Data breaches are the most common way for your email address to be leaked on the internet. This can lead to it appearing in online forums, on the dark web, and other public spaces. It takes an average of 277 days to identify and contain a breach according to a 2022 IBM report(new window), which means it could be nine months before you’re even aware attackers have your personal data. This poses a serious threat to your online privacy and security.
The only way to limit the impact of an email leak is to regularly check if your personal data has been compromised. In this article, we show you how to check if your email has been leaked and what you can do about it.
- What happens if your email is leaked?
- How to check for an email leak
- How to protect yourself from email leaks
- Choose a secure email provider
What happens if your email is leaked?
Personal data exposed in data breaches appears on the dark web all the time, causing a host of problems for victims. Here’s what could happen if cybercriminals got a hold of your email and password.
Increased spam and phishing emails
One of the biggest warning signs that your email has been leaked is a surge of spam and phishing emails in your inbox. While most spam emails are merely annoying, phishing emails are more dangerous. Phishing scammers impersonate a legitimate sender, such as your credit card company or healthcare provider, to trick you into divulging personal information.
Another common trick is to impersonate the service that leaked your information. For example, Twitter leaked over 200 million emails(new window) in late 2022, and it’s very easy for attackers to include all the information necessary to make it look like a legitimate email from the service. Here, you can see an example of “spear phishing” attacks targeting Twitter users with verified accounts.
Thankfully, you can usually defend yourself against phishing scams with nothing more than a little common sense. Keep an eye out for odd-sounding phrases, closely inspect the email address of the person who sent you the message, and reach out to them via another channel to confirm that the email is legitimate.
If you suspect an email is a phishing attempt, do not open any links or attachments and report the email to your email provider immediately.
Account takeover attacks
If your email password was also leaked in a data breach, a hacker could take control of your email account in an account takeover attack. Often, they’ll use the information in your inbox to access other, more sensitive accounts, such as your online banking or social media accounts. They might even blackmail you using your emails or force you to pay a ransom to regain access to your accounts.
Identity theft
Another possible outcome of an email leak is identity theft. Identity theft occurs when a hacker abuses your personal data to fool other people and organizations into thinking they are you. They might:
- Sign up for new subscriptions and contracts in your name
- Apply for new credit cards, loans, and bank accounts with your details
- Make fraudulent purchases
- Claim to be you and ask your friends and family for money
- Commit crimes using your details
Identity theft has devastating consequences — it can seriously damage your career and reputation and even leave you with a criminal record.
How to check for an email leak
Given how common data breaches are, it’s crucial to regularly monitor for signs your email has been leaked. A great way to do this is to search for your email address in the Have I Been Pwned (HIBP) database(new window), a website designed by web security consultant Troy Hunt to help people check if their personal information has been compromised. HIBP allows you to search for your email address, phone number, and password.
To search for your email address or phone number:
- Go to the Have I Been Pwned website(new window).
- Type your email address or phone number in the search bar and click pwned?

To search for your password:
- Go to the Have I Been Pwned website(new window).
- Click passwords located in the top navigation menu.
- Type your password in the search bar and click pwned?

How to interpret your results
If your email address and phone number haven’t been breached, you’ll see this message:

On the other hand, if you discover your information has been leaked, you’ll see this message instead:

If you find out you’re a victim of an email leak, take the following steps to protect yourself immediately.
How to protect yourself from email leaks
Change your passwords
The first thing you should do after discovering your email has been leaked is change the passwords on the affected accounts. This is assuming you’ve used a strong and unique password for all of your accounts. If you did use the same password for multiple accounts and one of those accounts was leaked or affected, then you should change that password everywhere you used it. This is one more reason you shouldn’t reuse passwords — it makes recovering from a breach more difficult.
We recommend using an open-source password manager to make it easier to remember multiple strong and unique passwords.
Password managers automatically generate and store complex passwords for each of your online accounts, making it difficult for hackers to crack them. All you need to do is remember a master password that allows you to sign in to your password manager.
Enable two-factor authentication
As you’re changing your email address(es) and passwords of your online account(s), you should also enable two-factor authentication (2FA) wherever possible. When you use 2FA, you defend your account against unauthorized access by requiring additional verification besides your password when you sign in. This is typically something you own, like a security key or a mobile device, or something that you are, such as your faceprint or fingerprint.
Security keys, also known as 2FA keys or hardware keys (for example, YubiKeys(new window)), are one of the most secure forms of 2FA. Unlike one-time codes generated by an authenticator app installed on your mobile device, security keys can’t be spoofed, aren’t time-bound, and don’t require access to a mobile device. Since they’re USB keys, you can easily add these security keys to your keyring and take them everywhere you go. Unfortunately, not all services support security keys.
Notify your contacts
You should inform your contacts that they might receive odd emails that appear to be from you to prevent them from being fooled by phishing attempts that use (or appear to use) your email address.
If you enabled 2FA in your email account before the leak and are confident that the hacker didn’t have access to your authenticator app or security key, you can skip this step.
Scrutinize your bank and credit card statements
You should also look over your bank and credit card statements to spot any unusual activity, such as charges you don’t recognize, large purchases, or even changes to your billing address. Sometimes criminals will also make small “test payments” of $1 or $2 before attempting to make bigger transactions.
If you uncover any suspicious activity, report it to your bank or credit card provider immediately. Usually, your bank or credit card company will provide you with a new bank account or credit card and close your old one.
Use email aliases
Using email aliases is a helpful strategy for preserving your online privacy, especially after an email leak. By using an email alias, you can keep your primary email address private and limit the amount of personal information you give out online. You can create email aliases in two ways:
- By adding a plus (+) sign: Add “+something” to your username. For example, if your email address is bobsmith@proton.me, your email alias could be bobsmith+finances@proton.me. This is known as email subaddressing.
- By creating a new email alias with a different username: You can create completely new email aliases for different online accounts.
Note: Not all email providers support these features. Proton Mail does, and we also offer +aliases for free.
Though convenient and practical, an attacker can easily extract your real email address from your email subaddress and use it in spam campaigns. If you have to use an email subaddress, make sure it doesn’t contain your real name.
Automatically generate unique email aliases
The better way to create new email aliases is to set them up individually. But given how many online accounts we use daily, it’s impossible to manually create new email aliases for all of them. It would also be a logistical nightmare to organize and manage that many inboxes.
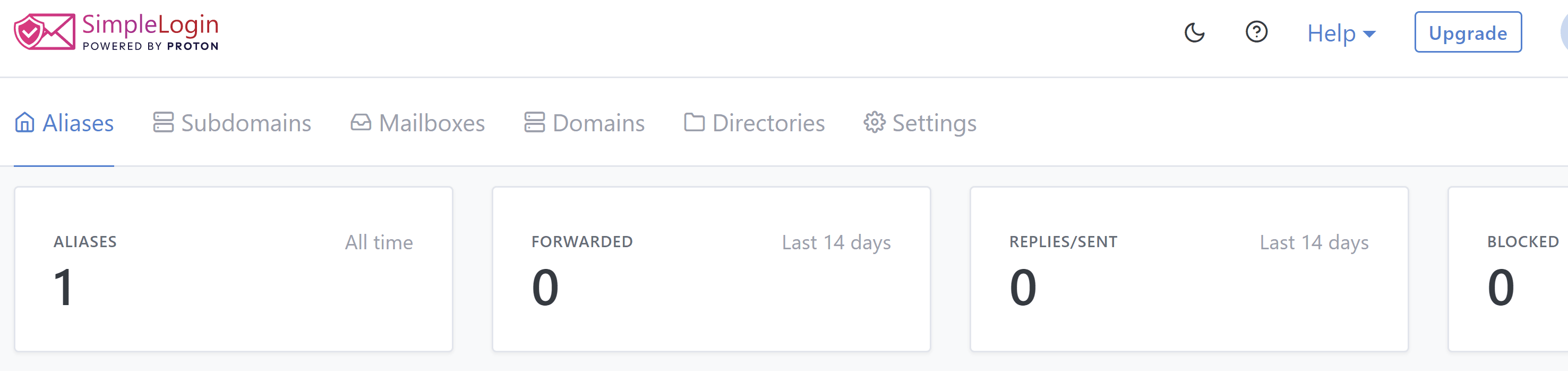
That’s why we recommend using an open-source email alias service, such as SimpleLogin by Proton(new window), to generate these addresses. SimpleLogin is a browser extension, web app, and mobile app that gives you anonymous email addresses whenever you sign up for an online account. Emails sent to your aliases are instantly forwarded to your inbox.
With SimpleLogin, you can create your own custom alias or let the software automatically generate a random one. If you decide you don’t want to use an alias anymore, you can simply delete it.
Don’t open suspicious links and attachments
Attackers often use phishing emails to trick you into revealing your personal data on fraudulent websites or installing malware(new window) on your computer. To stay safe, it’s best to only open emails and attachments from trusted senders and be cautious against emails that prompt you to take urgent action (like insisting you send money right away).
When you’re in doubt, contact the sender through an alternative method, such as calling their official helpline, and ask them to verify that they sent you an email. If you’re certain you’re dealing with a phishing email, report it to your email provider immediately.
Regularly monitor your email address(es) for leaks
Keeping a close eye on potential email leaks can go a long way in protecting your personal information and online identity. Regular monitoring helps you quickly detect and respond to any unusual activity and security incidents.
You can also use HIBP’s “Notify me” feature to receive notifications if your personal details are compromised in a data breach:
- Go to the Have I Been Pwned website(new window)
- Click Notify me located in the top navigation menu
- Enter your email address and select notify me of pwnage
Alternatively, you can follow HIBP’s Twitter account(new window) to keep track of all the latest data breaches. If you have a premium password manager, such as 1Password, you can also set up automatic leak detection updates where 1Password will regularly search the HIBP database and notify you if any of your login details appear.
Choose a secure email provider
Your email provider also plays a crucial role in preventing unauthorized access to your inbox. It’s responsible for implementing robust security measures that protect your email account from cyberthreats, such as hacking, phishing, and malware.
As the world’s largest encrypted email provider, our top priority at Proton is to protect your online privacy and empower you to take control of your data. When you use Proton Mail, you can enjoy the following security features:
- End-to-end encryption: No one besides you and your intended recipient can read your messages.
- Zero-access encryption: All data stored in our servers are fully encrypted. Even if a hacker breaches our servers, they won’t be able to read your emails.
- Additional email aliases: If you have a paid Proton Mail plan, you can create at least 10 additional email aliases. All emails sent to your aliases land in your inbox as usual.
- Block suspicious activity: Proton Mail’s security systems will temporarily lock your account if they detect suspicious behavior, such as someone attempting to hack into your inbox. Your account will be unlocked when you can prove your identity with a verification code (only sent to your recovery email address or phone number).
- Review security logs: In your Proton Mail account settings, you can review security logs and revoke access to any active session. You can also enable advanced logs that record the IP address for each event in the security logs.
- Strong spam filters: Our smart spam detection system automatically detects spam emails and directs them to your spam folder. For granular control, you can also add and remove email addresses from your Block List.
- Two-factor authentication (2FA) and security keys: You can use 2FA to secure your Proton Mail account. We support temporary codes generated by authenticator apps, YubiKey, and other U2F/FIDO2-compliant keys.
- Phishing protection: We provide anti-phishing protection with PhishGuard, a set of advanced features designed specifically to combat phishing.
- Anti-spoofing measures for custom domains: To protect you against spoofing attacks for your custom domain, we support SPF, DKIM, and DMARC.
By monitoring your email for leaks, implementing strong passwords, and utilizing the security features offered by Proton Mail, you can reduce the risk of email leaks and keep your personal data safe from cyberthreats.
If you’d like to support our mission of building a better, more private internet, consider signing up for a free Proton Mail account.







