Encryption > Glossary > Perfect forward secrecy
What is perfect forward secrecy, and why does it matter?
Perfect forward secrecy ensures encrypted conversations stay private, even if encryption keys are compromised later.
Learn how it works, why it’s important for encryption, and how it’s used across the internet.

What is perfect forward secrecy?
Perfect forward secrecy (PFS, or forward secrecy) is a security feature in encryption systems that ensures past communications stay secure even if a long-term private key is later compromised.
Normally, encrypted systems use a secret cryptographic key that stays the same over a long period of time. If someone steals that key after the communication has already happened, they could potentially decrypt previously recorded communications.
Example: with and without forward secrecy
Imagine you’re working remotely and logging into your company’s old internal web portal through HTTPS to submit expense reports or personal payroll information. The system uses an older TLS configuration that doesn’t support perfect forward secrecy.
An attacker somewhere along the network path (for example, on public WiFi or a compromised router) records the encrypted traffic. They can’t read it at the time because it’s encrypted.
Months later, the company suffers a breach and the server’s long-term private encryption key leaks. Because the system didn’t use forward secrecy, the attacker can use that key to decrypt the previously recorded traffic, exposing the sensitive information you submitted earlier.
If the system had used forward secrecy, each session would have used temporary encryption keys that were later discarded, so a leaked server key would not have allowed an attacker to decrypt those past communications.
How does perfect forward secrecy work?
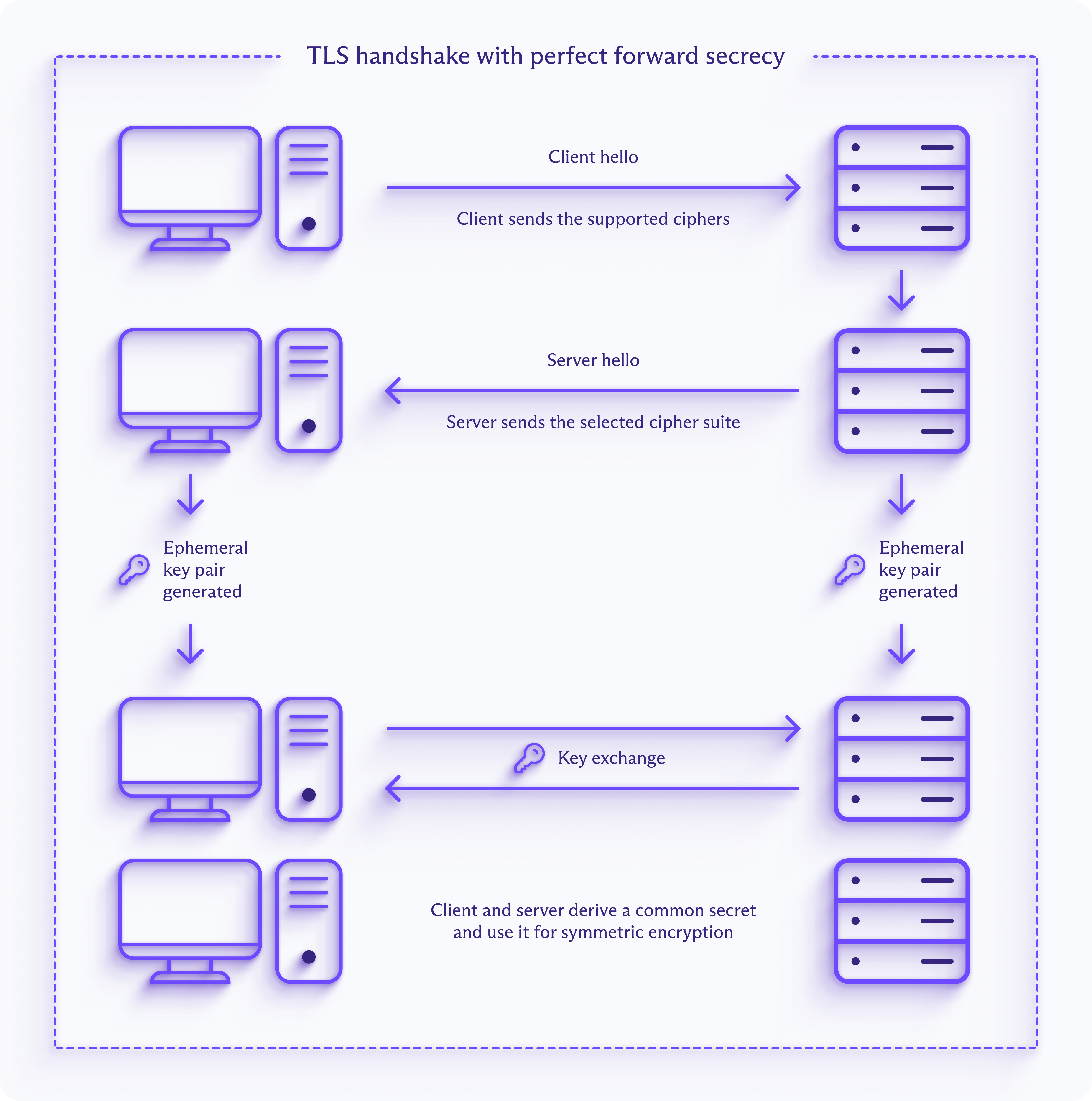
Perfect forward secrecy generates new, temporary session keys through ephemeral asymmetric key exchanges for each communication session. This is usually achieved using ephemeral key-exchange protocols such as Diffie–Hellman (DH) or its more efficient elliptic-curve counterpart, Elliptic Curve Diffie–Hellman (ECDH).
Elliptic Curve Diffie–Hellman is widely preferred today because it provides the same security as traditional Diffie–Hellman while using much smaller key sizes, improving performance. Traditional Diffie–Hellman relies on large prime numbers, and weak or reused parameter choices have been exploited(new window) in the past.
The diagram below shows a TLS handshake with perfect forward secrecy. Both the client and server generate ephemeral key pairs and exchange their public keys to derive a shared session secret. Because those keys are ephemeral, past sessions remain secure even if the server’s long-term key is later compromised.
Common uses of perfect forward secrecy
- Most secure websites (HTTPS), including online banking and shopping. HTTPS uses TLS to encrypt website connections, and TLS 1.3 includes forward secrecy.
- Messaging apps with end-to-end encryption, such as Signal and WhatsApp. They typically rotate keys frequently, sometimes per message.
- VPN(new window) apps that use modern VPN protocols such as WireGuard®(new window) and OpenVPN(new window) (with ephemeral Diffie–Hellman). Proton VPN supports forward secrecy(new window).
- SSH remote access tools like OpenSSH (built into macOS and most Linux systems) and PuTTY (a Windows SSH client).
- Email services usually encrypt emails while they are being sent between servers, often using TLS that support forward secrecy, so outsiders can’t easily intercept them. But the email provider itself may still be able to read stored emails unless they’re protected with encryption such as PGP.
Take charge of your data
Proton was built to protect your data from the start. With end-to-end encryption, open-source apps, and independent audits, your information stays yours.
Frequently asked questions
- Why is perfect forward secrecy important for encryption?
- How does Proton VPN use forward secrecy?
- How does Proton Mail handle encryption and forward secrecy?
Learn more about encryption