Secure every connected device with an enterprise-grade endpoint security VPN
Enable secure remote access
Block threats across your network
Ensure regulatory compliance

What is endpoint security?
Endpoint security refers to the practice of securing all user devices (also known as endpoints) that connect to your corporate network, including company laptops, phones, and BYOD devices. Securing each endpoint is crucial as they are potential entry points for cyberattacks.
Endpoint security is enforced through the use of cybersecurity software. An endpoint security VPN provides an essential foundation for endpoint security. VPNs encrypt all connections from every device to your network, ensuring secure access for employees, no matter where they may be, while protecting them and your network from compromise.

Common endpoint security challenges
The rise of remote work and flexible device policies means businesses have more devices to secure than ever. With these changes in workforce practices, securing endpoints poses new challenges.
Personal devices accessing company resources
If your BYOD policy doesn’t require managed profiles, your IT team can’t enforce security policies or ensure devices are up to date and secure. These devices can still connect to company resources, creating a potential attack vector.
Unsecured networks and remote connections
Employees work from offices, co-working spaces, their homes, airports — and more. Most networks lack enterprise-grade security, and WiFi in public places is notoriously insecure. Open and weak networks provide attackers an entry point to intercept data and access your systems
Mixed device types and operating systems
MacBooks, iPhones, Android phones, and Windows PCs are just some of the devices your employees are likely using. Each has its own operating system, security settings, and unique vulnerabilities. Maintaining consistent protection across devices is a major challenge.
Lack of endpoint connection visibility
Without proper endpoint security management, your IT team may not be able to manage all the devices accessing your network or identify outdated software and risky behavior before they put your network at risk.
Enforcing compliance requirements
GDPR, HIPAA, and other regulations require you to protect customer data on every device that accesses it. A single breach through an unsecured endpoint can result in massive fines and reputation damage.
Proton VPN features for endpoint security management
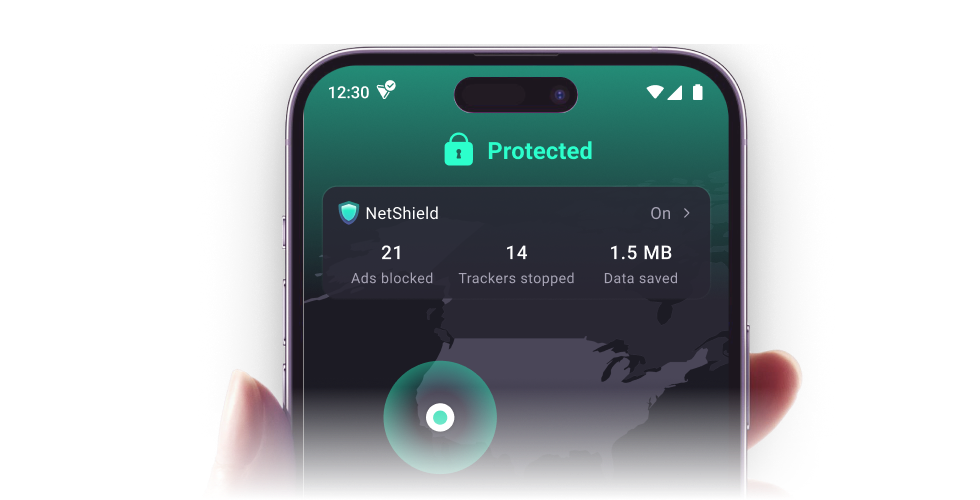
Secure all devices on your network
Proton VPN offers multi-platform support with easy-to-use apps and browser extensions. Employees can securely connect their devices while protecting company resources. Each team member can connect up to 10 devices at once.
Protection on any network
Whether your team connects from the office, at the airport, or anywhere in between, Proton VPN fully encrypts all traffic from connected devices. No one can intercept your company data.
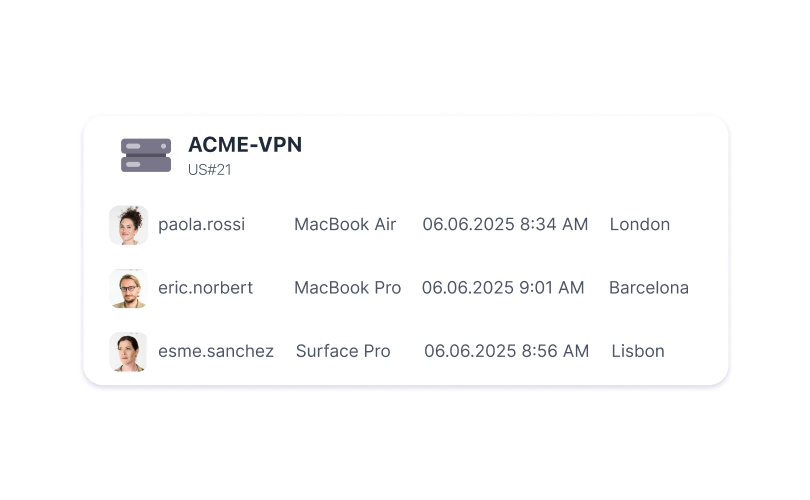
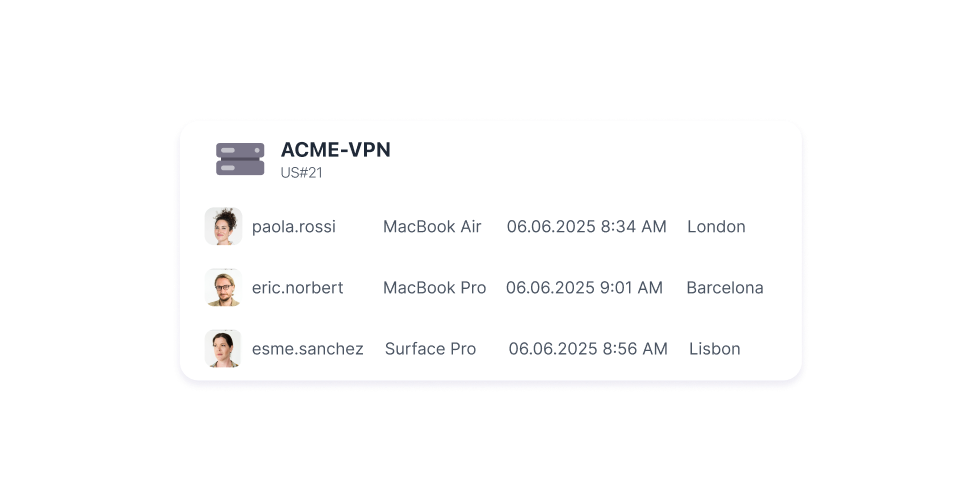
Complete endpoint visibility
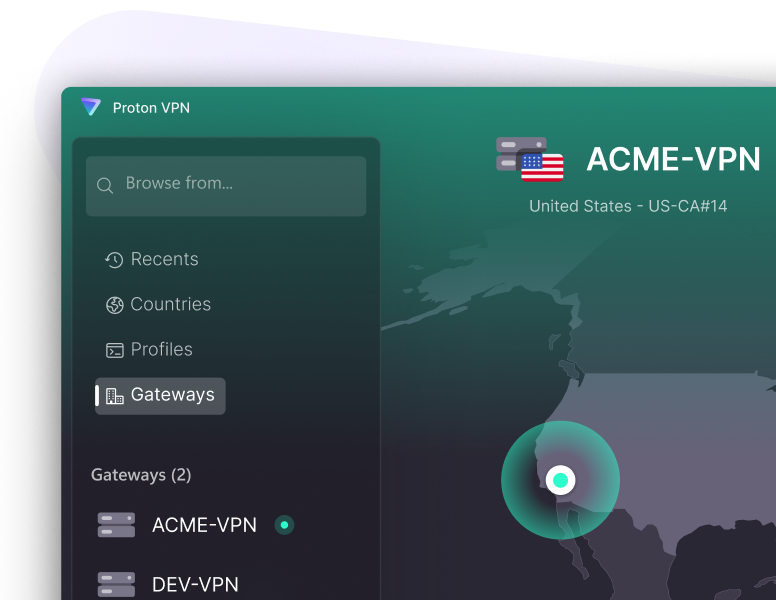
Monitor all VPN connections through a centralized admin dashboard. See which devices are connected, track usage patterns, and manage access permissions.
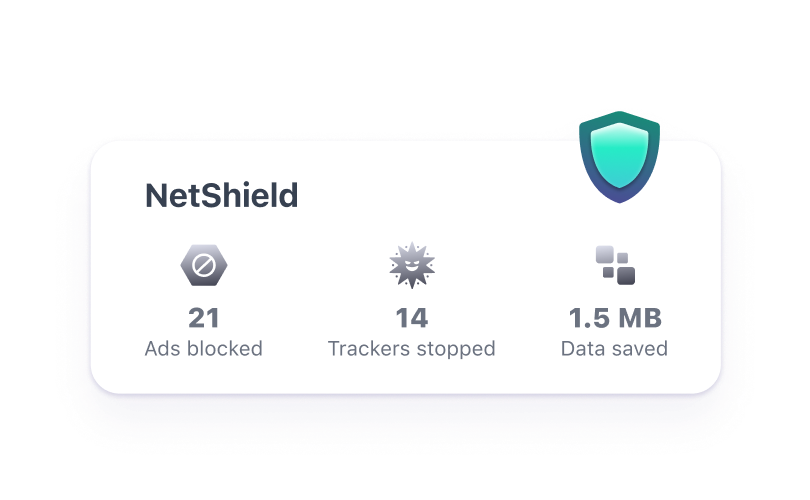
Advanced threat protection
Built-in NetShield ad-blocker prevents malware, trackers, and malicious ads from compromising devices. Proton VPN also has a built-in kill switch to keep IP addresses private even if the connection drops.
Enforce stronger authentication
For added security, easily enable two-factor authentication or single sign-on across your organization. This way, you can ensure only authorized users have access to your network.
How to secure endpoints with a VPN
Sign up for Proton VPN for Business
Choose a plan that fits your business needs.

Deploy across your team
Add employees and have them install Proton VPN on their devices.
Connect to a VPN server
When employees connect to the VPN, their device connections are instantly encrypted.
Thousands of businesses and privacy experts trust Proton VPN
30k+
Finance and technology professionals
10k+
Growing startups
15k+
Non-profit organizations
20+
EU Government Organizations out of over 80
+100 million
Accounts
Frequently asked questions about endpoint security
- How many endpoints can I protect with Proton VPN?
- How quickly can I deploy Proton VPN across endpoints?
- Can employees install Proton VPN on BYOD or personal devices?