Learn all about TLS/SSL certificates, the digital files that help to authenticate and secure data transfers across the internet.
Whenever you send or receive information on the internet, it passes through a network of multiple computers to reach the destination. Historically, any of these computers could read your data because it wasn’t encrypted.
Much of your data is sensitive — and valuable to hackers. It can include private communications that aren’t end-to-end encrypted, financial information, and even login credentials (for web apps that don’t use the Secure Remote Password protocol).
To protect sensitive data, security experts developed a standard protocol to send and receive internet traffic: Secure Sockets Layer (SSL). SSL later evolved into Transport Layer Security (TLS), which has now largely replaced SSL.
We explain how TLS and TLS certificates work, their weaknesses, and the extra steps we take at Proton to secure TLS-encrypted connections.
What is TLS?
How does TLS work?
What is a TLS certificate?
How does a TLS certificate work?
Why trust certificate authorities?
What are the weaknesses of TLS certificates?
Proton’s TLS security precautions
What is TLS?
Transport Layer Security (TLS) is an encryption protocol that provides secure connections between servers and applications on the internet.
Before TLS, websites and apps used the Hypertext Transfer Protocol (HTTP)(new window) to transfer data over the internet, which wasn’t designed to be secure. Today, most use sites use the Hypertext Transfer Protocol Secure (HTTPS), an extension of HTTP that uses TLS encryption.
When you connect to a website that uses HTTPS, TLS verifies the identity of the website’s server and encrypts your connection, preventing hackers from intercepting any data transmitted between your device and the site. In this way, TLS provides privacy and security for the data transmitted between your browser and the website, and you can be sure the data hasn’t been tampered with.
How does TLS work?
TLS uses public-key cryptography(new window) to verify the authenticity of a website. Every website that uses HTTPS (TLS) generates a mathematically related key pair:
- A private key, which is kept secret and used to sign data
- A public key, which anyone can use to verify that data
When your browser tries to connect to a website (a domain name like proton.me), the server creates a digital signature using the private key, which the browser verifies using the corresponding public key. If successful, this verification proves you’re connecting to a server that belongs to the domain name you’re visiting.
But how can your browser be sure the server’s public key really belongs to that domain? To solve this problem, TLS uses TLS certificates to help verify the identity of the server you’re connecting to.
What is a TLS certificate?
A TLS certificate is a type of digital certificate issued by a certificate authority (CA) to certify the ownership of a public key.
TLS certificates usually contain the following information:
- The subject domain name (for example, proton.me)
- The name of the issuing CA
- Additional subject domain names, including subdomains, if any
- The date of issue
- The expiry date
- The public key used to verify data (the subject organization keeps the private key secret)
The CA digitally signs the certificate, so if you trust the CA, you can be sure the public key belongs to the owners of the subject domain name.
How does a TLS certificate work?
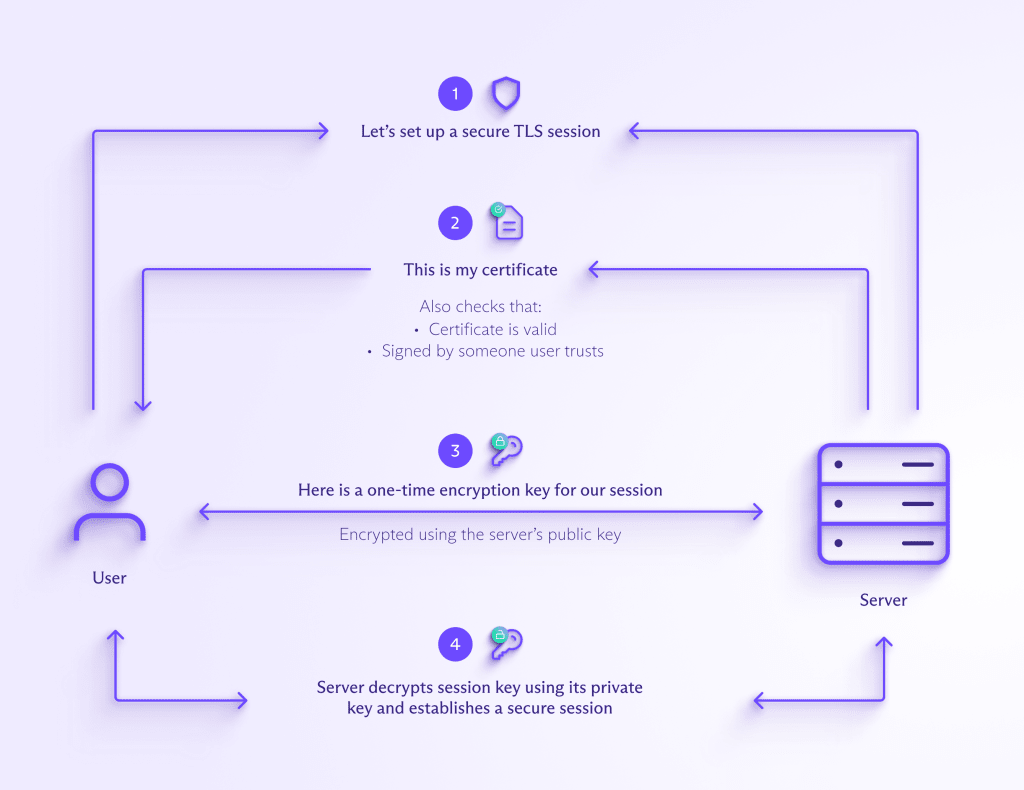
When you try to connect to a website using HTTPS, the website server sends your browser its TLS certificate.
Your browser then verifies that the certificate is valid and digitally signed by a trusted CA by comparing it with information it stores about trusted CAs. This verification process uses public-key cryptography like RSA(new window) or ECC(new window) to prove the CA signed the certificate.
The signed certificate verifies the website server’s public key, which confirms that you’re communicating with the genuine server of the website you’re visiting, like https://proton.me, and not a hacker.
The server also authenticates a key exchange, resulting in a one-time session key that is used to send encrypted and authenticated data between the clients and the server.
In simplified terms, here’s how your browser and a website server establish a secure connection using a TLS certificate.
Most browsers display a padlock to show that your connection is secure and the site’s TLS certificate is valid.
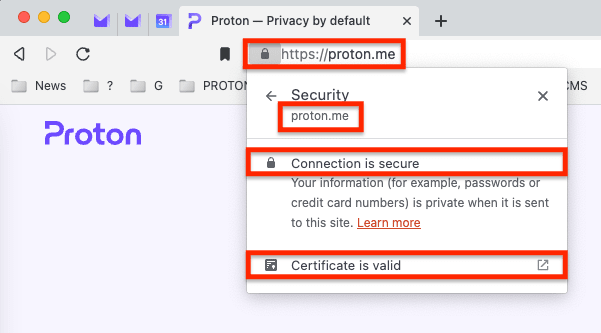
To make sure you’re securely connected to a website using HTTPS, check the following:
- The padlock is displayed: This indicates that the connection is secure.
- The URL is correct: Check it’s https://proton.me, not pr0ton.me, protan.me, or some other fake look-alike. If you’re connecting to a subdomain, like https://mail.proton.me(new window) for the Proton Mail web app, check it’s precisely mail.proton.me, not mail-proton.me or mail.proton.co.
If all the above are correct, your connection is secure, provided you can trust the certificate authority that issued the TLS certificate.
Why trust certificate authorities (CAs)?
As CAs are responsible for verifying that the data you received came from the server you expected, they play an essential role in the internet. They’re the backbone of secure internet communication, helping encrypt billions of data exchanges and transactions by issuing millions of digital certificates every year.
There are many precautions that CAs take to ensure the security of the certificate issuance process. For example, CAs store the private keys in a hardware security module(new window) so they can’t be extracted (although this doesn’t prevent certificates from being mistakenly signed).
Additionally, CAs follow various policies set by the CA/Browser Forum(new window) that establish and maintain security standards. All these measures help ensure the TLS certificate verification process is trustworthy.
The trust model of TLS relies on two major elements:
- Root certificates (also known as trusted roots)
- The server’s certificate
Your browser will automatically trust any certificates issued by a CA, provided the CA’s root certificate is installed in the certificate store of your device. Every device has a certificate store, a local collection of root certificates from trusted CAs. Only CAs that can demonstrate that they adhere to the policies set by the CA/Browser Forum are trusted by root certificate stores.
What are the weaknesses of TLS certificates?
Although TLS certificates are generally secure, here are some ways hackers can attack and potentially compromise TLS.
Certificate store poisoning
If an attacker infects your computer with malicious software (malware)(new window), they could gain access to the digital certificates stored on your device and insert a root certificate. They could then impersonate a website by fraudulently responding to your website requests.
Someone might ask you to install a root certificate on your device, for example, to access an internal site on a corporate network. Never install a root certificate on a personal device.
Similarly, never access Proton or other important accounts from a device with a root certificate installed, or from a public or shared device you don’t own, especially if it was given to you by someone you don’t completely trust.
Attacking CAs directly
For TLS certification to work, the CA must be secure. Any breach of the CA could lead to the incorrect or fraudulent authorization of keys.
CAs have occasionally been compromised, as we saw in the data breaches at Comodo and DigiNotar(new window) in 2011, which allowed attackers to issue fraudulent certificates.
Mistakenly issued certificates
Users rely on CAs to authenticate the server they connect to. However, sometimes CAs make mistakes in issuing certificates that present a vulnerability that hackers can exploit.
When combined with an insecure internet connection, an attacker could use a mistakenly or fraudulently issued certificate to compromise your connection with a server.
If these vulnerabilities exist, can you trust CAs? Yes, but it’s sensible to take precautions to minimize these risks.
Proton’s TLS security precautions
While CAs and TLS-based encryption methods are relatively secure, there’s always scope for improvement.
At Proton, we aim to enhance privacy and security for everyone online. Here are some of the additional steps we take to secure TLS-encrypted connections.
DNS certification authority authorization (DNS CAA)
As public concern about the security of CAs grew following the CA data breaches in 2011(new window), work on new security measures gathered pace. One of the outcomes of that work was DNS certification authority authorization (DNS CAA), which blocks the issuance of incorrect certificates.
DNS CAA allows domain owners to use a DNS resource record to specify which CAs are allowed to issue certificates for a given domain. If a CAA record exists, only the CAs listed in that record can issue the host’s certificate.
Although this provides some protection against unintended certificate misuse, it’s very difficult for users to detect if a CA ignores the CAA advisory. That’s why we use certificate transparency.
Certificate Transparency (CT)
To ensure the validity of certificates and prevent them from being mistakenly or fraudulently issued, all CAs post the certificates they generate on public log servers known as Certificate Transparency (CT) logs. These servers send a signature to the CA promising to publish their certificate.
We serve an Expect-CT header, which tells the browser to require the presence of this signature. We also have monitoring and auditing servers that check the CT log for all promised certificates meant to be published.
Together, all these measures make it highly improbable for anyone, including a state actor, to generate a TLS certificate for proton.me and use it to intercept connections without being detected.
TLS certificate pinning
Certificate pinning is a process that links a service to its specific public key. Once a certificate is established for a particular service, it’s permanently pinned to the service.
If multiple valid certificates exist for a given service, the pins are merged into a pinset. To validate a pinset, at least one element from the service must match the elements in the pinset. We pin the public key of our certificates in all our native apps.
At Proton, our work on TLS is part of our goal to give everyone privacy and security online. That’s why we offer free end-to-end encrypted Proton Mail, Proton Calendar, Proton Drive, Proton Pass, and Proton VPN(new window) — so everyone can be free online.
Our free accounts are funded by paying members of the Proton community, not by exploiting your personal data. If you want to support our mission to give everyone privacy and security online, sign up for a paid plan.
Together, we can build a better internet where privacy is the default.





