Your online data is valuable. While it might feel like you’re browsing the web for free, you’re actually paying marketing companies with your personal information. Often, even when you pay for services, these companies still collect and profit from your data.
For example, when you search for products online, you are tracked by companies that use this information to show you similar products in ads. Social media marketers analyze your likes, shares, and how long you look at certain posts to build a detailed profile of what you find appealing.
This collection of data not only threatens your privacy but has a broader social impact, like influencing elections and what people think about issues.
Although surveillance capitalism has become the internet’s dominant business model, there are practical ways to protect your information online and defend your data privacy.
How to protect your personal information online
1. Use secure cloud storage

Many people use cloud storage services like Google Drive or Microsoft OneDrive to keep digital copies of private documents. These Big Tech companies don’t use end-to-end encryption (E2EE), so they can always access your data and it could be more vulnerable to a data breach. If you don’t feel comfortable with that level of exposure, Proton Drive offers a safer alternative for storing your files online.
2. Create secure passwords

Many people use simple and common passwords(new window), such as password or 123456, which can be easily guessed by attackers. A strong password avoids dictionary words and predictable patterns. It’s usually long and contains a random mix of letters, numbers, and special characters. This complexity makes it almost impossible for someone to discover your passwords through brute force or dictionary attacks.
You should create unique secure passwords for each account using a reliable password manager like Proton Pass. Even if a service you use suffers a data breach, the hacker won’t be able to use your distinct password on other websites (credential stuffing).
3. Set up 2FA

Two-factor authentication (2FA) increases the security of your accounts by requiring at least two forms of verification, such as your account password and a time-based one-time password (TOTP). Even if someone knows your account password, they still can’t get access without the second factor.
Moreover, if you get a 2FA notification that you didn’t request, it’s a clear warning that someone is trying to access your account, so you can quickly change your password. You can easily enable 2FA for all your accounts that offer it using our built-in authenticator in Proton Pass.
4. Use a VPN

If you need to use public WiFi(new window), a virtual private network (VPN)(new window) service will secure your connection by encrypting all data that travels between your device and the internet. If a cyber-criminal manages to intercept your network traffic, they would not be able to read or use the information.
Additionally, by replacing your real IP address(new window) with the one of the VPN server, a VPN improves your privacy by preventing ISPs and advertisers from tracking your physical location and building a detailed profile of your online interests, habits, and behaviors.
If you live in or travel to countries with strict internet restrictions, a trustworthy VPN like Proton VPN helps you bypass censorship(new window) and avoid surveillance by hiding your online activities from ISPs or governments.
5. Monitor your financial accounts

Regularly checking your bank statements and online accounts helps you notice patterns that might indicate someone has gained unauthorized access to your accounts via identity theft. This could include small, seemingly insignificant transactions that are often a test by fraudsters before making larger withdrawals. For example, you could use a credit monitoring service(new window).
6. Limit the information you share online

The less personal information you reveal on the internet, the fewer opportunities cyber-criminals have to steal your data for scams, doxing, or social engineering attacks. This also prevents advertisers and data brokers from collecting details about you.
When creating or updating online profiles, provide only the mandatory information and skip the optional fields asking for details that could be used to track or impersonate you.
Plus, you should avoid posting personal information on social media, such as your home address, phone number, birthday, vacation plans, and photos that reveal sensitive information.
While online quizzes and surveys can be fun, these can be a front for collecting personal details that are then sold to advertisers or worse.
7. Use a secure calendar
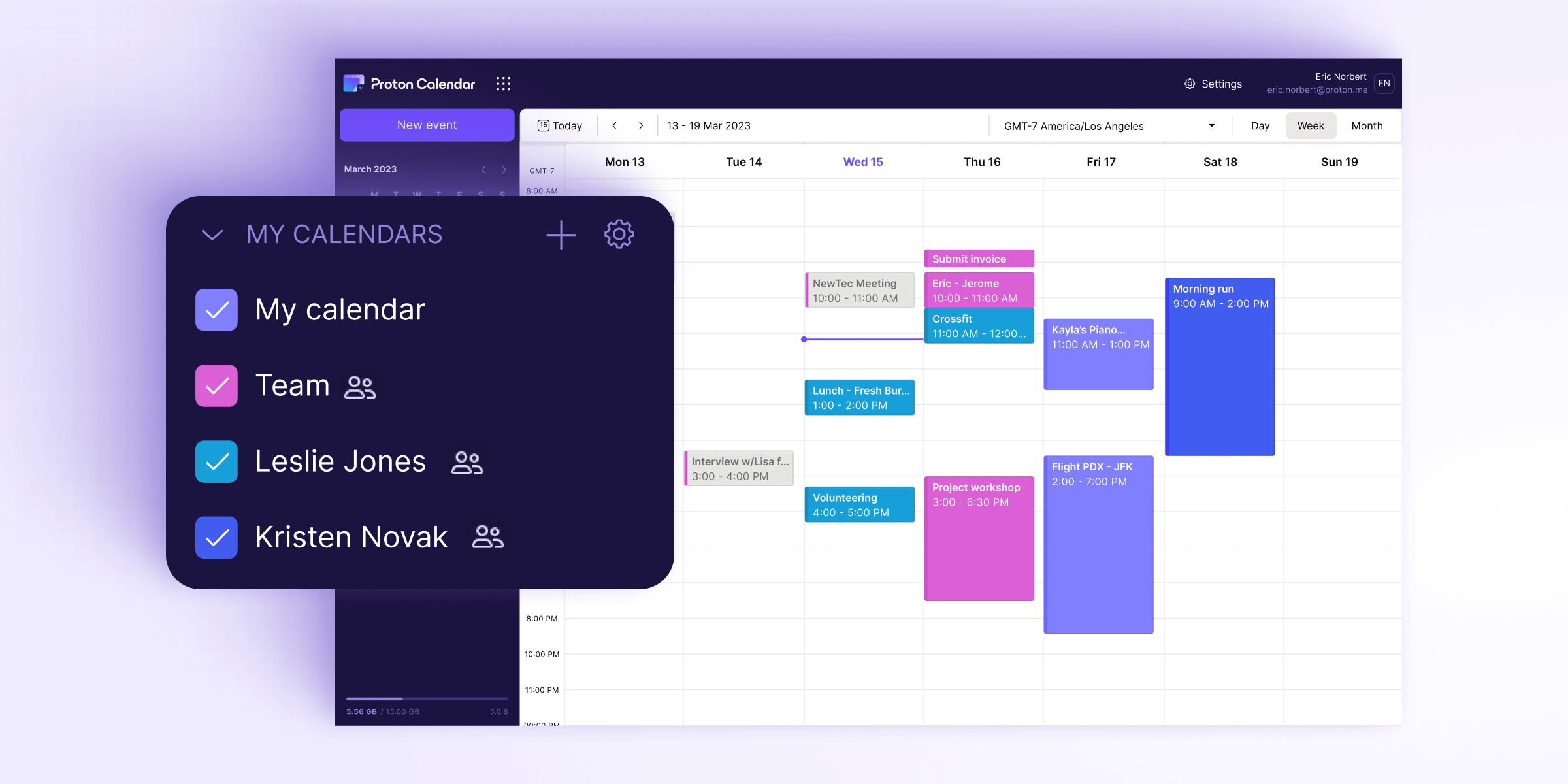
If you use a calendar app to organize your schedule, make sure to check the privacy settings and limit who can view your appointments to safeguard your personal information. Furthermore, it should offer strong encryption to enhance your security against hackers.
Some calendar services like Google Calendar collect and analyze your data. If you value your privacy and security, Proton Calendar provides end-to-end encryption and doesn’t use your data for commercial gain.
8. Monitor the web for data leaks

You can use dedicated tools like Dark Web Monitoring to scan the internet for data leaks and get notifications about compromised personal information, such as your email addresses, passwords, date of birth, phone numbers, government IDs, medical information, or financial details.
9. Switch to a privacy-focused browser

Privacy-first browsers like Mozilla Firefox or Brave collect minimal data about you and have built-in features to block trackers(new window), ads, and third-party cookies that collect your data.
Additionally, you should consider browser compartmentalization to keep your data separate and eliminate tracking across websites. For example, you can use a browser with strict privacy settings and no third-party extensions for sensitive activities like banking or shopping, and use another browser for daily activities with lower privacy risks, like reading news or watching videos.
10. Be wary of phishing attacks

Always be careful with emails, messages, and websites that ask for personal information since it could be a scam or phishing attack. Never click links or download attachments from senders you don’t recognize or weren’t expecting. It’s best to visit an online service’s website directly to log in rather than clicking a link in an email or text message, which could be faked or point to malware.
Proton Mail provides advanced protection through PhishGuard, which alerts you of possible phishing attacks.
11. Send emails securely

Standard email services like Gmail use TLS encryption to protect emails during transmission. However, once the emails arrive at their servers, they are not end-to-end encrypted, which means Google can access your private contents for targeted advertising.
A privacy-first email service like Proton Mail uses both TLS and end-to-end encryption to ensure that only the sender and recipient can access the message contents.
12. Use private messaging services

While WhatsApp (owned by Meta) uses end-to-end encryption to protect your messages from eavesdroppers and other third parties, it can still access your metadata. Meta can’t read the messages you’re sending or receiving, but it can see who you’re talking to, when, how often, where you are, and what device you’re using.
You can protect your personal information online when communicating with friends and family by switching to more private messaging apps like Signal or Threema.
13. Update your software regularly

It’s important to periodically update your software, including your operating system, browsers, antivirus, VPN, and all other applications with internet access. For instance, if you haven’t used your desktop computer for a long time, you should run all updates before taking any further steps.
Software updates often include patches for security holes that have been discovered since the last update and which could be exploited to gain unauthorized access to your system and steal sensitive data.
What are threats to your online privacy?
Cyberthreats can take many forms, from ad trackers to hacking. Here are a few common threats:
- Identity theft: Cyber-criminals steal personal data like Social Security numbers, credit card details, and passwords to impersonate you. They might open accounts in your name, incur debts, or commit fraud, damaging your financial health and credit score.
- Privacy invasion: Details such as your residential address, phone number, and email address can be used for harassment or stalking, compromising your internet privacy.
- Social engineering: Attackers can use small pieces of personal information gathered from various sources online to build trust and manipulate you into disclosing more sensitive data.
- Data collection and profiling: Data brokers use your browsing habits and purchase history to create profiles for targeted advertising or to sell to third parties.
- Phishing attacks: Scammers may trick you into handing them over your personal information, often through fake websites or emails that mimic legitimate companies.
- Reputational damage: Sensitive or embarrassing information shared online can be used to harm your reputation, professionally or personally, if fallen into the wrong hands.
- Network vulnerabilities: Hackers could use your personal information to infiltrate networks, such as your workplace, to spread malware or steal more credentials.
Safeguard your digital data with Proton
Proton is trusted by millions of people who are concerned about their online privacy, including journalists and activists. We are headquartered in Switzerland, so your data is protected by strict privacy laws. All our apps are open source(new window) and independently audited.
Proton uses end-to-end encryption(new window) to protect your data from third parties, including ISPs, advertisers, and surveillance — not even us can see what you’re doing. You can access all Proton services with one account and use 2FA to improve your security. Our Sentinel high-security program alerts you to potential threats to prevent account takeover.
We offer an encrypted ecosystem designed to protect your data from surveillance and breaches. By using our services, you can safeguard your personal information across various aspects of your digital life, including email, calendar, cloud storage, passwords, and internet connection(new window).
For example, Proton Drive is a secure cloud storage solution for storing sensitive files, such as financial documents and personal photos, making backups, and safely sharing files with end-to-end encryption. It’s a great first step to protect more of your personal information online, with a simple, free signup at Proton Drive.






