Data loss prevention (DLP) strategies to protect your business
Find out more about data loss prevention (DLP), including the best software for your needs, how a business password manager can help, and what else you can do to protect your business from data theft.
What is data loss prevention?
Data loss prevention (DLP), also known as data loss protection, is a set of tools, policies, and practices that help organizations detect, prevent, and respond to security risks affecting data.
Your data faces different risks depending on which state it’s in: at rest, in use, or in motion.
Data at rest
Data that is not actively in use but is stored on hard drives, in databases, or in cloud storage.
Data in use
Data that is being accessed, modified, or processed by authorized users or applications.
Data in motion
Data that is moving between locations, such as via email exchanges or file transfers. Also referred to as data in transit.
Different loss prevention techniques are needed depending on the type and state of data you need to protect. For most organizations, this will typically involve a combination of policies, DLP software, and privacy tools, such as password managers.
Common causes of data loss
Businesses face a wide variety of data threats. Some of the most common risks include:
Insider threats
Data loss commonly occurs when employees mistakenly send confidential data to the wrong recipient or upload it to an insecure platform. Less commonly, you may find that employees or contractors are stealing or leaking sensitive information.
External attacks and data breaches
Weak or leaked passwords are one of the most common ways attackers gain access to accounts without hacking systems at all. Phishing and social engineering attacks, where hackers trick employees into revealing usernames, passwords, and other sensitive information, are also widespread. You may also encounter issues with malware and ransomware, where cybercriminals encrypt or steal critical files, sometimes demanding a ransom. Lastly, man-in-the-middle attacks(new window) are a common threat to data in transit if networks are not properly encrypted.
System and human errors
Misconfigured systems, lost or stolen laptops or smartphones, and simple human errors, such as accidentally deleting files or failing to install software updates, can all leave data vulnerable to unauthorized access.
Compliance failures
Failure to meet industry or governmental standards can lead to unprotected regulated data (like health records or payment details), making it vulnerable to threats and possibly resulting in fines and penalties.
Types of data loss prevention software
The type of DLP software you choose will depend on the size of your organization, the industry you’re in, and the IT infrastructure you’re running. You may need more than one type of solution to protect all your sensitive data.
Here are the most common categories:
Business password manager
Deploying a business password manager enables your organization to securely store and manage company passwords. A password manager makes it easier for employees to create strong, unique passwords and use 2FA on all their accounts. It also encrypts your passwords and other sensitive information using end-to-end encryption, keeping them secure even in the event of a data breach.
Best for: Reducing the risk of data breaches as a result of weak or reused passwords, as well as phishing attacks.
On-premises DLP
This software is deployed within your organization’s own infrastructure, giving you control over data stored on servers, databases, and endpoints. It’s highly customizable and often preferred by industries with strict compliance requirements.
Best for: Protecting sensitive data that remains within internal systems and networks.
Cloud-native DLP
Cloud-native DLP is designed for businesses that rely heavily on SaaS apps and cloud storage. Delivered as a service, it scales easily and protects data that lives in cloud apps or moves between them.
Best for: Organizations that use Google Workspace, Microsoft 365, Salesforce, or other SaaS platforms.
Endpoint DLP
This software runs directly on devices, including laptops, desktops, and mobile phones. It prevents unauthorized copying, sharing, or printing of files and protects data even when devices are offline.
Best for: Businesses with employees who work remotely or handle sensitive files on personal devices.
Network DLP
Network DLP software monitors data in transit as it moves across company networks. It can encrypt, block, or quarantine sensitive information before it leaves the network.
Best for: Preventing data from leaving the organization through email or unapproved network channels.
Cloud/App DLP
Cloud or application-level DLP solutions focus on securing data inside specific SaaS platforms, APIs, and cloud storage services. The software can control who can download, share, or sync files, ensuring that sensitive files aren’t exposed by mistake.
Best for: Companies that collaborate heavily in third-party software platforms.
Email DLP
Specialized for email security, email DLP scans messages and attachments to detect sensitive content and can block, quarantine, or force encryption of risky emails.
Best for: Businesses where employees frequently send documents or sensitive information via email, which remains one of the most common methods for data leaks to occur.
Most businesses combine multiple DLP solutions to create a layered defense that protects data at rest, in motion, and in use.
How to secure your business data
A robust DLP strategy requires both policies and technology. Here are six best practices you can implement to protect your data.
1. Implement access controls
Restricting access prevents unauthorized employees or external parties from handling sensitive files.
How DLP software helps: Ensuring only authorized employees can access, download, print, or share sensitive files by integrating with identity and access management (IAM).
Best solutions: Endpoint DLP and network DLP tools enforce role-based permissions at the device and network level, while a business password manager gives admins the ability to manage and monitor user access to password-protected tools and files.
2. Encrypt everything
Data should be encrypted both at rest (on servers or endpoints) and in transit (across the internet).
How DLP software helps: Enforcing automatic encryption before files leave your network or when they are stored in the cloud.
Best solutions: Network DLP for traffic in motion, storage DLP for files at rest, and a business password manager to encrypt all login credentials.
3. Classify and label your data
Identify which data is public, internal, confidential, or highly sensitive and apply labels that guide how information is handled and who has access to it.
How DLP software helps: Scanning files, emails, and documents to detect sensitive data and apply classification labels.
Best solutions: Storage DLP and cloud DLP tools help with data discovery and classification.
4. Educate employees
Human mistakes — like emailing confidential files to the wrong recipient — are a leading cause of data leaks.
How DLP software helps: Sending real-time prompts and warnings to alert employees when they attempt to move or share restricted data, and implementing role-based permissions.
Best solutions: Endpoint DLP and cloud DLP monitor user actions at the device and app levels. A business password manager can prevent unauthorized access and enables admin visibility into access and usage.
5. Backup and recovery
Data backups ensure that if files are lost, corrupted, or encrypted by ransomware, businesses can recover quickly.
How DLP software helps: Ensuring sensitive data is protected before being stored by working in conjunction with backup tools. Some solutions can flag if regulated data is improperly backed up.
Best solutions: Storage DLP ensures backups don’t contain unprotected sensitive files.
6. Monitor and respond in real time
Rapid detection and response are crucial to stopping a breach before it escalates.
How DLP software helps: Flagging suspicious activity (like bulk downloads or large email attachments) using machine learning and anomaly detection. It can also automatically block, quarantine, or encrypt data in response.
Best solutions: Network DLP (to monitor traffic), endpoint DLP (to track device behavior), and integrated DLP suites (for a unified view).
How a password manager can support your DLP strategy
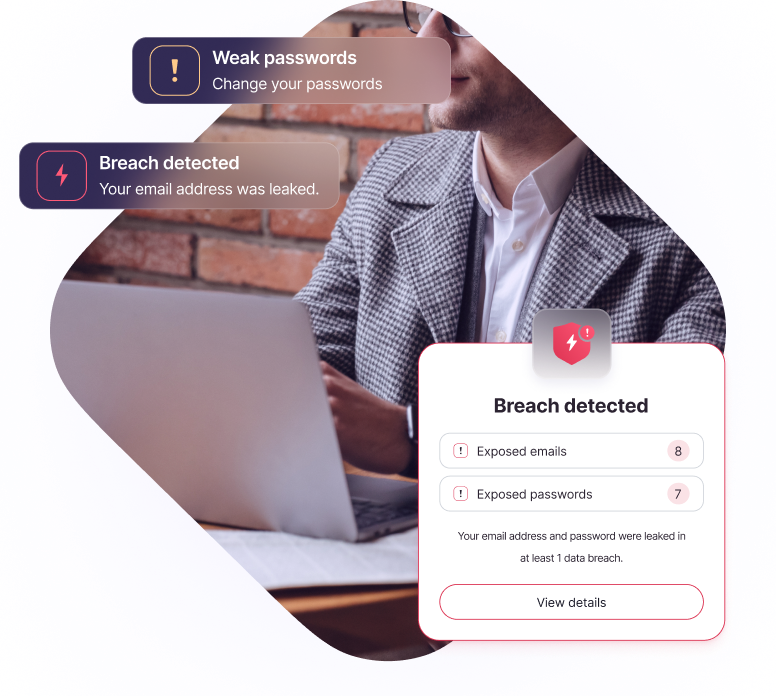
A business password manager can strengthen your DLP strategy by protecting data at rest and reducing the risk of unauthorized access. Proton Pass for Business makes it easy for your team to create strong, unique passwords, store them securely, and access them whenever they need. It also gives admins visibility into credential health and breach alerts, supported by activity logs for oversight.
Where traditional DLP software focuses on monitoring and enforcing policies around sensitive information, Proton’s tools shield your data from hackers and insider threats.
Proton Business Suite, which includes Proton VPN, Mail, Drive, and Calendar, as well as Proton Pass, ensures that communication, file sharing, and collaboration remain private and encrypted end-to-end.
By layering these privacy tools on top of your DLP software, you can create a more resilient defense for your business.
FAQ: Data loss prevention
- What is data loss prevention?
- Is a password manager a type of DLP?
- Does DLP software spy on employees?
- Is DLP required for compliance?