What is AES encryption?
AES in cryptography refers to Advanced Encryption Standard, a fast, efficient, and secure encryption algorithm certified by the US National Institute of Standards and Technology (NIST). It's a symmetric-key cipher that uses the same key to both encrypt and decrypt data. This is relatively quick, making it ideal for encrypting large amounts of data at rest.
Because of its strength and reliability, AES is one of the most popular and common types of encryption used in wireless network security, data and disk encryption, online payment systems, cloud storage, password management, and even government and military applications. The US government uses AES encryption to secure its classified information, which has contributed to its popularity.
Is the AES algorithm safe?
Yes. In 2000, after a very thorough(new window) and open selection process, NIST announced that AES (known until then as the Rijndael algorithm, created by Vincent Rijmen and Joan Daemen) would replace DES as its recommended(new window) “unclassified, publicly disclosed encryption algorithm capable of protecting sensitive government information well into the next century”.
According to NIST, all AES algorithm key lengths are deemed "sufficient" to protect classified information up to the "Secret" level. For "Top Secret" information, AES-192 or AES-256 is required.
Brute force attacks
The most basic form of attack possible on any encryption cipher is a brute force attack, which involves trying every possible key combination until the correct one is found.
Frontier(new window) is the world’s most powerful publicly known supercomputer. If it dedicated its entire output to brute forcing AES-128, it would still require the order of 10–12 trillion years to exhaust all possible combinations for AES-128. This is far longer than the age of the universe. So even at its lower bit sizes, AES is highly resistant to brute force attacks from conventional computers.
AES-256 is 340 billion-billion-billion-billion (2¹²⁸) times harder to brute force than AES-128.
While Grover's algorithm(new window) theoretically reduces the security of symmetric keys by half against quantum threats(new window), they are still relatively quantum resistant, especially when using a 256-bit key.
Key attacks
Over the years, a number of theoretical attacks on AES keys have been published by cryptographers, but all of these are either unworkable in practice, or are only effective on AES implementations that use a reduced number of rounds (see below).
The most successful attempt was the theoretical biclique attack(new window) published in 2011 that can reduce the time needed to brute force AES by a factor of four. However, it would still require billions of years to brute force AES on any current or foreseeable computer hardware.
No known key attack is practical against properly implemented AES-128 or higher.
Side-channel attacks
A side-channel attack attempts to reduce the number of combinations required to make a successful brute force attack by looking for clues from the computer performing the encryption calculations. Clues can be gleaned by examining:
- Timing - how long a computer takes to perform an operation
- Electromagnetic leaks
- Audio cues
- Visual cues (picked up using a high-resolution camera).
Cache-timing attacks, in particular, have proven to be quite effective at successfully cracking AES. In the most notable example, researchers in 2016 were able to recover(new window) an AES-128 key using “only about 6 - 7 blocks of plaintext or ciphertext (theoretically even a single block would suffice)”.
However, a number of things can be done to mitigate against the threat of side-channel attacks:
- Properly implemented AES can prevent ways that data can be leaked.
- Hardware that integrates the AES instruction set further reduces the side-channel attack surface of AES.
- Randomization techniques can be used to disrupt the relationship between data protected by AES and any leaked data that could be collected using a side-channel attack.
In many cases, side-channel attacks require the attacker to have close proximity or physical access to the device as it decrypts data, although remote attacks are possible if malicious software is installed on a device, particularly in the case of timing attacks.
How AES works
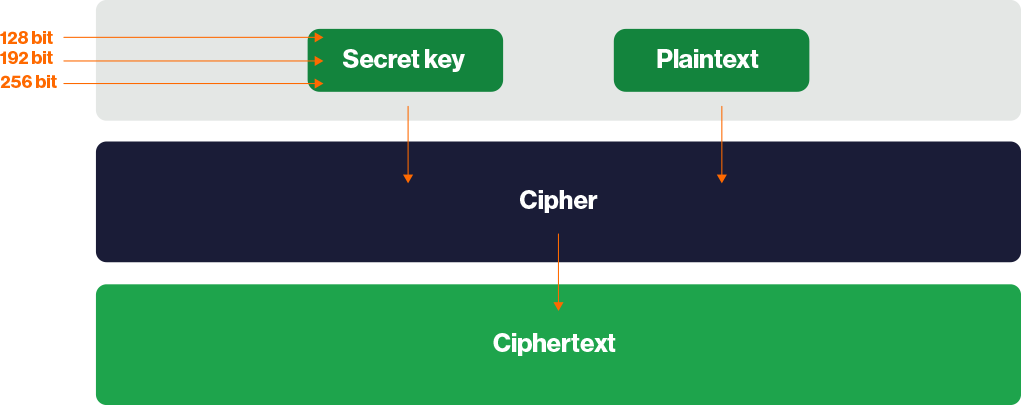
AES is a block cipher that encrypts and decrypts data in blocks of 128 bits using 128-bit, 192-bit, or 256-bit keys. As noted earlier, the same key is used for encrypting and decrypting data. AES using a 128-bit key is often referred to as AES-128, and similarly for AES-192 and AES-256.
Data is encrypted using multiple rounds, each of which consists of a series of mathematical operations.
The process starts with using Rijndael's key schedule algorithm to derive a series of new round keys from the original secret key. This is known as key expansion.
Each round then consists of one or more (or a combination) of the following operations:
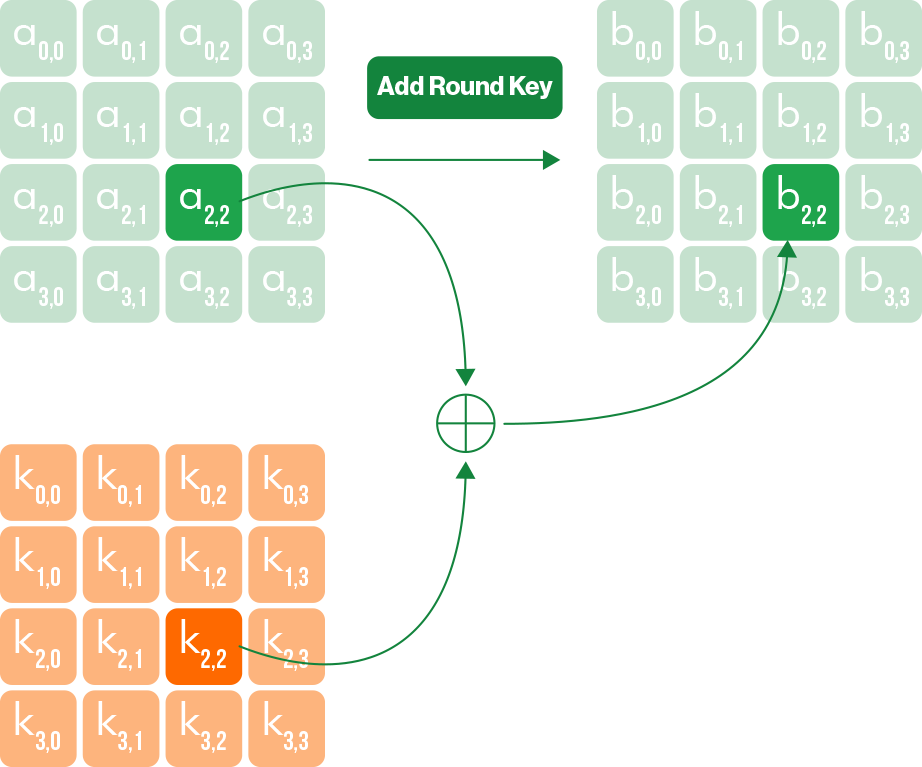
1. Add RoundKey: An XOR operation(new window) is performed to combine the data to be encrypted (the ciphertext) with each round key.
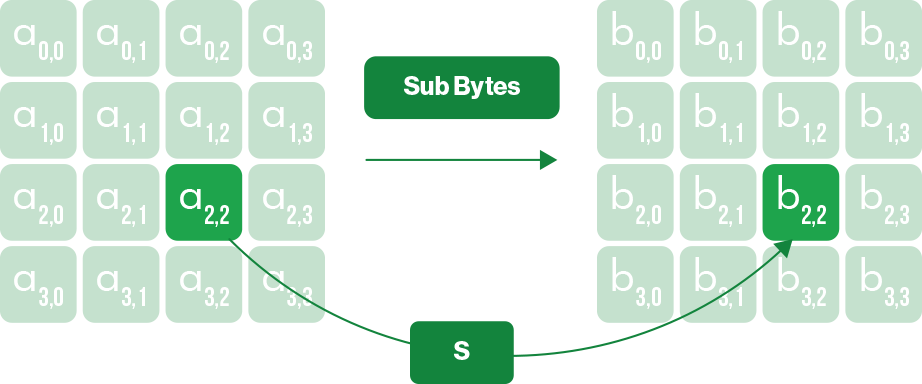
2. Sub Bytes: A substitution table is used to further mix up the data. Think, in principle, of the simple substitution ciphers you used as a child where you substituted each letter in a message for one a set number of later in the alphabet.
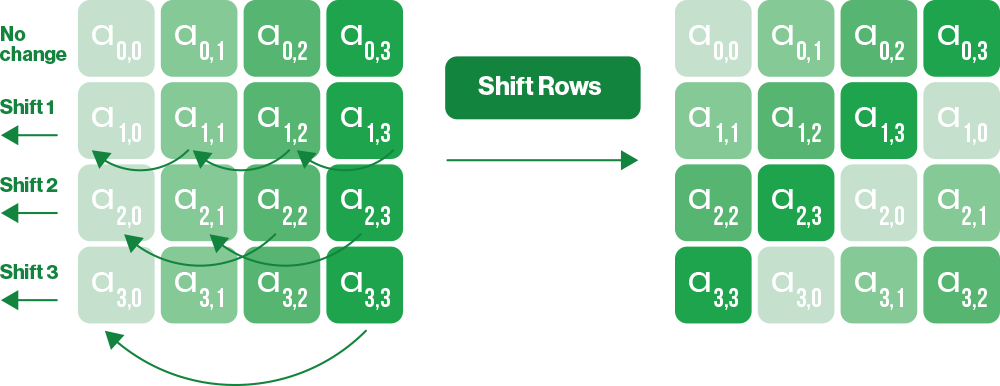
3. Shift Rows: Each 128-bit bock of data consists of a 16-bit 4x4 block. This operation shifts each byte in a block row by a certain offset to the left.
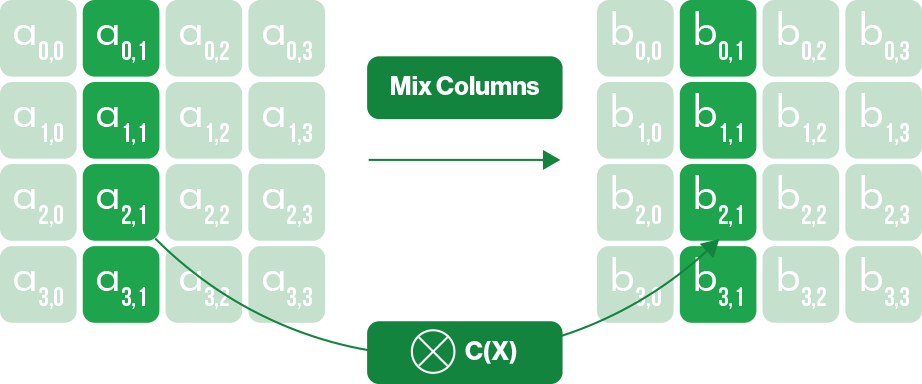
4. MixColumns: An additional invertible linear transformation is performed on each column in the block.
This series of transformations constitutes one round, which is then repeated on the data for a specific number of rounds, depending on the key size:
- AES-128 — 10 rounds
- AES-192 — 12 rounds
- AES 256 — 14 rounds
To decrypt data, all the steps used to encrypt it are simply performed in reverse. This requires the original secret key to reverse the process using each inverse round key.
Why is AES-256 preferred to AES-192 or AES-128?
It would take longer than the age of the universe to brute force AES-128 given current and foreseeable technology. Legendary cryptographer Bruce Schneier has even argued(new window) that AES-128 might be stronger than AES-256 thanks to it having a stronger key schedule —the algorithm that calculates all the round keys from the original secret key.
Yet AES-256 has become the de facto gold standard for symmetric-key encryption. It is often (if somewhat controversially) viewed as the stronger choice because its larger key size signals added margin of security so that encrypted data will remain safe even if some way is found to dramatically weaken the algorithm. This argument has become stronger as the need for post-quantum resistance becomes more pressing.
AES-CBC vs AES-GCM
Until fairly recently, AES was usually used in cipher block chaining (CBC) mode, where each block of plaintext is XORed with the previous ciphertext block before being encrypted. When used in CBC mode, a HMAC(new window) hashing algorithm such as HMAC-SHA256 is required to verify the data.
It is increasingly common, however, for AES to be used in Galois/counter (GCM) mode, which uses the counter mode(new window) of encryption. The main advantage is that it uses the Galois field(new window) to verify data without the need for an outside algorithm. It is therefore more efficient than using a separate authentication algorithm that can have a high computational overhead.
Although AES-CBC with HMAC authentication is generally considered secure, CBC is potentially vulnerable to padding attacks(new window), such as POODLE(new window). GCM is not.
Hardware-accelerated AES
Most modern CPUs include Advanced Encryption Standard New Instructions (AES-NI(new window)), a set of hardware instructions that performs AES operations directly on the processor. This makes AES much faster and also helps prevent timing-based side-channel attacks because the operations happen inside the processor's secure execution units, so there are fewer observable timing variations for an attacker to exploit.
Proton and AES
We make extensive use of AES to secure Proton products:
Events and contacts are secured using AES-256 combined with ECC for the key exchange to ensure your privacy via end-to-end encryption.
Proton VPN focuses mainly on the fast, efficient WireGuard® VPN protocol (which uses ChaCha20), but OpenVPN connections use AES-256.
Proton Pass stores passwords, notes, identities, and other items inside your secure vault using AES-256.
Proton Drive encrypts all uploaded files end to end with AES-256 using ECC for key exchange. Proton Docs and Proton Sheets also use AES-256 with ECC-based key exchange, though their encryption implementation differs from Proton Drive’s general file-encryption scheme.
Proton Mail stores emails and attachments using AES-256 via the OpenPGP standard. Even your private key, which unlocks your emails, is encrypted with AES-256 before being stored on the server.
Proton Meet uses Messaging Layer Security (MLS) to encrypt audio, video, and chat messages, ensuring forward secrecy (PFS) and post-compromise security (PCS) for all communications. All meeting data is end-to-end encrypted using AES-256-GCM.
Mitigating AES encryption attacks
Security is only as strong as its weakest link, which is usually your password. This means social engineering schemes, phishing attacks, and keyloggers(new window) are also a threat to AES-encrypted data. So even when AES is used, you should take the following precautions:
- Use an encrypted password manager
- Use hardware security keys (such as YubiKey) for an extra layer of protection
- If you're part of an organization, perform regular staff security training to prevent phishing attacks
Take charge of your data
Proton was built to protect your data from the start. With end-to-end encryption, open-source apps, and independent audits, your information stays yours.
Frequently asked questions about AES encryption
- Which is better: AES vs. DES?
- Which is better: AES vs. RSA?
- How strong is AES security?