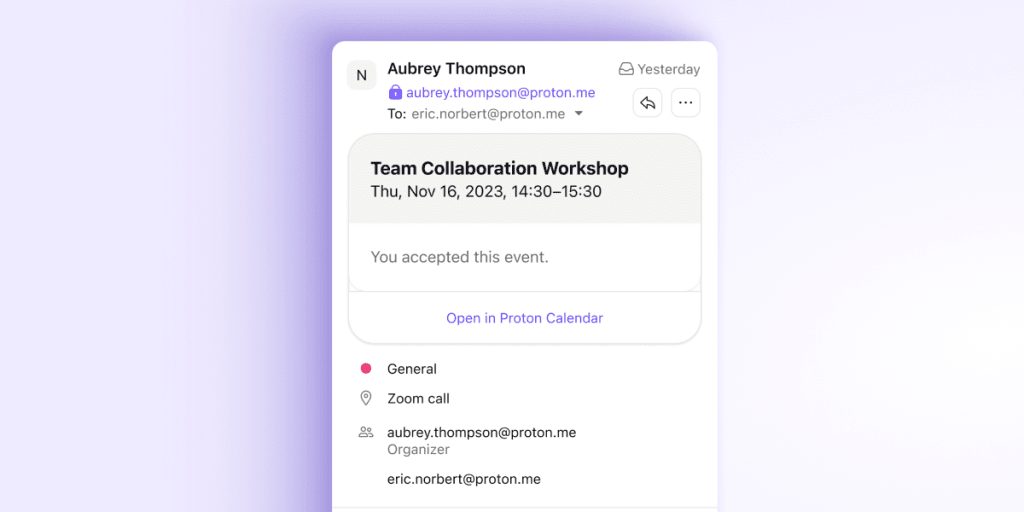
With the new event summary integration between Proton Calendar and Proton Mail, you can also easily see event summary details in invites you receive on the Proton Mail iOS app. This includes key event information and the option to open Proton Calendar with one tap to check your availability.
Proton Mail
Quicker inbox management on the go
Our new “Jump to next” feature for Proton Mail on iOS allows you to quickly sift through your inbox by automatically displaying the next email when you delete or archive one. This feature is optional and can be enabled from your settings, ensuring that you can keep up with your emails efficiently while on the go.
You can also snooze your emails and be reminded about them at a more convenient time. This ensures you’ll never forget or miss an email, as it will reappear in your inbox when you’re ready to take action.
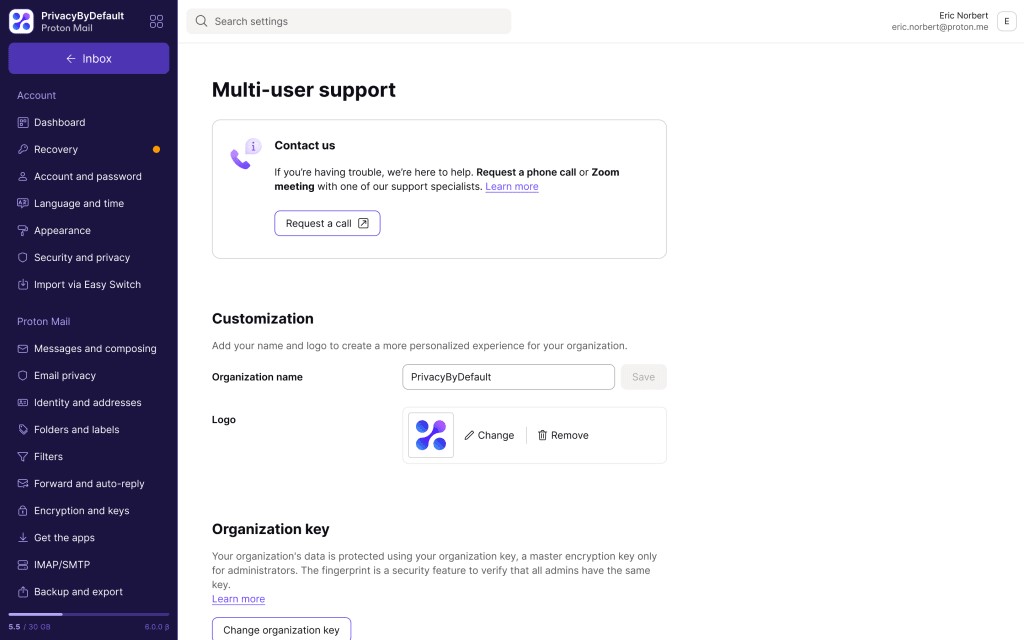
Keep your business on brand with your logo

As your organization’s admin, you can now customize the company’s digital work environment by adding your company’s logo to the Proton Mail web interface.
Logo customization is exclusively available to subscribers of our business plans — specifically those with Proton Business(new window), Pass Business(new window), Proton VPN for Business(new window), and Proton Enterprise(new window) — to tailor your Proton experience to your brand.
Proton Mail desktop app
In March, we launched the Proton Mail desktop app — available for Windows and macOS, with a Linux version in beta. Included in our Business plans, these desktop apps complement our existing web and mobile applications, allowing you to keep your emails private across all devices without using a browser.
At Proton, we believe you should be able to access your email however you want to without compromising your privacy or security. You can get the app right now(new window).
We have even published an easy-to-follow tutorial to guide you through how to get started with the Proton Mail desktop app.
Looking forward
In 2024, even more features are coming to the Proton ecosystem to further enhance your ability to run an efficient, organized, and productive business.
But those features would not be possible without the tens of thousands of businesses and professionals who already use Proton in their work. We are always listening to your valuable feedback and requests to build better features for your business needs. Thank you for your support and trust.
Switching to Proton Mail not only helps your business with easy-to-implement tools to manage communications and cybersecurity, but it helps create a better internet and a future where privacy and security are the default.
If your business seeks the highest level of digital privacy and security and would like to migrate to Proton, you can learn more at https://proton.me/business(new window) or contact our Sales team(new window).






