Data breach protection: Is your business secure?
Explore best-practice tools and strategies to protect your organization from data breaches and credential theft, including business password managers, internal training, DLP software, and intrusion detection systems.

How do data breaches happen?
A data breach occurs when unauthorized users access sensitive information or when it is unintentionally exposed. The most common causes include weak or reused passwords, brute-force cyberattacks, phishing scams, and technical vulnerabilities, such as unpatched software.
Organizations can suffer financial and reputational damage, regardless of how a data breach occurs. And a single incident can cost a small firm over $1 million.
Find out how to prevent a data breach and explore our data breach observatory.

Best data breach protection strategies and tools
With small- and medium-sized businesses (SMBs) accounting for 70% of breaches in 2025, it’s more important than ever to implement enhanced security protections. To protect your organization from embarrassing and costly privacy breaches, a range of safeguards is available.
Password hygiene
Weak and reused credentials are one of the easiest ways for bad actors to bypass your security. Enforcing good password hygiene is a simple and effective way of reducing the chance of a data breach at your company. Proton Pass for Business enables companies to enforce password policies, monitor access and usage, receive breach alerts, and perform hygiene checks on existing credentials.
Employee security training
Human error frequently plays a significant role in data breaches. Occasionally, it’s due to flaws in software setups. Sometimes, it’s as simple as leaving a laptop open or losing a phone. But most often, it’s the result of a sophisticated phishing attack.
Training employees to be aware of potential risks and to know how to respond in various situations can significantly reduce the risk of a data breach resulting from human error.
Internal security policies
Policies governing data handling and access control are essential for protecting against data breaches. They may include data classification, least-privilege access, password managers, and data disposal processes.
For employees using personal or off-site devices, policies for acceptable use, remote work, and BYOD help set security standards. This might include requiring VPNs or other encryption tools, enforcing MFA, and ensuring proper handling of company data.
IT tools for data breach protection
Data loss prevention (DLP) software is a widely used tool that monitors and controls the transfer of sensitive data to prevent unauthorized sharing or leaks. DLP software might be combined with a continuous security monitoring (CSM) tool to provide real-time threat detection, and an encryption tool to protect data by encrypting it and making it unreadable even if someone were able to leak or intercept it.
Other standard tools include intrusion detection systems (IDS) and security information and event management (SIEM) software, which help organizations collect and analyze security data across their networks, making it easier to identify and respond to potential threats before they cause damage.
How Proton for Business can protect your company from a data breach
Proton offers businesses a suite of products designed specifically to ensure the security of your workplace and help your organization meet GDPR, HIPAA, CCPA, and other privacy regulations.
Business password manager
Our business password manager enables you to enforce strong passwords, securely share logins, and control access to your accounts. Business users also benefit from Sentinel, our high-security program that combines artificial intelligence monitoring with human expertise to detect, identify, and challenge any suspicious account takeover attempt.

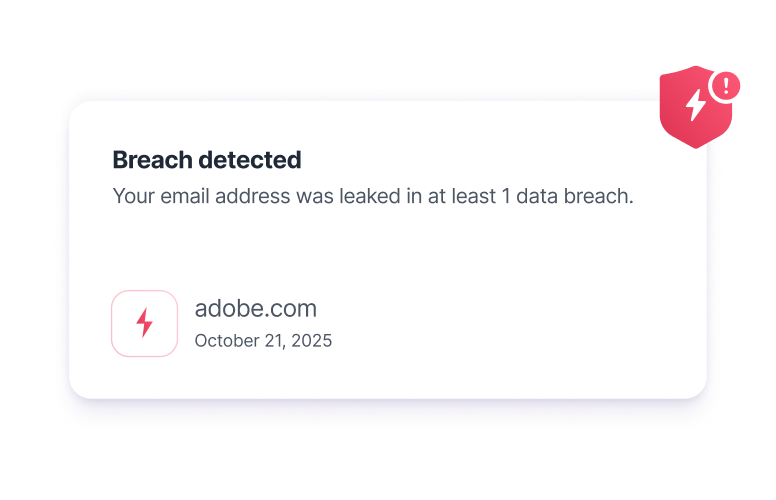
Real-time breach information
Proton’s Dark Web Monitoring tool scans hidden parts of the internet for email addresses that have ended up in illegal data markets. Our system will alert you if it finds leaked details of any of your accounts for third-party websites. You’ll receive comprehensive information about the breach, along with actions you can take to mitigate any risk.
Additionally, Proton’s Data Breach Observatory is a free tool that empowers you with real-time intelligence about data breaches. You can use the Observatory to investigate how businesses like yours are being affected — from types of data being stolen, to industries most frequently targeted — and strengthen your business protections accordingly.
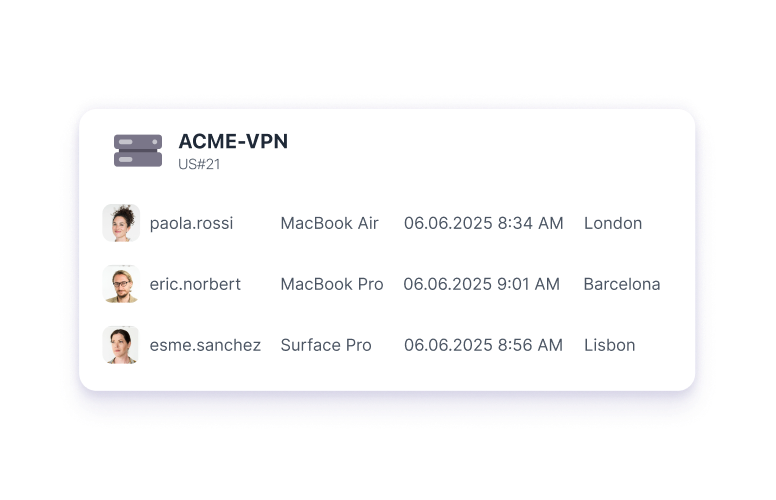
Business VPN
A business VPN encrypts data within your network, shielding sensitive information from hackers and insider threats. It enables you to restrict logins so only approved devices and networks can use private gateways, and assign and segment permissions so employees only see what they need. With Proton VPN, you can ensure that your data is always secure, even when accessed remotely or on public WiFi networks.
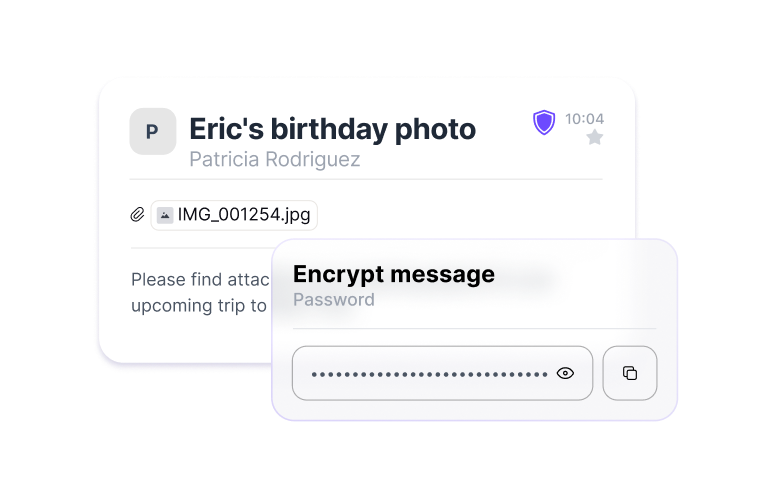
End-to-end encryption
Proton uses end-to-end encryption by default to secure your passwords, VPN traffic, emails, calendar events, your data on cloud storage, and more. Even if your data were leaked or intercepted, it would be impossible to decrypt.
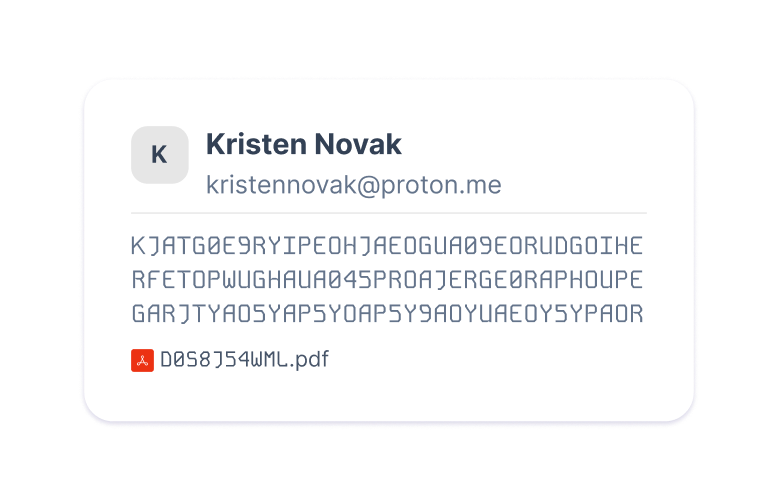
Zero-access architecture
Proton uses zero-access architecture so we can never access your data. We instantly encrypt emails from other service providers, queries in Lumo, and other data on our servers using your public key, so we cannot decrypt your messages.
Stop breaches before they start
Protect your data with a business password manager. Create and enforce strong passwords, share logins securely, and control access to your accounts.
FAQ on data breach protection
- What is a data breach?
- What are the most common causes of data breaches?
- How can businesses prevent data breaches?
- How does a password manager help with data breach protection?
- What should my business do in the event of a data breach?
- What’s the difference between a data breach and a privacy breach?