You can’t trace an email to a person. But email providers, ISPs, and law enforcement agencies may identify and track you through your emails if you don’t take steps to protect your privacy.
Whether to block spam, check for phishing, or simply investigate an unknown sender, you sometimes want to find out where an email came from. And many people may want to trace and track your emails — from big tech companies, marketers, and advertisers to law enforcement authorities.
We explain how emails can be traced and tracked and the steps you can take to keep your email private.
Why trace an email address?
Find an IP address from an email
Can you trace an email to a person?
Can you trace an email to a location?
How you can be tracked with email
“Free” email data collection
Email trackers
Stop emails from being tracked
Switch to private email
Use a VPN (or Tor)
Hide your email with aliases
Final thoughts
Why trace an email?
If you receive an email from an unfamiliar sender, there are several reasons why you might want to check where it came from:
- The message is spam and you want to find and block the sender.
- You suspect a phishing attack, so you check to see where the message originated.
- You’ve received an abusive message and want to trace the source.
Similarly, others may try to trace you and track your actions online through your emails:
- Most free email providers collect information linked to your identity to target you with ads.
- Marketing companies can track how you respond to their emails using trackers in the messages you receive.
- Governments and law enforcement agencies may identify and track you by the emails you send.
Anyone can create a fake email address and put any name in the From field, so how can you trace its origin?
Find an IP address from an email
The first place to start tracing an email is to look for the source IP address(new window), the string of numbers that identify devices connected to the internet. Check the email header, which contains information about the sender, receiver, subject, and time the message was sent. It also shows the IP address of the server the message was sent from.
For example, in Proton Mail, you can see an email’s header by clicking on the More menu (three horizontal dots) and selecting View headers.

Check the long code snippet (partly shown below). You can find the email’s source IP address in the first Received field (as messages usually pass through multiple servers to get to you, you may see multiple Received fields). Here the IP address is 159.135.236.69.

The easiest way to find the IP address is to cut and paste the header into a message header analyzer like Messageheader(new window) or Email Header Analyzer.(new window)
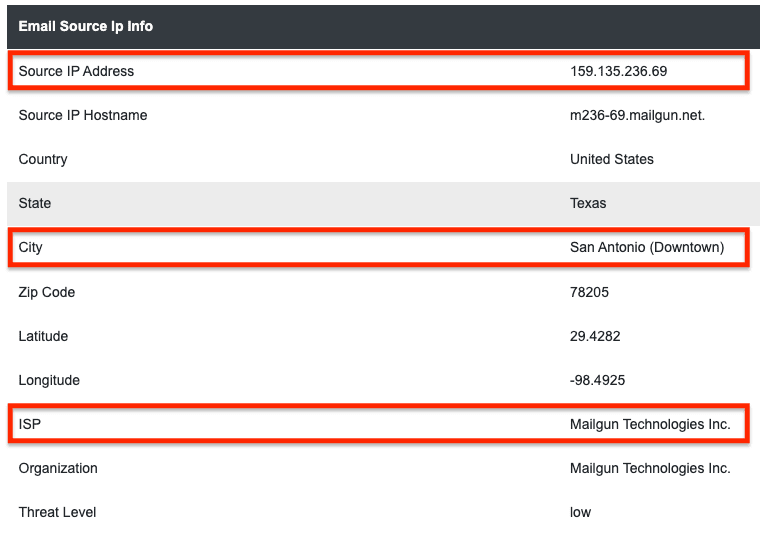
The IP address refers to the server the email was sent from — in this case, an email delivery service in San Antonio, Texas — but that address can’t be traced to a specific person.
Most popular web-based and mobile email apps don’t include the public IP addresses assigned to individuals in email headers. The email headers of messages sent from Proton Mail web and mobile apps don’t contain user IP addresses in the headers of sent mail.
But desktop email apps that use SMTP, like Outlook or Thunderbird, may include the originating IP address in the header. However, this IP address can’t be traced to an individual without further investigation (see how you can be traced below).
In short, the IP addresses in emails may give you a clue as to where the email originated. If you see it’s from an unknown or suspicious source, you can block future emails from that sender.
Learn how to block unwanted emails in Proton Mail
Can you trace an email to a person?
Email services, internet service providers (ISPs), and law-enforcement agencies may be able to identify you from your public IP address and other metadata(new window).
First, suppose you sign up for a free email service, like Gmail, using a mobile number or other personally identifiable information. In that case, the provider will obviously be able to trace you. But even if you create an account with only fake personal details, Google may piece together your real identity, as it logs your every move online (see how you’re tracked below).
Second, your ISP assigns a public IP address to your connected devices (like your home WiFi router), which is your address on the internet. Your mobile network operator does the same for your smartphone. Every website you visit or online service you use will refer to your device using your public IP address (unless you hide it — see below). So an email sent from an IP address can be traced to whoever is assigned that IP address at that time.
In this way, law enforcement agencies may request a user’s IP address and other metadata from email providers and ISPs to trace who’s behind an email, though it requires a court order in most countries.
Can you trace an email to a location?
The source IP address of an email may give you a rough indication of where an email originates from, for example, if it’s from a private email server (see how to find an IP address above). But often, the email will just show an email provider’s server. A Google server may be in Texas, but the user who sent the email could be anywhere.
However, if law enforcers get hold of your public IP address by investigating your email, that may indicate your location.
Most ISPs and mobile operators assign blocks of public IP addresses to devices in some geographical regions. So your public IP address may show which city or district you live in, but there’s no guarantee. An IP address can sometimes suggest you’re in a different area or even another country.
Of course, if you provide any personally identifiable information when signing up for an email account, your home location can be traced by your publicly available address details.
How you can be tracked with email
There are two main ways you can be tracked when using email:
- Big free email providers, like Gmail and Outlook, track your email and other online activity across the internet.
- Email marketers use tracking technology to monitor how you respond to emails.
“Free” email data collection
Most free email providers, like Gmail and Outlook, monitor every way you interact with your account. They track your activity online using browser and device fingerprinting, third-party cookies(new window), and other tracking technologies.
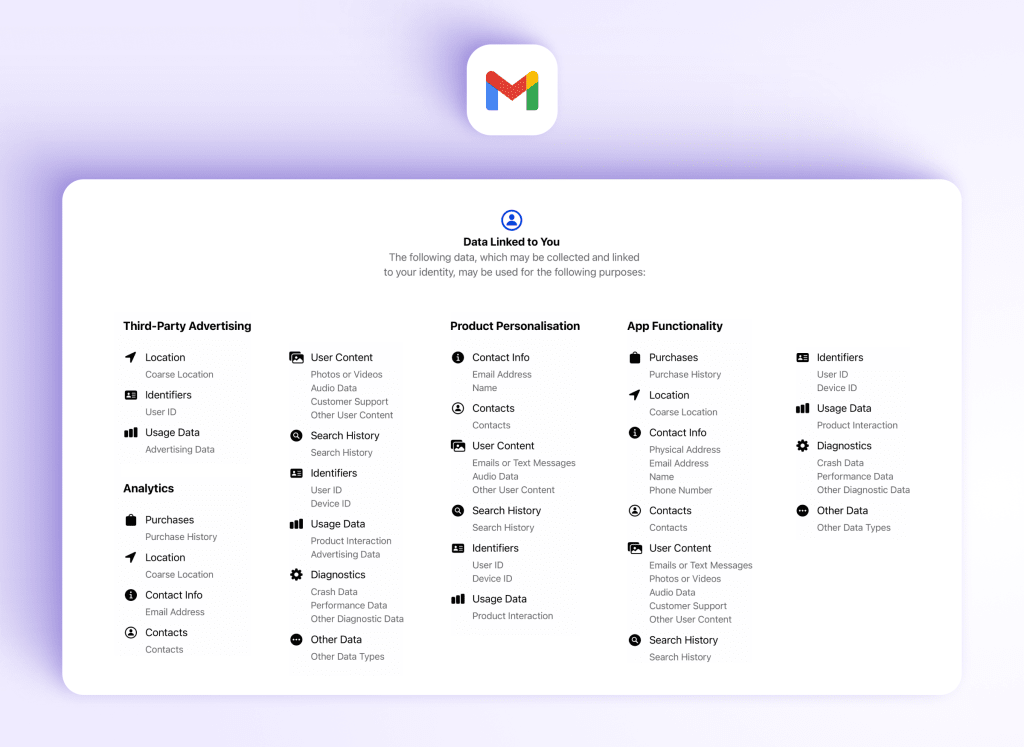
By aggregating your personal data across apps and services, Google can build a detailed profile of you to share with advertisers(new window). With Gmail and other “free” Google services, you don’t pay a subscription. Instead, you pay with the intimate details of your life.
To get an idea of the real cost of Gmail, take a look at its privacy label in Apple’s App Store showing the reams of personal data it collects from you:
Email trackers
Companies often include email trackers in messages to monitor your mail activity.
Email trackers typically work by embedding a tiny tracking pixel into an email linked to a remote image. When you open the message, the image is loaded from the source server, and sensitive information can be sent back to the sender, including:
- Which email you opened
- The date and time of opening
- The device type and operating system
Email trackers can even track your IP address and approximate location.
According to one study, over 70% of emails from mailing lists contain trackers(new window). But there are ways to block trackers and keep your email activity private.
Stop emails from being tracked
Here’s how to use email more privately and block trackers from invading your privacy.
Switch to private email
Get an end-to-end encrypted email account like Proton Mail.
At Proton, we don’t collect your personal data to target you with ads. All our funding comes from paying members of the Proton community, not from exploiting your personal data.

With Proton Mail, you can:
- Create a free account without sharing any personal information (though you may be asked to verify you’re a human)
- Keep your emails secure with end-to-end and zero-access encryption. No one but you can read them, not even Proton
- Send an end-to-end encrypted email to anyone using Password-protected Emails
- Block email tracking and hide your IP address with Proton’s enhanced tracking protection
- Set an expiration time for encrypted emails after which they automatically delete themselves from your recipient’s inbox
Learn more about what Proton Mail protects you from
Use a VPN (or Tor)
Keep your online activity private with a virtual private network (VPN) like Proton VPN(new window).
A good VPN hides your IP address from your ISP and keeps your online activity private. To protect your privacy while using email, you should only access your private email with a VPN.
If you need a greater degree of privacy, consider accessing Proton Mail with the Tor anonymity network.
Hide your email with aliases
Use email aliases, or additional email addresses, to hide your personal email address and protect your identity. You can create at least ten additional addresses with a Proton paid plan.
Or consider using an email aliasing service like SimpleLogin by Proton(new window). Creating anonymous aliases for different websites lets you keep your email address private and protect your inbox from spam and phishing.
Final thoughts
You may not be able to trace a single email to a person, but you can get an idea of where it came from its header.
However, email providers, ISPs, and law enforcement agencies can track down individuals from emails using their IP addresses and other metadata. And marketing companies can monitor how you respond to the emails you receive.
It’s impossible to guarantee 100% anonymity on the internet. But you can significantly reduce the chances of being traced and tracked by using Proton Mail, Proton VPN (or Tor), and aliases.
At Proton, our mission is to give everyone privacy and security online. Sign up for a free Proton Mail account, and you get encrypted Proton Calendar, Proton Drive, and Proton VPN included.
If you want to support our mission, sign up for a paid plan. Our Proton Unlimited plan includes 500 GB of encrypted storage, support for three custom domains, 15 addresses, and unlimited aliases. Stay secure!








