Cloud data security that puts you back in control
Keep your business data safe in the cloud — and out of anyone else’s hands. Proton Drive improves your cloud data security and privacy by protecting your business files from unauthorized access, surveillance, AI training, and data leaks.
What is cloud data security?
Cloud data security is a set of technologies, policies, and practices used to protect data that is stored, processed, and transferred using cloud storage. Its goal is to keep data safe from theft, leaks, unauthorized access, loss, and corruption while providing access to legitimate users.
The three pillars that guide information security standards such as ISO 27001 also sit at the foundation of cloud data security:
Confidentiality: Keeps your data in the right hands by ensuring only authorized people and systems can access it.
Integrity: Protects your data from unwanted changes, so you can trust that it stays accurate and reliable.
Availability: Makes sure your data and cloud services are ready and reachable whenever legitimate users need them.

How cloud data security works
An effective cloud data security strategy adds several layers of protection as data moves to, from, and within the cloud:
1. Encrypts data during transfer
When you upload data to a cloud service, it is protected while traveling over the internet using secure encryption protocols such as HTTPS/TLS, the same technology used by online banking.
This encryption ensures that, even if attackers intercept your data during transfer, they can’t access or tamper with it.
2. Encrypts data during storage
In traditional cloud services, the provider decrypts your data after it arrives, then re-encrypts it for storage using server-side encryption and manages the encryption keys.
While this protects your data from external threats, it also means the provider can technically access your content when necessary — for things such as file scanning, AI features, personalized services, or anything else acceptable under its terms of service.
3. Controls who can access your data
Cloud data security systems use access controls to ensure only approved people can view, edit, or share your files — also known as the principle of least privilege.
This typically includes a combination of:
- User logins and passwords or passkeys to verify identity.
- Two-factor authentication (2FA) for an extra layer of protection.
- Permission settings that limit what each user can do.
For example, you can allow an employee to view a file without giving them permission to edit or share it. This helps prevent accidental data leaks, insider threats, or unauthorized access, especially as your team grows or works remotely.
4. Monitors and blocks security threats
An effective cloud data security platform actively monitors your organization’s cloud to detect and stop threats before they become a serious problem. It means watching for events like repeated failed attempts, access from unfamiliar locations, or brute-force login attacks.
When something out of the ordinary is detected, automated response mechanisms step in immediately to block access and alert administrators.
5. Creates backups and enables recovery
Your business can lose data due to human error, ransomware, hardware failure, or accidental deletion. A cloud data security platform helps by automatically creating secure backups of your data at regular intervals.
These backups are stored in separate, protected locations and are often versioned, so you can restore previous versions of files if they become corrupted, overwritten, or encrypted by ransomware.
How to improve cloud data protection for your team
Here are the best practices to follow for strong data security and privacy in your organization:
1. Use end-to-end encryption
End-to-end encryption (E2EE) ensures that only your business controls the keys to your data, and your cloud provider can’t view, scan, or access your files.
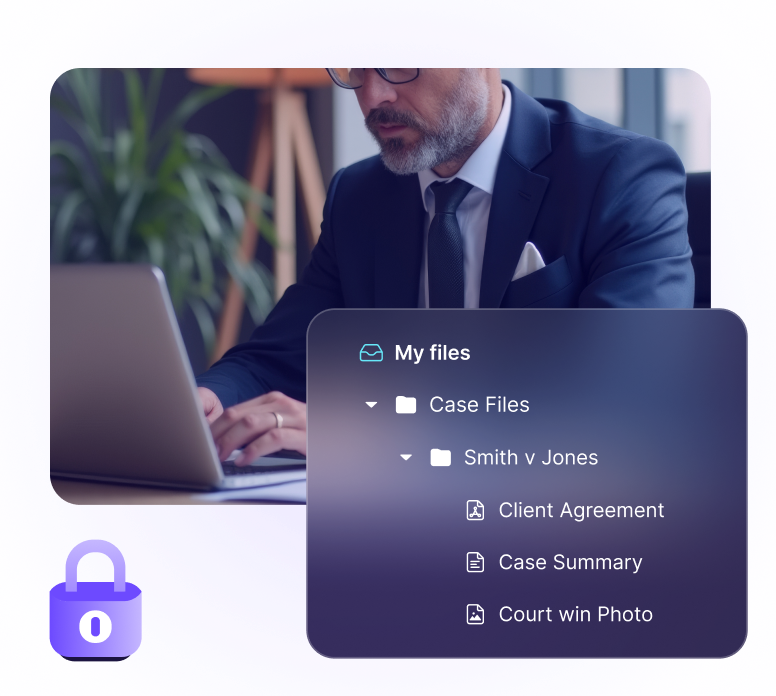
Proton Drive protects your team with end-to-end encryption. Your files remain protected at all times, and only you control the encryption keys, so Proton never has access to your content. Even in the unlikely event of a data breach, your files remain protected.
2. Use strong access controls
You should be able to define precisely who can access your data across your organization — whether that’s an internal employee, a contractor, or an external partner — and easily adjust or revoke that access as roles change.
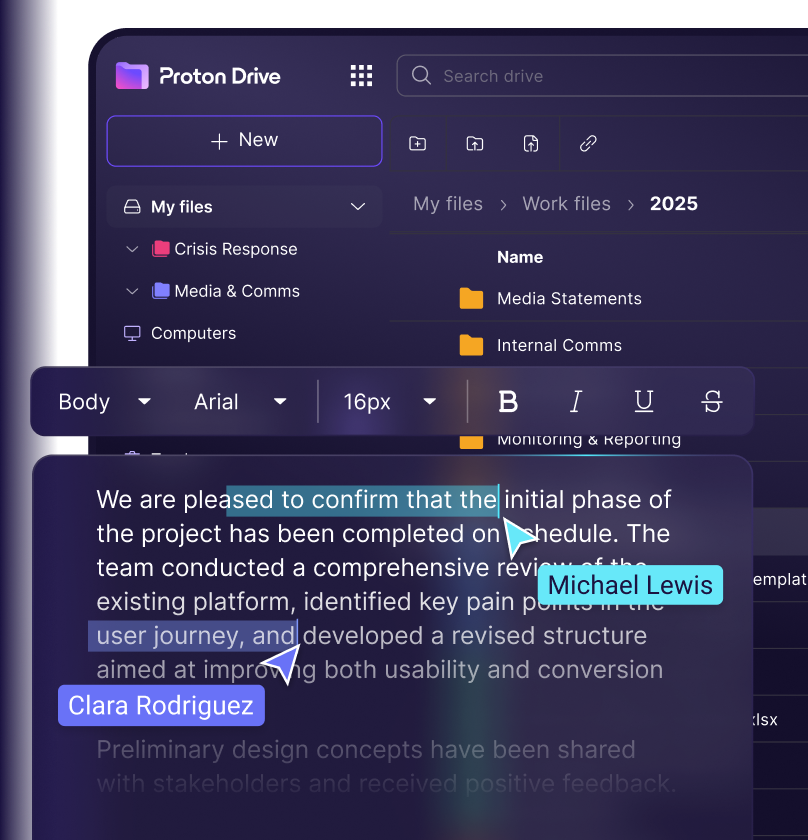
With Proton Drive, you can securely share files inside and outside your team using email invitations or secure links protected with passwords and expiration dates, giving you full control over how long access remains active and who can use it.
You can set roles such as view-only or edit for each person, so they only have the level of access needed. Everything shared is visible in one central space, allowing you to easily review, update, or revoke access anytime.
3. Recover deleted files or previous file versions
A secure cloud solution should make it easy to restore your data when things go wrong, so your team can get back on track quickly.
In Proton Drive, any files you delete are moved to Trash and remain there until you choose to permanently remove them — or recover them if you change your mind.
Plus, Drive keeps a detailed version history for all files for up to 10 years. So if you or a team member accidentally overwrites a file (or priorities simply change), you can review older versions, see when each one was uploaded and by whom, and restore one you need.
4. Enforce two-factor authentication
Your organization’s security is only as strong as its weakest account. 2FA adds stronger protection to your team accounts by requiring a second form of verification before access is granted, such as a code from an authentication app or a security key.
Proton Drive for Business allows organization admins to monitor and enforce 2FA across their teams. You can see who has enabled it, send reminders to those who haven't, and require 2FA for administrators or all members.
5. Monitor team activity for suspicious behavior
A cloud security solution should continuously monitor your environment and flag anything that looks out of the ordinary, giving your incident response team time to spot potential threats early and take action before they escalate.
Activity monitoring in Proton Drive for Business gives your team visibility into how accounts are being used, logging events such as failed login attempts, changes in user activity, and access patterns.
Plus, you can use Proton Sentinel to protect high-risk accounts. It’s an advanced security feature that uses AI and human analysis to identify and stop suspicious login behavior.
How Proton supports your team’s cloud data privacy and security
Store, share, and collaborate on business files with encrypted cloud storage, access controls, and version history.
Send secure email and attachments to make internal and external communications private and secure.
Plan and coordinate work while keeping meeting details, participants, and sensitive information private.
Protect your organization’s network and secure remote access by encrypting internet traffic.
Protect access to key business tools by managing credentials with an end-to-end encrypted password manager.
Start protecting your business data
Why choose Proton for your cloud data security and privacy
All Proton apps work together to protect your cloud environment, guided by shared core principles of security, privacy, and transparency.
Compliance that builds trust
Proton meets the strict standards set by global regulations and information security frameworks such as GDPR, HIPAA, SOC 2 Type II, and ISO 27001, safeguarding sensitive information while maintaining the trust of your customers and partners.
Transparency and audits
All Proton apps are open source, meaning our code is publicly available for anyone to verify our security model, so you don’t have to trust us on our word alone. Plus, our apps are regularly audited by independent security experts.
Swiss privacy protections
Since Proton is based in Switzerland, your data benefits from strict legal protections. It is securely stored in EU data centers and remains beyond the reach of the data-collecting models used by Big Tech.
Long-term privacy
Proton is mainly controlled by the nonprofit Proton Foundation, not private investors or large corporations. Our long-term decisions are always guided by our mission to protect privacy and security, rather than by the need to maximize profits.
Protect your business data with Proton Drive for Business
Frequently asked questions about cloud data security
- What is the shared responsibility model in cloud data security?
- What is the difference between cloud security and cloud data security?
- What are the biggest threats to cloud data security?
- How does cloud storage support business data protection?